CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
HIPAA Modernization of Security Standards
HIPAA Modernization of Security Standards
The Health Insurance Portability and Accountability Act, better known (if not always spelled correctly) as HIPAA, was signed into law by President Bill Clinton in August 1996.
A lot has changed in the two decades since – in the ways consumers interact with health systems and the ways technology is transforming care delivery and the patient experience. So maybe it's time to give the privacy law a refresh, said the American Medical Informatics Association and the American Health Information Management Association.
WHY IT MATTERS
As access to personal health information is easier than ever, with smartphones now ubiquitous and apps and connected devices proliferating by the day, both AMIA and AHIMA have voiced support for HIPAA modernization.
In a joint appearance on Capitol Hill, in a presentation about unlocking data for patient empowerment, experts from the two groups highlighted how healthcare has a lot of catching up to do to serve a population used to online shopping, travel booking, review sites and more.
Webinar: The Future of Medicine: Protecting Privacy Without Impacting Quality of Care
Toward this vision of improved patient experience, AMIA and AHIMA said U.S. policymakers should take steps to update HIPAA to enable greater data access and portability – something that looks more likely than it did even a few months ago.
It could be done in a couple different ways, they said. First, potentially, by establishing a new concept of a health data set, with that HDS comprising all the clinical, biomedical and claims data maintained by a covered entity or business associate.
Another option is to revise HIPAA's existing "designated record set" definition, requiring certified health IT products to provide that amended DRS to patients digitally – enabling in a way that enables them to use and reuse their data.
They explained that a new definition for HDS would support individual HIPAA right of access and guide the future development of ONC's Certification Program so individuals could view, download, or transmit to a third party this information electronically and access this information via application programming interface.
Revising the existing DRS definition, meanwhile, offer more clarity and predictability for both providers and patients, AMIA and AHIMA said.
THE LARGER TREND
Even as the availability and maturity of consumer technology has improved, "more than two decades after Congress declared access a right guaranteed by law, patients continue to face barriers," said Dr. Thomas Payne, medical director, IT Services at UW Medicine. "We need a focused look at both the technical as well as social barriers."
AMIA and AHIMA called a broader conversation regarding consumer data privacy, and called on Congress to "extend the HIPAA individual right of access and amendment to non-HIPAA Covered Entities that manage individual health data, such as mHealth and health social media applications. The goal is uniformity of data access policy, regardless of covered entity, business associate, or other commercial status."
Moreover, the groups said regulators should clarify existing regulatory guidance related, for example, to third-party legal requests, such as those by lawyers looking for information without appropriate patient permissions.
ON THE RECORD
"Congress has long prioritized patients' right to access their data as a key lever to improve care, enable research, and empower patients to live healthy lifestyles," said Dr. Doug Fridsma, president and CEO and AMIA. "But enacting these policies into regulations and translating these regulations to practice has proven more difficult than Congress imagined."
"AHIMA's members are most aware of patient challenges in accessing their data as they operationalize the process for access across the healthcare landscape," said AHIMA CEO Wylecia Wiggs Harris, in a statement. "The language in HIPAA complicates these efforts in an electronic world."
Cyber Security: Information Data Protection
CyberSecOp assist clients with managing privacy risk while keeping thier existing controls as effective and efficient as possible to withstand a complex privacy risk environment. We focus on testing, and training based on common employee mistakes and remediate gaps in the process, eeping your systems in line with current regulations,
The revolution that has taken place over the past 20 years has had an impact on both consumers and enterprises. The devices and applications that millions of individuals use on a daily basis contain increasingly more complex information, within a constantly evolving technological environment. The growing digital innovation trends such as cloud computing, big data and the IoT create new opportunities to communicate and exchange information. However, this massive amount of confidential data must consequently be managed and secured efficiently and continuously.
How can a company guarantee the security of its data and of its users' data? What solutions are currently available on the market that can help enterprises optimize the management of information while maintaining their privacy?
CyberSecOp, an american base market leader in the Managed Security Service Provider industry, responds to the companies' need for security, offering a range of solutions and services designed to help customers identify cyber security risks in order to mitigate and monitor them over time.
Through its diverse solutions portfolio, CyberSecOp provides the right mix of technology, processes and sector-specific knowledge, supporting customers during the initial planning phase, from design to implementation, in order to identify the best solutions both in terms of process, as well as technology. The company’s strategic partnerships with key suppliers and expertise with market technologies guarantee customers a solution that provides effective operational coverage, on-premise or remote, with vertical expertise throughout the duration of the project and during the delivery of services.
Moreover, thanks to a Cyber Security Operations Center (CSOC), the delivery of timely services and continuous security monitoring are seamlessly integrated to reduce cyber security-related risks. The service is designed to offer the customer a growth-oriented path aimed at improving the company’s overall security position and risk level awareness.
The Industry 4.0 evolution and the arrival of the IoT have significantly increased the complexity and the level of risk to which all enterprises are subject, necessitating an efficient management of corporate security. In a changing environment characterized by increasing opportunities, while at the same time offset by an exponential increase in associated risks, the availability of CSOC services represents an essential guarantee of security.
MSSP Cybersecurity & Managed Detection and Response
MSSP Cybersecurity & Managed Detection and Response
Managed detection and response enables a proactive approach to security with its ability to detect and fully analyze threats and promptly respond to incidents. CyberSecOp Threat intelligence is one of the key aspects our security consultants used to help organizations make decisions on how to combat threats. Through managed detection and response, organizations can take advantage of the threat intelligence capabilities of security experts.
How Managed Detection and Response Provides Effective Threat Intelligence
Capture full visibility across your entire IT environment
Detect the most advanced threats (known and unknown) designed to bypass your traditional perimeter security controls, even when no malware is used
Expose threat actors currently hiding in your environment
Gain 24x7 monitoring by an advanced team of security experts that are specially trained to analyze advanced threats, determine the severity of any incidents and provide actionable guidance to remediate
Quickly elevate the alerts that matter most so you can focus limited resources where it matters most
Managed Detection and Response Service
Managed Detection and Response (MDR) is an all-encompassing cybersecurity service used to detect and respond to cyber-attacks. Using the best of signature, behavioral and anomaly detection capabilities, along with forensic investigation tools and threat intelligence, human analysts hunt, investigate and respond to known and unknown cyber threats in real time 24x7x365. Get Managed Detection and Response Services for your business www.cybersecop.com.
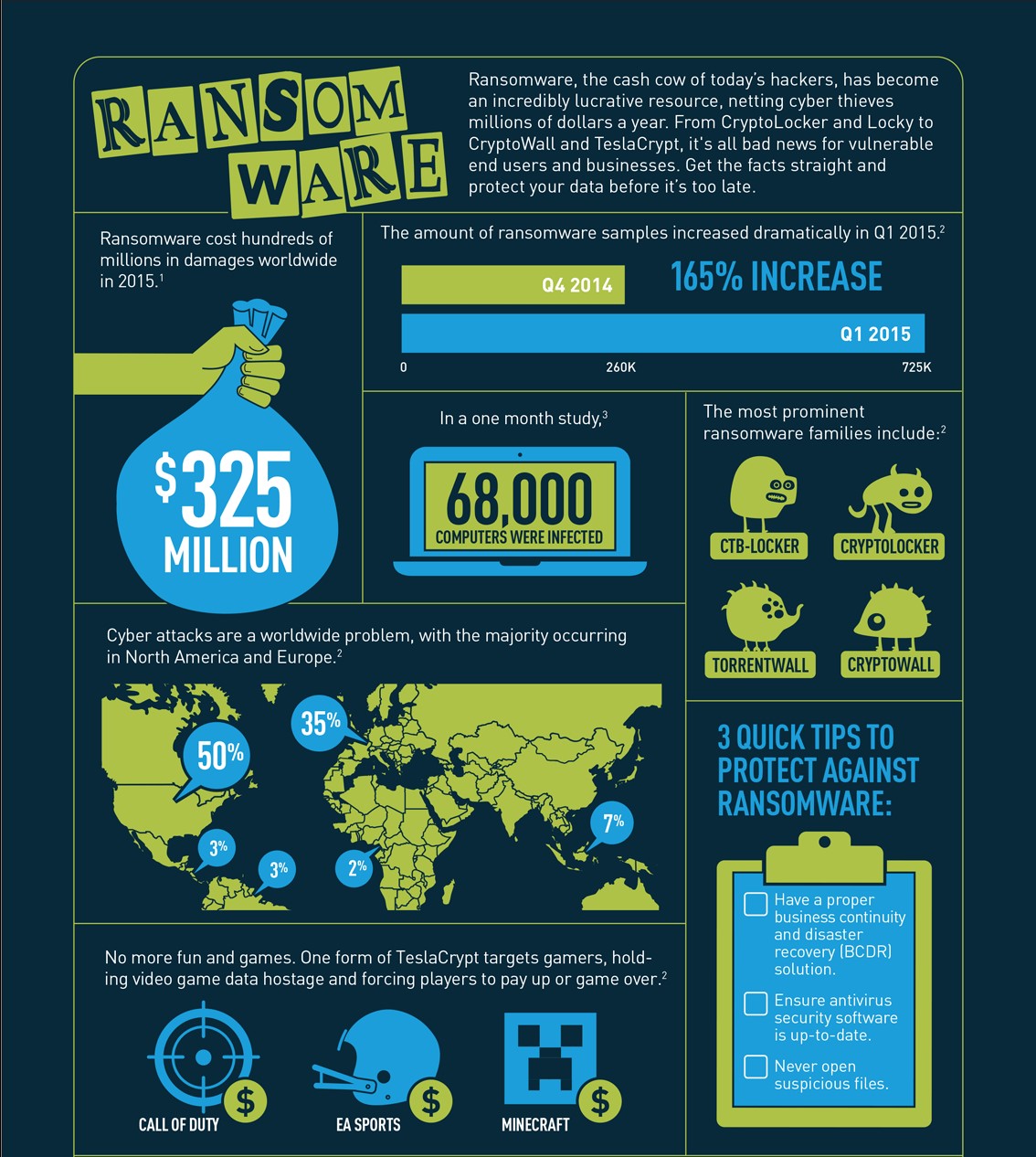
Ransomware Cyberattack - 92% of MSSPs Expect Ongoing Attacks
Ransomware is the leading cyberattack experienced by small and medium-sized businesses (SMBs), according to a survey of more than 2,400 managed service providers (MSSPs) conducted by data protection company Datto.
Datto’s State of the Channel Ransomware Report provides unique visibility into the ransomware epidemic from the perspective of the IT Channel and the SMB clients who are dealing with these infections on a daily basis. The report provides a wealth of detail on ransomware, including year-over-year trends, frequency, targets, impact, and recommendations for ensuring recovery and continuity in the face of the growing threat.
Key findings from Datto’s “State of the Channel Ransomware Report” included:
79 percent of MSSPs reported ransomware attacks against customers.
85 percent indicated that victims had antivirus software installed, 65 percent reported victims had email/spam filters installed and 29 percent reported victims used pop-up blockers.
89 percent are “highly concerned” about ransomware attacks.
92 percent predict the number of ransomware attacks will continue at current, or worse, rates.
MSPs ranked phishing emails as the top ransomware delivery method, followed by malicious websites, web ads and clickbait.
The average requested ransom for SMBs is roughly $4,300, while the average cost of downtime related to such an attack is approximately $46,800.
The number of MSPs reporting OS/iOS attacks increased by nearly 500 percent year over year in the first six months of 2018.
No single solution is guaranteed to prevent such attacks, Datto indicated. Conversely, SMBs require a multilayered approach to identify and stop ransomware attacks before they cause brand reputation damage, revenue loss and other problems.
How Can SMBs Address Ransomware Attacks?
CyberSecop offered the following recommendations to help SMBs safeguard their data and assets against such attacks:
Leverage business continuity and disaster recovery (BCDR) technology. BCDR technology won’t stop ransomware attacks; instead, it helps an SMB determine how to limit downtime and maintain operations despite a ransomware attack.
Provide cybersecurity training. By offering regular and mandatory cybersecurity training, an SMB can ensure all of its employees can identify and avoid potential phishing scams that otherwise lead to such an attack.
Employ a dedicated cybersecurity professional. It may be difficult for an SMB to hire a full-time cybersecurity professional. Fortunately, working with an MSSP allows an SMB to receive cybersecurity monitoring and other security services.
Data Breaches Ransomware and Cyber Attacks
Data Breaches Ransomware and Cyber Attacks
It’s unrealistic to think that you can completely avoid cyberattacks and data breaches, so it’s vital to have a proper data recovery plan in place. You can also tighten your defenses significantly by ensuring all of your network devices are properly configured, and by putting some thought into all of your potential network borders.
Data Recovery Capability
Do you have a proper backup plan in place? Have you ever tested it to see that it works? Disaster recovery is absolutely vital, but an alarming number of companies do not have an adequate system in place. A survey of 400 IT executives by IDG Research revealed that 40% rate their organizations’ ability to recover their operations in the event of disaster or disruption as “fair or poor.” Three out of four companies fail from a disaster recovery standpoint, according to the Disaster Recovery Preparedness Benchmark.
A successful malware attack can lead to altered data on all compromised machines and the full effects are often very difficult to determine. The option to roll back to a backup that predates the infection is vital. Backed up data must be encrypted and physically protected. It’s also important that a test team routinely checks a random sampling of system backups by restoring them and verifying data integrity.
Secure Configurations for Network Devices such as Firewalls, Routers, and Switches
The default configurations for network devices like firewalls, routers, and switches are all about ease of use and deployment. They aren’t designed with security in mind and they can be exploited by determined attackers. There’s also a risk that companies will create exceptions for business reasons and then fail to properly analyze the potential impact.
The 2015 Information Security Breaches Survey found that failure to keep technical configuration up to date was a factor in 19% of incidents. Attackers are skilled at seeking out vulnerable default settings and exploiting them. Organizations should have standardized secure configuration guidelines applied across devices. Security updates must be applied in a timely fashion.
You need to employ two-factor authentication and encrypted sessions when managing network devices, and engineers should use an isolated, dedicated machine without Internet access. It’s also important to use automated tools to monitor the network and track device configurations. Changes should be flagged and rule sets analyzed to ensure consistency.
Boundary Defense
When the French built the Maginot Line in World War II, a series of impregnable fortifications that extended along the border with Germany and beyond, it failed to protect them because the Germans invaded around the North end through neutral Belgium. There’s an important lesson there for security professionals: Attackers will often find weaknesses in perimeter systems and then pivot to get deeper into your territory.
They may gain access through a trusted partner, or possibly an extranet, while your defensive eye is focused on the Internet. Effective defenses are multi-layered systems of firewalls, proxies, and DMZ perimeter networks. You need to filter inbound and outbound traffic and take caution not to blur the boundaries between internal and external networks. Consider network-based IDS sensors and IPS devices to detect attacks and block bad traffic.
Segment your network and protect each sector with a proxy and firewall to limit access as far as possible. If you don’t have internal network protection, then intruders can get their hands on the keys to the kingdom by successfully breaching the outer defenses.
The real cost
A lot of businesses argue that they can’t afford a comprehensive disaster recovery plan, but they should really consider whether they can afford to lose all their data or be uncertain about its integrity. They may lack the expertise to ensure that network devices are securely configured, but attackers don’t lack the skills to exploit that. It’s understandably common to focus on the outer boundary of your network and forget about threats that come from unexpected directions or multiply internally, but it could prove costly indeed.
Compared to the cost of a data breach, all of these things are cheap and easy to set up
Cyber Insurance - Is a must have - you will need it
Cyber Insurance - Is a must have - you will need it.
It’s every healthcare organization’s nightmare to get the call that their data has been breached or hacked. As a result, many have turned to cyber insurance to protect assets and business operations.
As cyber policies and carriers lack a universal policy, there’s an even greater worst case scenario: An organization is breached, and the policy doesn’t cover what the leaders thought it did. Now, not only is the healthcare provider strapped with the burden of the breach, it wasted money on a useless cyber insurance policy.
To get a better grasp on how to choose the right policy, Healthcare IT News asked attorney Matthew Fisher, partner with Mirick O’Connell, and Jane Harper, Henry Ford Health System’s director of privacy and security risk management, to outline the biggest policy mistakes -- and how to avoid them.
Mistake #1: Rushing the process
When buying a policy, a carrier will provide a questionnaire that will evaluate your organization’s security posture, program, tools and policies. The biggest mistake is to rush the pre-policy process to see the rates and what the carrier will cover, explained Fisher.
Organizations need to be conservative with how they answer the questions, as “it could be a ground for denial, if you don’t have the policies you said you have in place,” said Fisher. “You have to make sure you’re not unintentionally misleading the insurance company when it comes to coverage.”
Often these questionnaires attempt to create a black and white policy and “it can be tough to answer correctly,” explained Fisher.
“Your ability to be as transparent and truthful upfront is critical to the nonpayment discussion,” said Harper. “If you tell the insurance company that you have everything in place and are compliant, if you tell them that and then you have an issue, and you weren’t truthful, it ends up being a legal battle.”
“When you submit your checklist that they have you fill out, meet with the underwriter to make sure you understand what you’ve documented,” she added. “You also need the copy that was provided to the insurance company because it will come back into play when you submit the final documents.”
For example, if you say you have a specific control in place, and you actually don’t, Harper explained that can create a situation where “they thought they had an understanding of something, but they didn’t.”
“Be honest, transparent and accurate -- because they can deny your policy if you were inaccurate or misleading in your responses,” she said.
Mistake #2: Lax, incomplete risk assessment
It’s easier to prevent a misleading or false statement to an underwriter, when an organization has a strong assessment and inventory of the processes and tools on the system. But far too often, hospitals “don’t know everything about the control environment,” explained Harper.
“When you talk about protecting an system and preventing a cyber incident, you have to have a good understanding of the organization’s overall control environment,” Harper said. “It’s key, as the longer it takes you to identify that you’ve had an incident, it leads to more exposure and the longer it takes to recover.”
But it’s also important to remember to update this inventory or assessment when buying new tools, merging with other organizations, hiring new staff and the like, Harper explained.
“Think about all of the activities and operations that happen,” she said. “And every three years, you’re updating a cybersecurity checklist -- that may not be frequent enough.”
For example, Harper explained that an organization filling out the policy questionnaire may have all of the right elements in place. But if another tool was purchased and the controls weren’t updated or the control was removed and the underwriter was not notified, there could be a problem.
“If those controls played into how the underwriter rated you: that can be key,” said Harper. “Think about your own home: you get additional discounts when you have a burglar alarm. So if you get one, and let them know, you may get a lower rate… But if you no longer have that control, you have to tell the carrier.”
“It’s the same kind of practice that we want to get into when we get into cyber insurance for our organization,” she added.
Mistake #3: Failing to involve the right people
Many organizations understand that security needs to exist outside of the IT team. In the same vein, it’s crucial when buying a cyber insurance policy that the same mentality is applied to make sure all of your bases are covered.
“Make sure you are talking to the right individuals,” Harper said. “The appropriate key stakeholders are not only involved with the evaluation process - how many patients, how much data, etc. -- but also the responses to the questions the policy is going to ask.”
“Risk folks typically talk about it as it relates to patients,” she continued. “Those folks are key, but in addition, you need your privacy and security risk professionals, security officers, IT leader, your key business leaders/owners and those driving the data. It’s key.”
Also crucial? Making sure the facilities team is involved, as there can sometimes be a cyber incident based on a physical issue. Harper explained that “often people tend to focus on things like electronic PHI, but there’s physical PHI. If there’s a break in at a warehouse and data is stolen, OCR considers that a breach.”
Mistake #4: Failing to understand coverage
Far too often organizations make large assumptions as to just what cyber insurance will cover. Fisher explained that these leaders are often shocked to learn that they did not receive the full spectrum of coverage they wanted.
“Relying on blind faith on those terms, or what the broker or agent is telling you is a major mistake,” said Fisher. “It’s always up to up to you to go into something with eyes fully wide open to make sure you know what you’re actually buying.”
Harper took it a step further and laid to rest a common misconception when it comes to coverage: “Insurance will not cover fines and penalties associated with noncompliance. If you’re not complaint, and you didn’t do risk assessments, cyber insurance won’t protect you from that, so don’t expect it.”
Ransomware Business Impacts, Ransomware Business Cost
Projecting the overall cost of a ransomware attack can be tricky for security executives considering the many factors that can come into play when responding to and recovering from one. Information from numerous previous incidents show the costs go well beyond any demanded ransom amount and the costs associated with cleaning infected systems.
Ransomware is defined as a form of malicious software that is designed to restrict users from accessing their computers or files stored on computers till they pay a ransom to cybercriminals. Ransomware typically operates via the crypto virology mechanism, using symmetric as well as asymmetric encryption to prevent users from performing managed file transfer or accessing particular files or directories. Cybercriminals use ransomware to lock files from being used assuming that those files have extremely crucial information stored in them and the users are compelled to pay the ransom in order to regain access.
Ransomware History
It’s been said that Ransomware was introduced as an AIDS Trojan in 1989 when Harvard-educated biologist Joseph L. Popp sent 20,000 compromised diskettes named “AIDS Information – Introductory Diskettes” to attendees of the internal AIDS conference organized by the World Health Organization. The Trojan worked by encrypting the file names on the customers’ computer and hiding directories. The victims were asked to pay $189 to PC Cyborg Corp. at a mailbox in Panama.
From 2006 and on, cybercriminals have become more active and started using asymmetric RSA encryption. They launched the Archiveus Trojan that encrypted the files of the My Documents directory. Victims were promised access to the 30-digit password only if they decided to purchase from an online pharmacy.
After 2012, ransomware started spreading worldwide, infecting systems and transforming into more sophisticated forms to promote easier attack delivery as the years rolled by. In Q3, about 60,000 new ransomware was discovered, which doubled to over 200,000 in Q3 of 2012.
The first version of CryptoLocker appeared in September 2013 and the first copycat software called Locker was introduced in December of that year.
Ransomware has been creatively defined by the U.S. Department of Justice as a new model of cybercrime with a potential to cause impacts on a global scale. Stats indicate that the use of ransomware is on a steady rise and according to Veeam, businesses had to pay $11.7 on average in 2017 due to ransomware attacks. Alarmingly, the annual ransomware-induced costs, including the ransom and the damages caused by ransomware attacks, are most likely to shoot beyond $11.5 billion by 2019.
Ransomware Business Impacts Can Be Worrisome
Ransomware can cause tremendous impacts that can disrupt business operations and lead to data loss. The impacts of ransomware attacks include:
Loss or destruction of crucial information
Business downtime
Productivity loss
Business disruption in the post-attack period
Damage of hostage systems, data, and files
Loss of reputation of the victimized company
You will be surprised to know that apart from the ransom, the cost of downtime due to restricted system access can bring major consequences. As a matter of fact, losses due to downtime may cost tens of thousands of dollars daily.
As ransomware continues to become more and more widespread, companies will need to revise their annual cybersecurity goals and focus on the appropriate implementation of ransomware resilience and recovery plans and commit adequate funds for cybersecurity resources in their IT budgets.
Consider the following examples. The Erie County Medical Center (ECMC) in Buffalo, NY, last July estimated it spent $10 million responding to an attack involving a $30,000 ransom demand. About half the amount went toward IT services, software, and other recovery-related costs. The other half stemmed from staff overtime, costs related to lost revenues, and other indirect costs. ECMC officials estimated the medical center would need to spend hundreds of thousands of dollars more on upgrading technology and employee awareness training.
Public records show that the City of Atlanta spent almost $5 million just in procuring emergency IT services following a March 2018 ransomware attack that crippled essential city services for days. The costs included those associated with third-party incident response services, crisis communication, augmenting support staff and subject matter expert consulting services.
In Colorado, Gov. John Hickenlooper had to set aside $2 million from the state disaster emergency fund after ransomware infected some 2,000 Windows systems at CDOT, the state department of transportation, this February. In less than eight weeks, CDOT officials spent more than half that amount just returning systems to normal from the attack.
Not surprisingly, industry estimates relating to ransomware damages have soared recently. Cybersecurity Ventures, which pegged ransomware costs at $325 million in 2015, last year estimated damages at $5 billion in 2017 and predicted it would exceed $11.5 billion in 2019.
For security executives trying to prepare a total ransomware cost estimate, the key is not to get fixated on the ransom amount itself. Even if you end up paying it to recover your data—something that most security analysts advocate against—the actual costs of the attack in most cases will end up being greater.
Risk Facing Financial Services
Risk Facing Financial Services
Financial services institutions have changed significantly over the last decade – from utilizing technology in new ways to stay competitive and drive efficiencies, to adapting business practices in light of the global financial crisis and recent narrow interest margin markets.
As these businesses evolve, they’re faced with a new range of exposures that can result in significant and lasting commercial costs, and traditional exposures come to light in a different context. Crime has also changed for these businesses, with a growing number of attacks against financial institutions taking place online and through digital means.
To better understand this changing landscape, we’ve outlined the top risks facing financial institutions today:
Social engineering and funds transfer fraud
Some of the most frequent cyber claims made by businesses in the past year involved funds transfer fraud and some form of social engineering. Funds transfer fraud is often carried about by criminals leveraging fraudulent emails or phone calls to request the transfer of funds from a legitimate account to their own. In some cases, fraudsters will pose as a senior executive appearing to give urgent instructions to a junior employee. While financial institutions have greater control processes, including separation of responsibilities, both banks and their clients are at risk of falling victim to these types of attacks, and as long as they continue to prove successful, we expect this threat to grow in both frequency and severity. Financial institutions should consider employee training on these newer forms of fraud, including how to identify phishing emails. Banks should also be concerned about their customers’ susceptibility to social engineering fraud, and should consider education campaigns where relevant.
Adherence to post-crisis regulation
Following the mortgage crisis in 2007-2008 and the subsequent global financial crisis, the regulatory burden for banks has increased significantly. This brings additional costs when meeting these new requirements, along with higher potential penalties if an institution fails to comply. In many instances, resultant fines and penalties following regulatory failures are uninsured or uninsurable. Financial institutions should seek cover where regulatory enquiry costs and expenses are covered.
Falling prey to predatory banking
Financial institutions have found themselves in a narrow interest margin environment, which means the pressure on banks to generate revenue from non-interest earnings is intense. In some cases, the desire to drive revenue through new or existing products has led to instances of selling inappropriate products to consumers, resulting in significant consumer claims. Institutions must ensure that their products are suitable and that they meet the needs of the consumer and the consumer’s expectations. It’s also important for institutions to ensure their remuneration policies do not inadvertently encourage the miss-selling of products. The fallout from consumer protection scandals can be costly not only from a legal and regulatory standpoint, but also in terms of damage to the brand.
Reputational damage
Predatory banking is only one type of behavior that can bring reputational harm to financial institutions. Large institutions can suffer backlash for a variety of misdeeds made public, for instance the failure in anti-money laundering controls by Wells Fargo or HSBC, who were hammered in the media for their behavior. On a smaller scale, for regional and community-based institutions, the power of social media can mean that reputational damage spreads far faster than ever before.
Systemic instability
Nearly a decade later, the effects of the global financial crisis are still being felt by financial institutions around the world. Recent concerns over Deutsche Bank’s operational cut backs and stock price decline have shown there is still uncertainty around the performance of even the biggest financial organizations. Additionally, recent instability in Europe – particularly in Italy and Spain, as well as the still incomplete negotiation – could have effect elsewhere, including the US, where European headquartered institutions such as Deutsche Bank, Barclays and HSBC are systemically significant institutions.
Challenger banks and new technology
The traditional banking model is increasingly challenged by newcomers trying to use technology to replace existing processes and disrupt the status quo. In the UK and Europe, challenger banks are gaining steam and traction among younger generations and early adopters. In the US, there are few online-only challenger banks, but there is increasing competition from payment processors, online non-bank lenders and other providers who are edging their way towards areas conventionally controlled by banks. The risk for traditional institutions will not only be economic, but they will also need to provide more services to their clients to ensure they are competitive and relevant, and they may need to reassess their cyber exposure as they put more systems online.
Cybersecurity Future and Artificial Intelligence (AI)
As businesses struggle to combat increasingly sophisticated cybersecurity attacks, the severity of which is exacerbated by both the vanishing IT perimeters in today’s mobile and IoT era, coupled with an acute shortage of skilled security professionals, IT security teams need both a new approach and powerful new tools to protect data and other high-value assets. Increasingly, they are looking to artificial intelligence (AI) as a key weapon to win the battle against stealthy threats inside their IT infrastructures, according to a new global research study conducted by the Ponemon Institute on behalf of Aruba, a Hewlett Packard Enterprise company (NYSE:HPE).
The Ponemon Institute study, entitled “Closing the IT Security Gap with Automation & AI in the Era of IoT,” surveyed 4,000 security and IT professionals across the Americas, Europe and Asia to understand what makes security deficiencies so hard to fix, and what types of technologies and processes are needed to stay a step ahead of bad actors within the new threat landscape.
The research revealed that in the quest to protect data and other high-value assets, security systems incorporating machine learning and other AI-based technologies are essential for detecting and stopping attacks that target users and IoT devices. The majority of respondents agree that security products with AI functionality will help to:
Reduce false alerts (68 percent)
Increase their team’s effectiveness (63 percent)
Provide greater investigation efficiencies (60 percent)
Advance their ability to more quickly discover and respond to stealthy attacks that have evaded perimeter defense systems (56 percent)
Twenty-five percent of respondents said they currently use some form of an AI-based security solution, with another 26 percent stating they plan on deploying these types of products within the next 12 months.
Current Security Tools are not Enough
“Despite massive investments in cybersecurity programs, our research found most businesses are still unable to stop advanced, targeted attacks – with 45 percent believing they are not realizing the full value of their defense arsenal, which ranges from 10 to 75 security solutions,” said Larry Ponemon, chairman, Ponemon Institute. “The situation has become a ‘perfect storm,’ with nearly half of respondents saying it’s very difficult to protect complex and dynamically changing attack surfaces, especially given the current lack of security staff with the necessary skills and expertise to battle today’s persistent, sophisticated, highly trained, and well-financed attackers. Against this backdrop, AI-based security tools, which can automate tasks and free up IT personnel to manage other aspects of a security program, were viewed as critical for helping businesses keep up with increasing threat levels.”
IoT and Cloud Adds Significant Risk
Ponemon researchers found that the majority of IT security teams believe that a key gap in their company’s overall security strategy is their inability to identify attacks that use IoT devices as the point of entry. In fact, more than three-quarters of respondents believe their IoT devices are not secure, with 60 percent stating even simple IoT devices pose a threat. Two-thirds of respondents admitted they have little or no ability to protect their “things” from attacks. Continuous monitoring of network traffic, closed-loop detection and response systems, and detecting behavioral anomalies among peer groups of IoT devices, were cited as the most effective approaches to better protect their environments.
Even the ownership model for IoT security presents potential risk. When asked who inside their organization was responsible for IoT security, responses ranged from the CIO, CISO, CTO, and line-of-business leaders, with no majority consensus. Only 33 percent identified the CIO, with no other executive or functional group achieving response totals above 20 percent. Surprisingly, “No Function” was the third-highest answer (15 percent).
Survey results also highlighted the importance of visibility and the ability to define which resources that people and IoT devices can access, with 63 percent of respondents stating network access control is an important element of their company’s overall security strategy and critical for reducing the reach of inside exploits. Also cited as important was having detailed information about applications (71 percent), endpoints (69 percent), cloud (64 percent), and networks (63 percent), with more than half saying they currently deploy network access control solutions for enabling visibility and control across both wired and wireless networks.
Additionally, more than half of respondents said it’s hard to protect expanding and blurring IT perimeters resulting from requirements to concurrently support IoT, BYOD, mobile, and cloud initiatives (55%).
“Partnering with the Ponemon Institute helps us to improve customer experiences by better understanding security teams’ challenges, and then arming them with advanced solutions that enable quick identification and responses to an ever-changing threat landscape,” said Larry Lunetta, vice president of security solutions marketing for Aruba. “The insight gained from this study enables us to continually improve our ability to provide an enterprise wired and wireless network security framework with an integrated and more comprehensive approach for gaining back visibility and control.”
FBI: Protecting Your Networks from Ransomware
Protecting Your Networks from Ransomware
Ransomware is the fastest growing malware threat, targeting users of all types—from the home user to the corporate network. On average, more than 4,000 ransomware attacks have occurred daily since January 1, 2016. This is a 300-percent increase over the approximately 1,000 attacks per day seen in 2015. There are very effective prevention and response actions that can significantly mitigate the risk posed to your organization.
Ransomware targets home users, businesses, and government networks and can lead to temporary or permanent loss of sensitive or proprietary information, disruption to regular operations, financial losses incurred to restore systems and files, and potential harm to an organization’s reputation.
Ransomware may direct a user to click on a link to pay a ransom; however, the link may be malicious and could lead to additional malware infections. Some ransomware variants display intimidating messages, such as:
“Your computer was used to visit websites with illegal content. To unlock your computer, you must pay a $100 fine.”
“You only have 96 hours to submit the payment. If you do not send money within provided time, all your files will be permanently encrypted and no one will be able to recover them.”
What is Ransomware”
Ransomware is a form of malware that targets your critical data and systems for the purpose of extortion. Ransomware is frequently
delivered through spearphishing emails. After the user has been locked out of the data or system, the cyber actor demands a ransom payment. After receiving payment, the cyber actor will purportedly provide an avenue to the victim to regain access to the system or data. Recent iterations target enterprise end users, making awareness and training a critical preventive measure.
Protecting Your Networks
Educate Your Personnel
Attackers often enter the organization by tricking a user to disclose a password or click on a virus-laden email attachment. Remind employees to never click unsolicited links or open unsolicited attachments in emails. To improve workforce awareness, the internal security team may test the training of an organization’s workforce with simulated phishing emails. For additional information on Avoiding Social Engineering and Phishing Attacks.
Ransomware Proactive Prevention is the Best Defense
Prevention is the most effective defense against ransomware and it is critical to take precautions for protection. Infections can be devastating to an individual or organization, and recovery may be a difficult process requiring the services of a reputable data recovery specialist.
The U.S. Government (USG) recommends that users and administrators take the following preventive measures to protect their computer networks from falling victim to a ransomware infection:
Ransomware Preventive Measures
• Implement an awareness and training program. Because end users are targets, employees and individuals should be aware of the threat of ransomware and how it is delivered.
• Enable strong spam filters to prevent phishing emails from reaching the end users and authenticate inbound email using technologies like Sender Policy Framework (SPF), Domain Message Authentication Reporting and Conformance (DMARC), and DomainKeys Identified Mail (DKIM) to prevent email spoofing.
• Scan all incoming and outgoing emails to detect threats and filter executable files from reaching end users.
• Configure firewalls to block access to known malicious IP addresses.
• Patch operating systems, software, and firmware on devices. Consider using a centralized patch management system.
• Set anti-virus and anti-malware programs to conduct regular scans automatically.
• Manage the use of privileged accounts based on the principle of least privilege: no users should be assigned administrative access unless absolutely needed; and those with a need for administrator accounts should only use them when necessary.
• Configure access controls—including file, directory, and network share permissions— with least privilege in mind. If a user only needs to read specific files, the user should not have write access to those files, directories, or shares.
• Disable macro scripts from office files transmitted via email. Consider using Office Viewer software to open Microsoft Office files transmitted via email instead of full office suite applications.
• Implement Software Restriction Policies (SRP) or other controls to prevent programs from executing from common ransomware locations, such as temporary folders supporting popular Internet browsers or compression/decompression programs, including the AppData/LocalAppData folder.
• Consider disabling Remote Desktop protocol (RDP) if it is not being used.
• Use application whitelisting, which only allows systems to execute programs known and permitted by security policy.
• Execute operating system environments or specific programs in a virtualized environment.
• Categorize data based on organizational value and implement physical and logical separation of networks and data for different organizational units. Business Continuity Considerations
• Back up data regularly. Verify the integrity of those backups and test the restoration process to ensure it is working.
• Conduct an annual penetration test and vulnerability assessment.
• Secure your backups. Ensure backups are not connected permanently to the computers and networks they are backing up. Examples are securing backups in the cloud or physically storing backups offline. Some instances of ransomware have the capability to lock cloud-based backups when systems continuously back up in real time, also known as persistent synchronization. Backups are critical in ransomware recovery and response; if you are infected, a backup may be the best way to recover your critical data.
What to Do If Infected with Ransomware
Should preventive measures fail, the USG recommends that organizations consider taking the following steps upon an infection with ransomware:
• Isolate the infected computer immediately. Infected systems should be removed from the network as soon as possible to prevent ransomware from attacking network or share drives.
• Isolate or power-off affected devices that have not yet been completely corrupted. This may afford more time to clean and recover data, contain damage, and prevent worsening conditions.
• Immediately secure backup data or systems by taking them offline. Ensure backups are free of malware.
• Contact law enforcement immediately. We strongly encourage you to contact a local field office of the Federal Bureau of Investigation (FBI) or U.S. Secret Service immediately upon discovery to report a ransomware event and request assistance.
• If available, collect and secure partial portions of the ransomed data that might exist.
• If possible, change all online account passwords and network passwords after removing the system from the network. Furthermore, change all system passwords once the malware is removed from the system.
• Delete Registry values and files to stop the program from loading.
Implement your security incident response and business continuity plan. Ideally, organizations will ensure they have appropriate backups, so their response to an attack will simply be to restore the data from a known clean backup. Having a data backup can eliminate the need to pay a ransom to recover data.
There are serious risks to consider before paying the ransom. USG does not encourage paying a ransom to criminal actors. However, after systems have been compromised, whether to pay a ransom is a serious decision, requiring the evaluation of all options to protect shareholders, employees, and customers. Victims will want to evaluate the technical feasibility, timeliness, and cost of restarting systems from backup. Ransomware victims may also wish to consider the following factors:
• Paying a ransom does not guarantee an organization will regain access to their data; in fact, some individuals or organizations were never provided with decryption keys after paying a ransom.
• Some victims who paid the demand were targeted again by cyber actors.
• After paying the originally demanded ransom, some victims were asked to pay more to get the promised decryption key.
• Paying could inadvertently encourage this criminal business model.
How Law Enforcement Can Help
Any entity infected with ransomware should contact law enforcement immediately. Law enforcement may be able to use legal authorities and tools that are unavailable to most organizations. Law enforcement can enlist the assistance of international law enforcement partners to locate the stolen or encrypted data or identify the perpetrator. These tools and relationships can greatly increase the odds of successfully apprehending the criminal, thereby preventing future losses.
Federal law enforcement places a priority on conducting cyber investigations in a manner that causes minor disruption to a victim entity’s normal operations and seeks to work cooperatively and discreetly with that entity. Federal law enforcement uses investigative measures that avoid unnecessary downtime or displacement of a company’s employees. Federal law enforcement closely coordinates its activities with the affected organization to avoid unwarranted disclosure of information.
As an affected entity recovers from a cybersecurity incident, the entity should initiate measures to prevent similar incidents. Law enforcement agencies and the Department of Homeland Security’s National Cybersecurity and Communications Integration Center can assist organizations in implementing countermeasures and provide information and best practices for avoiding similar incidents in the future. Additionally, the affected organization should conduct a post-incident review of their response to the incident and assess the strengths and weaknesses of its incident response plan.
Ransomware Variants
Ransomware is a growing criminal activity involving numerous variants. Since 2012 when police locker ransomware variants first emerged, ransomware variants have become more sophisticated and destructive. Some variants encrypt not just the files on the infected device, but also the contents of shared or networked drives, externally attached storage media devices, and cloud storage services that are mapped to infected computers. These variants are considered destructive because they encrypt users’ and organizations’ files, and render those files useless until a ransom is paid.
Recent federal investigations by the FBI reveal that ransomware authors continue to improve ransomware code by using anonymizing services like “Tor ” for end-to-end communication to infected systems and Bitcoin virtual currency to collect ransom payments. Currently, the top five ransomware variants targeting U.S. companies and individuals are CryptoWall, CTBLocker, TeslaCrypt, MSIL/Samas, and Locky. New ransomware variants are continually emerging.
CryptoWall
CryptoWall and its variants have been actively used to target U.S. victims since April 2014.
CryptoWall was the first ransomware variant that only accepted ransom payments in Bitcoin.
The ransom amounts associated with CryptoWall are typically between $200 and $10,000. Following the takedown of the CryptoLocker botnet, CryptoWall has become the most successful ransomware variant with victims all over the world. Between April 2014 and June 2015, IC3 received 992 CryptoWall-related complaints, with victims reporting losses totaling over $18 million. CryptoWall is primarily spread via spam email but also infects victims through drive-by downloads and malvertising .
CTB-Locker
CTB-Locker emerged in June 2014 and is one of the first ransomware variants to use Tor for its C2 infrastructure. CTB-Locker uses Tor exclusively for its C2 servers and only connects to the C2 after encrypting victims’ files. Additionally, unlike other ransomware variants that utilize the Tor network for some communication, the Tor components are embedded in the CTBLocker malware, making it more efficient and harder to detect. CTB-Locker is spread through drive-by downloads and spam emails.
TeslaCrypt
TeslaCrypt emerged in February 2015, initially targeting the video game community by encrypting gaming files. These files were targeted in addition to the files typically targeted by ransomware (documents, images, and database files). Once the data was encrypted, TeslaCrypt attempted to delete all Shadow Volume Copies and system restore points to prevent file recovery. TeslaCrypt was distributed through the Angler, Sweet Orange, and Nuclear exploit kits.
MSIL or Samas (SAMSAM)
MSIL or Samas (SAMSAM) was used to compromise the networks of multiple U.S. victims, including 2016 attacks on healthcare facilities that were running outdated versions of the JBoss content management application. SAMSAM exploits vulnerable Java-based Web servers. SAMSAM uses open-source tools to identify and compile a list of hosts reporting to the victim’s active directory. The actors then use psexec.exe to distribute the malware to each host on the network and encrypt most of the files on the system. The actors charge varying amounts in Bitcoin to provide the decryption keys to the victim.
Locky
In early 2016, a destructive ransomware variant, Locky, was observed infecting computers belonging to businesses globally, including those in the United States, New Zealand, Australia, Germany and the United Kingdom. Locky propagates through spam emails that include malicious Microsoft Office documents or compressed attachments (e.g., .rar, .zip) that were previously associated with banking Trojans such as Dridex and Pony. The malicious attachments contain macros or JavaScript files to download the Locky files. Recently, this ransomware has also been distributed using the Nuclear Exploit Kit.
Links to Other Types of Malware
Systems infected with ransomware are also often infected with other malware. In the case of
CryptoLocker, a user typically was infected by opening a malicious attachment from an email.
This malicious attachment contained Upatre, a downloader, which infected the user with GameOver Zeus. GameOver Zeus was a variant of the Zeus Trojan used to steal banking information and other types of data. After a system became infected with GameOver Zeus, Upatre would also download CryptoLocker. Finally, CryptoLocker encrypted files on the infected system and demanded a ransom payment.
The disruption operation against the GameOver Zeus botnet also affected CryptoLocker, demonstrating the close ties between ransomware and other types of malware. In June 2014,
an international law enforcement operation successfully weakened the infrastructure of both
GameOverZeus and CryptoLocker.
Cyber security IT skills in-demand in US
There’s no doubt that demand for the technologically skilled will only increase in the upcoming years, as practically every company becomes a software-driven enterprise. A survey by the jobs site Monster found that in the US, jobs in the digital sector have multiplied at more than twice the rate of other non-digital tech sectors, and are predicted to grow by 20% in the next decade.
However, which skills will be particularly in demand? While it’s unlikely that the IT skills demanded by the jobs market today will become redundant within our lifetimes, the field is constantly evolving, and there are certainly growth areas on the horizon that IT professionals would do well to educate themselves in.
Cyber security
Cyber security is an area set to grow exponentially in importance in the upcoming years. Every time a breach is suffered by an organisation, there is a huge cost both in terms of financial loss and loss of reputation and brand value.
A recent study carried out by jobs site Indeed indicated that the US is dangerously short on cyber security skills and that the number of cyber security jobs advertised in the US is the third highest globally, meaning demand exceeded candidate interest by more than three times.
Development
Demand for skills in development is here to stay (for the time being anyway – this could change as soon as AI is more widely used to code). In 2017, the demand for software developers and engineers increased by 13% in the UK.
Devops
Another important area of growth is the trend for companies to take a devops approach to their IT departments, meaning that developers well versed in this outlook will be the most employable.
Cloud computing
It’s widely recognised that cloud computing is the future, and every IT professional should feel comfortable using these systems. Demand for cloud infrastructure specialists is increasing across the board.
Machine Learning and AI
These are two obvious areas of increasing growth. In the US, demand for AI jobs increased threefold between 2015 and 2018, even surpassing the UK in terms of demand.
HOW DOES RANSOMWARE WORK?
HOW DOES RANSOMWARE WORK?
Ransomware infections occur when a user opens a malicious email attachment, clicks on a malicious link, or visits a website infected with malicious code, known as a drive-by download.
Once a system is infected, the ransomware contacts a command and control (C2) server to generate an encryption key and begins encrypting files on the victim’s machine.
The ransomware runs quietly in the background performing in-depth searches of all disk folders, including removable drives and network shares, and encrypts as many files as it can.
Ransomware may also delete Shadow Volume Copies, destroy restore points, and overwrite free disk space to prevent victims from recovering their files and systems without paying the ransom.
If a system is powered off as files are being encrypted, some ransomware variants resume where they left off when the system or device is powered on again.
After files are encrypted, a ransom note is displayed on the screen with instructions on how and where to pay the ransom and the length of time before the hacker or software destroys the decryption key.
Some recent variants offer victims a ‘second chance’ to pay after the initial timer expires; however, the ‘second chance’ is often at least double the original ransom amount.
If the victim pays the ransom, the malware is supposed to contact the C2 server for the decryption key and begin decrypting the victim’s files; however, in many cases, the files are never decrypted.
Some ransomware files can delete themselves in order to avoid detection and analysis by security researchers or law enforcement.
CyberSecOP: Ransomware Remediation and Prevention Service
RANSOMWARE MITIGATION STRATEGIES
For many organizations, preventing ransomware entirely is nearly impossible, however, the impact of a successful infection can be greatly reduced if a robust data backup process is in place. Comprehensive data backups should be scheduled as often as possible and must be kept offline in a separate and secure location. The most effective method to prevent ransomware infections is to conduct regular training and awareness exercises with all employees to ensure users are proficient in safe Internet-browsing techniques and the ability to identify phishing emails. For specific recommendations for data protection, systems management, network management, mobile device management, and post-infection remediation.
5 steps for preventing ransomware
5 steps for preventing ransomware
Hardening Your Environment Against Ransomware
To avoid ransomware infection, follow these steps:
1. Back up your computers and servers regularly.
Regularly back up the files on both the client computers and servers. Either back up the files when the computers are offline or use a system that networked computers and servers cannot write to. If you do not have dedicated backup software, you can also copy the important files to removable media. Then eject and unplug the removable media; do not leave the removable media plugged in.
2. Lock down mapped network drives by securing them with a password and access control restrictions.
Use read-only access for files on network drives, unless it is absolutely necessary to have write access for these files. Restricting user permissions limits which files the threats can encrypt.
3. Deploy and enable the following Endpoint Protection:
Implement and managed endpoint antivirus on all endpoint to prevent ransomware, most ransomware can be detected by popular antivirus.
4. IPS/IDS
IPS blocks some threats that traditional virus definitions alone cannot stop. IPS is the best defense against drive-by downloads, which occurs when software is unintentionally downloaded from the Internet. Attackers often use exploit kits to deliver a web-based attack like CryptoLocker through a drive-by download.
See Enabling network intrusion prevention or browser intrusion prevention.
5. Download the latest patches for web application frameworks, web browsers, and web browser plug-ins.
Attacking exploit kits cannot deliver drive-by downloads unless there is an old version of a plug-in to exploit, such as Flash. Historically, attacks were delivered through phishing and web browsers. Recently, more attacks are delivered through vulnerable web applications, such as JBOSS, WordPress, and Joomla.
6. Use an email security product to handle email safely.
CryptoLocker is often spread through spam emails that contain malicious attachments. Scanning inbound emails for threats with a dedicated mail security product or service is critical to keep ransomware and other malware out of your organization. For important advice and recommendations, see:
How to remove ransomware
There is no ransomware removal tool or CryptoLocker removal tool. Instead, if your client computers do get infected with ransomware and your data is encrypted, follow these steps:
1. Do not pay the ransom.
If you pay the ransom:
· There is no guarantee that the attacker will supply a method to unlock your computer or decrypt your files.
· The attacker uses the ransom money to fund additional attacks against other users.
2. Isolate the infected computer before the ransomware can attack network drives to which it has access.
3. Update the virus definitions and scan the client computers.
New definitions are likely to detect and remediate the ransomware. Configure Endpoint Protection to automatically downloads virus definitions to the client, as long as the client is managed and connected to the Symantec Endpoint Protection Manager.
4. Restore damaged files from a known good backup.
No security Endpoint Protection cannot decrypt the files that ransom lockers have sabotaged.
Submit the malware to antivirus provider.
If you can identify the malicious email or executable, submit it to antivirus provider.
Remediate Ransomware Attack - Ransomware Survival
Made famous by the WannaCry attack that crippled the NHS in 2017, ransomware is continuing to hit businesses. According to security research firm Symantec, infections have steadily increased every year since 2013, reaching record levels in 2017.
Even over the last few months, ransomware has impacted multiple organizations, including the PGA of America, and the borough of Matanuska-Susitna in Alaska – where government workers were forced to use typewriters to carry out their daily tasks.
It is not surprising that governments are concerned about the impact of the malicious software, which locks a user’s device or data until they pay a ransom. In the UK, the National Cyber Security Centre (NCSC) has published advice on mitigating against ransomware. Meanwhile, the UK government’s behavioral change campaign for cybersecurity, Cyber Aware, promotes simple measures to stay more secure online.
RANSOMWARE REMEDIATION, RANSOMWARE PREVENTION, AND THREAT RESPONSE SERVICES
No need to configure cryptocurrency wallets or transaction with the cybercriminals. We support the transaction while charging you no commission or crypto exchange fees.
We will negotiate with the ransomware hacker to reduce ransom.
We will remove the ransomware virus or viruses
We will run the ransomware decryption tool, to ensure it doesn’t affect any other system.
But according to security researchers, there has been a decline in ransomware compared to other threats including cryptomining. Yet the malicious software remains a very real risk: attacks are becoming fewer but more targeted. “The major difference between 2017 and 2018 appears to be a trend towards more targeted ransomware,” says Matt Shabat, strategy director at Glasswall Solutions. “Instead of seeking mass infections through relatively blunt means, threat actors are using more precise infection vectors to achieve initial compromise.”
Identifying ransomware
Ransomware comes in two types. The first encrypts the files on a computer or network; the second locks a user's screen. “Some ransomware will also act like a worm – as was the case with WannaCry – and once inside a network, will spread laterally to other machines without interaction by the attacker or the infected user,” says a NCSC spokesman.
Occasionally, malware is presented as ransomware, but after the ransom is paid the files are not decrypted. This is known as ‘wiper’ malware.
The ‘ransom’ is often demanded in a cryptocurrency such as Bitcoin as a prepaid card or gift voucher. In many cases the ransom amount is modest, a tactic designed to make paying the quickest and cheapest way to resume use.
Generally, if a firm is hit by ransomware, they will have no problem realising. Infected computers will be inaccessible because key files have been encrypted, with a ransom note displayed on-screen.
Most ransomware pops up a pay page, either in a text editor or on a browser, says Paul Ducklin, senior technologist at Sophos. “But a lot of it also changes your desktop wallpaper to a graphical image of the pay page.”
And sadly, the first sign of compromise may already be too late, especially if ransomware has spread network-wide and every desktop is hijacked, says Chris Boyd, malware analyst at Malwarebytes. “Much of it comes down to basic social engineering, and fake emails aimed at HR with dubious receipt attachments harboring an infection.”
Recognizing the warning signs: Ransomware and email phishing
Email still remains the top attack vector for all malicious activity, says Adenike Cosgrove, cybersecurity strategist, EMEA, Proofpoint. She says the easiest route for cyber criminals is to exploit the vulnerability of humans “through simple yet sophisticated social engineering tactics”. She explains: “Cybercriminals have found new ways to exploit the human factor — the instincts of curiosity and trust that lead well-intentioned people to play into the hands of the attacker. This could be in the form of a disguised URL or seemingly benign attachment, but all it takes is one click and the ransomware can take hold immediately.”
The majority of ransomware is spread via massive spam campaigns involving hundreds of thousands of emails sent daily, says Dick O'Brien, threat researcher at Symantec.
Ransomware may also be spread via websites compromised to host what’s known as an exploit kit. “This is a tool that scans the visitor’s computer to see if it’s running software with known vulnerabilities,” says O’Brien. “If it finds any, it will exploit one of these vulnerabilities to download and install ransomware on the victim’s computer.”
In a small number of cases, firms may be specifically targeted by groups who attempt to break into the company’s network and infect as many computers as possible before triggering the ransomware.
How to fight off ransomware
You’ve been hit. So, what do you do?
“A lot of ransomware is poorly coded, or master keys are leaked, and it's worth checking online to see if anyone has built a decryptor tool,” says Boyd. He says his firm Malwarebytes has released standalone versions for certain versions of Petya and Chimera, “and there's many more out there”.
Whatever you do, it is agreed that paying the ransom is a big mistake. Indeed, the National Crime Agency encourages industry and the public not to pay the ransom.
“We strongly advise not to pay the ransom, as it simply encourages the scammers to continue with their profitable business model,” agrees Boyd.
Jake Moore, cybersecurity specialist at ESET says he always advises against paying. “But I have seen CEOs with their heads in their hands asking me, ‘what else can we do?’ when they realise their resilience measures have also been attacked.”
Yet there is no guarantee that you will ever receive the data back and if you do, it might be damaged. “Funding cyber criminals also funds larger cyber-attacks, so it must be reiterated that paying won't always get make the issue go away,” says Moore.
Avoiding future attacks requires preparation such as incident response plans and educating employees.
organizations aren't training employees in security basics. “Perhaps they're not sending out emails warning about common scams, or maybe they aren't bothering with security tools known to prevent exploits and ransomware.”
Employees should be trained on how to spot attacks. This helps to avoid becoming a victim, and also means staff can raise the alarm straight away, says David Moore, managing director, CyberSecOp Security. “Employees can become your strongest line of defense. Attackers will hit as many people in an organization as possible, and one click is all it takes. So, having a workforce of people ready to sound the alarm will help prevent that one click.”
It’s important to look for less obvious attacks. “Looking out for the less obvious attacks is highly advisable. If any hint of files being corrupted or encrypted is immediately addressed at the source, it will help to reduce the extent of an attack.”
It might seem obvious, but backup is integral. Even without other measures, firms would still be able to bring their files back with ease if they had a sensible backup process in place.
Prevent DDoS attacks across your enterprise
DDoS (Distributed Denial of Service) attacks feature amongst the most dreaded kinds of cyber attacks, for any enterprise today. This is especially because, as the name itself suggests, there it causes a total denial of service; it exhausts all resources of an enterprise network, application or service and consequently it becomes impossible to gain access to the network, application or the service.
In general, a DDoS attack is launched simultaneously from multiple hosts and it would suffice to host the resources, the network and the internet services of enterprises of any size. Many prominent organizations today encounter DDoS attacks on a daily basis. Today DDoS attacks are becoming more frequent and they are increasing in size, at the same time becoming more sophisticated. In this context, it becomes really important that enterprises look for DDoS attack prevention services, in fact the best DDoS attack prevention services, so as to ensure maximum protection for their network and data.
The different kinds of DDoS attacks
Though there are different kinds of DDoS attacks, broadly speaking there are three categories into which all the different kinds of DDoS attacks would fit.
The first category is the volumetric attacks, which include those attacks that aim at overwhelming network infrastructure with bandwidth-consuming traffic or by deploying resource-sapping requests. The next category, the TCP state-exhaustion attacks, refer to the attacks that help hackers abuse the stateful nature of the TCP protocol to exhaust resources in servers, load balancers and firewalls. The third category of DDoS attacks, the application layer attacks, are basically the ones targeting any one aspect of an application or service at Layer 7.
Of the above-mentioned three categories, volumetric attacks are the most common ones; at the same time there are DDoS attacks that combine all these three vectors and such attacks are becoming commonplace today.
DDoS attacks getting sophisticated, complex and easy-to-use
Cybercriminals today are getting cleverer and smarter. They tend to package complex, sophisticated DDoS attack tools into easy-to-use downloadable programs, thereby making it easy even for non-techies to carry out DDoS attacks against organizations.
What are the main drivers behind DDoS attacks? Well, there could be many, ranging from ideology or politics to vandalism and extortion. DDoS is increasingly becoming a weapon of choice for hacktivists as well as terrorists who seek to disrupt operations or resort to extortion. Gamers too use DDoS as a means to gain competitive advantage and win online games.
There are clever cybercriminals who use DDoS as part of their diversionary tactics, intending to distract organizations during APT campaigns that are planned and executed in order to steal data.
How to prevent DDoS attacks
The first thing that needs to be done, to prevent DDoS attacks from happening, is to secure internet-facing devices and services. This helps reduce the number of devices that can be recruited by hackers to participate in DDoS attacks.
Since cybercriminals abuse protocols like NTP, DNS, SSDP, Chargen, SNMP and DVMRP to generate DDoS traffic, it’s advisable that services that use any of these ought to be carefully configured and run on hardened, dedicated servers.
Do repeated tests for security issues and vulnerabilities. One good example is doing penetration tests for detecting web application vulnerabilities.
Ensure that your enterprise implements anti-spoofing filters as covered in IETF Best Common Practices documents BCP 38 and BCP 84. This is because hackers who plan DDoS attacks would generate traffic with spoofed source IP addresses.
Though there are no fool-proof techniques that can prevent DDoS attacks completely, you can ensure maximum protection by ensuring proper configuration of all machines and services. This would ensure that attackers don’t harness publicly available services to carry out DDoS attacks.
It’s to be remembered that it’s difficult to predict or avoid DDoS attacks and also that even an attacker with limited resources can bring down networks or websites. Hence, for any organization, it becomes important that the focus is always on maximum level protection for enterprise networks, devices, websites etc.
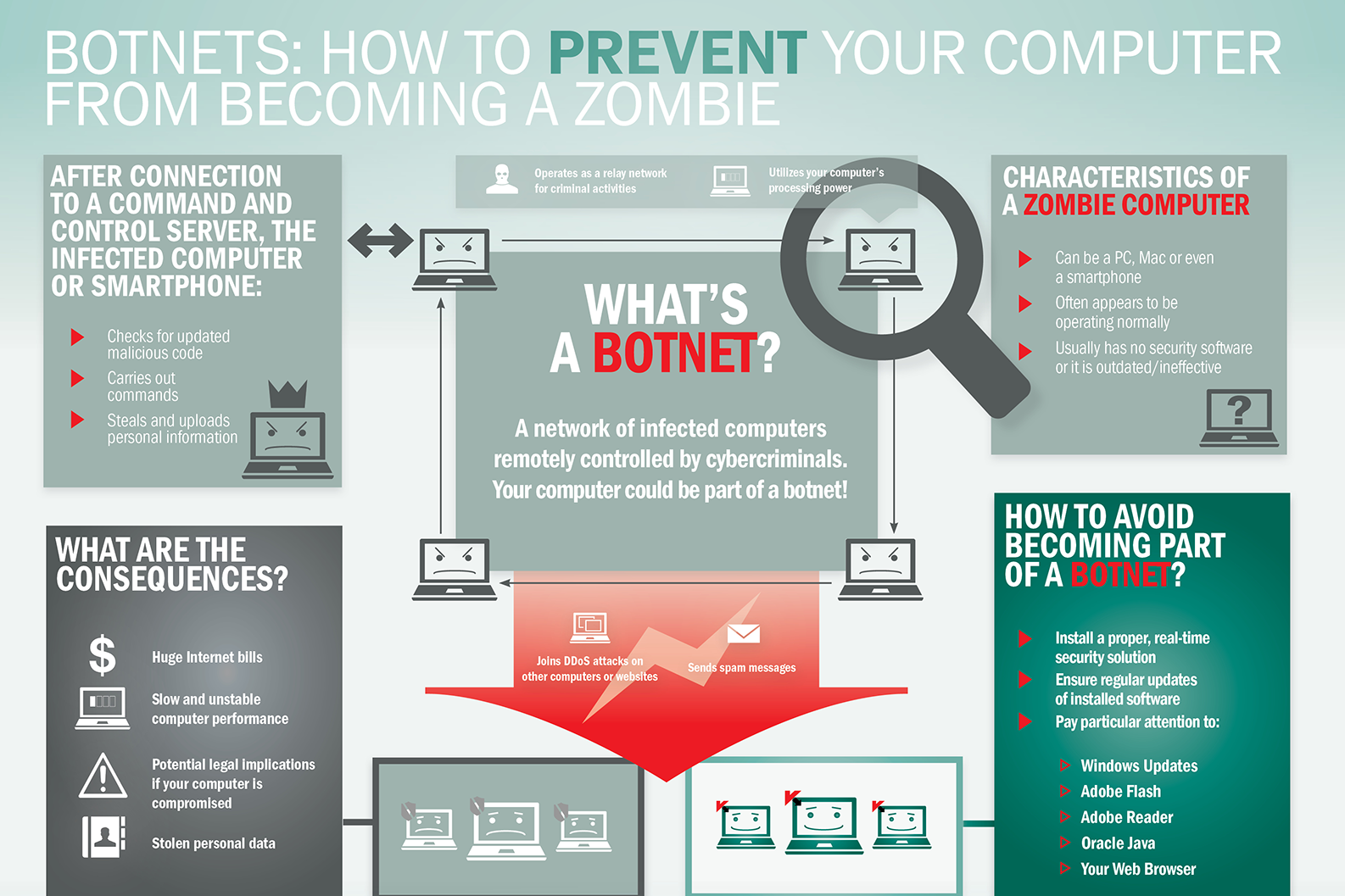
What is Botnet - Cybercriminals #1 Weapon
The word Botnet is formed from the words ‘robot’ and ‘network’. Cybercriminals use special Trojan viruses to breach the security of several users’ computers, take control of each computer and organise all of the infected machines into a network of ‘bots’ that the criminal can remotely manage.
Botnet Prevention- What is Botnet
How Botnets can impact you
Often, the cybercriminal will seek to infect and control thousands, tens of thousands or even millions of computers – so that the cybercriminal can act as the master of a large ‘zombie network’ – or ‘bot-network’ – that is capable of delivering a Distributed Denial of Service (DDoS) attack, a large-scale spam campaign or other types of cyberattack.
In some cases, cybercriminals will establish a large network of zombie machines and then sell access to the zombie network to other criminals – either on a rental basis or as an outright sale. Spammers may rent or buy a network in order to operate a large-scale spam campaign.
How to prevent your computer becoming part of a Botnet
Installing effective anti-malware software will help to protect your computer against Trojans and other threats.
What advice does the world's first CISO have
What advice does the world's first CISO have for the current generation of CISOs? Stephen Katz emphasizes, first and foremost, that cybersecurity must be treated as a business risk management issue rather than a technology issue.
"Security has to evolve and grow at the same pace as the business," he stresses in an interview with Information Security Media Group.
The role of the CISO has to be recognized as a core business function, he adds. "Security has to be an enabler of the business; security has to earn a seat at the executive table. Too often, we give people the title of chief information security officer; they don't believe they're an executive, and executives don't believe they are an executive."
In this interview (see audio link below photo), Katz also discusses:
Changes in the threat landscape since becoming the world's first CISO;
Top priorities for CISOs in the coming year;
Why getting back to the basics of security remains so important;
The ongoing growth of machine learning models in all aspects of cybersecurity.
Katz is the founder and president of Security Risk Solutions LLC, an information security company providing consulting, mentoring, coaching and advisory services. He was formerly CISO at JPMorgan Chase, Citigroup and Merrill Lynch.
Secure Google Chrome from Hacking Attacks
Google Chrome is definitely one of the most popular web browsers being used today. Hackers, as we know, are perpetually after whatever gets popular in the world of the internet. This because whatever is popular would help them target more people and steal more data. Thus, Google Chrome too happens to be among the most favorite for cyber criminals across the world. Hence, securing Google Chrome against hacking attacks is really important.
So, how do we secure Google Chrome from cyber attacks? Well, it’s a multi-step process. Lots of things have to be done. Securing your browser is important as it helps secure your device, your internet connection and more importantly, your personal and business data.
Let’s discuss, in detail, what all needs to be done to secure Google Chrome from hacking attacks. Here we go:
Begin by ensuring that your Google account is properly secured!
This is something basic, your Google account needs to be properly secured. Chrome lets you sign in from any device, anytime. Hence, it’s important to ensure the security of your Google account. You need to make sure you are logged out of your account every time you sign in, on any device. You also need to ensure that your password is secure. If you aren’t signed out or if someone knows/cracks your password, it would be easy to manipulate things and cause you harm. Your data could be stolen.
Keeping the browser secured is equally important…
Keeping the browser secured is as important as securing your Google account. You could use a password to protect your browser, and thus, in your absence, no one would be able to take control of your browser and do mischiefs. Similarly, every time you leave your terminal, it’s good to go out of the browser as well.
Keep your browser ‘clean’!
You should make it a habit to keep your browser ‘clean’, by wiping out most of the information from it. In fact, there should be some plan/schedule as regards cleaning the browser. Clear the history periodically, either everytime you log out or at least once every week if not once a day.
Never save passwords on the browser
The browser might offer to ‘remember’ your passwords for you so that you could sign in easily the next time you’re using some service. But it’s always good not to save passwords on the browser. If you save your passwords, it would be possible for someone else to get into your account and misuse it or steal information.
Having a master password helps
Having a master password, which would help you get to your other saved passwords in Chrome, is a good thing to do. Thus you need not worry about remembering all of your passwords and you don’t have to be afraid of your passwords getting stolen or misused either.
Keep your device protected
The device that you use to browse needs to be protected from malware and hacking. For this, you must use whatever security tools you need and also have alerts that tell you if at all your device is compromised. Remember a compromised device means an unsecured browser!
Keep the device locked whenever you’re not using it
Always keep your device locked when you are not using it, be it a computer or any other mobile device. That prevents people from getting on to your device and hijacking your browser and your data as well. Locking your device also gets it off the WiFi network that you are using.
Secure your network, never use unsafe WiFi networks
Securing your network is important; it helps a lot in securing Google Chrome from hacking attacks. Hence you need to do all that is needed to secure your network. Similarly, it’s always advisable never to use unsafe WiFi networks. Whenever you’re using a WiFi network, ensure it’s properly encrypted and if possible use an app or program that would prevent hacking. In fact, using a secure network secures not just your browser, but everything on your device/system.
Trust Chrome for phishing detection
Google Chrome does its own phishing detection and protects you from many phishing websites. So, when your browser tells you that a website is not safe, it’s always advisable to trust it and avoid such sites.
Avoid phishing websites and attachments yourself
In addition to Google Chrome detecting phishing websites for you, it’s always good that you yourself stay away from websites/attachments that could be used for phishing scams. Staying away from such suspicious websites secures your browser, your system/network and your data.
Useful tips for implementing the cloud
Useful tips for implementing the cloud
“One very important thing is to not implement solutions on the cloud with a traditional mindset. Many clients are surprised when they see their first bill because they ‘lift and shift’ the infrastructure,”
“Remember, the cloud is highly elastic in nature and you can scale up and when you require. So, implement the minimum infrastructure needed and scale it based on load. That’s the secret to success in the cloud!”
Focus on entry and exit points in terms of network connectivity. Wherever possible, use private connections such as Microsoft express route, AWS direct connect.
In terms of cloud application connectivity, always encrypt the data in transit using SSL.
Ensure you implement least privileged and conditional based access to cloud administrative portals such as the Azure portal and AWS management console.
Implement RBAC access in providing access to cloud resources. Segregation and isolation of the resources using resource groups, virtual networks is key!
Utilise the security monitoring tools provided by cloud services provider to monitor the solution. Most of the basic functionality is free, such as Azure’s security centre.
In general, always divide the security focus areas into a matrix where rows are networks, compute, storage, applications, databases, and columns are data encryption at rest, encryption at transit, authentication and authorization etc; this will allow focussing on each security cell.
Carry out security risk assessment during the design phase to ensure the design has the appropriate security controls in place to mitigate possible risks.
Nevertheless, problems can arise when storing data in the cloud. “Services & data in the cloud is accessible from the internet. Unless proper controls in place, your users can access and download the data from anywhere in the world,” warns Varma.
Cloud storage security
“The majority of clients require their data to be encrypted in the cloud. Although cloud supports ‘bring your own key’ options, these encryption keys are stored in cloud providers key vaults. So, there is a very narrow chance that cloud providers can access those keys and decrypt the data. It’s also vital to note that cloud providers have very strict governance and accreditations in place to mitigate the same.”
Cloud providers generally keep their cloud services up-to-date with advancements in technology, according to Varma. “On the other end, many of the clients’ data centers he has worked within the past have out-of-date IT infrastructure systems & applications which takes a lot of time and money to replace and are prone to attacks”, he adds.
Varma also advises that you must ask your service provider the following questions about cloud storage security:
What is the authentication and authorization approach to cloud services?
How do you implement access controls for cloud services?
What’s the approach to secure transit and rest data?
What is preventive security monitoring are in place against risks and threats?
Are their solution adheres to such as cyber essentials, cloud security principles, ISO 27002?
Businesses Expansion of Attack Surfaces
One of the main reasons cyber risk increases exponentially is the rapid expansion of attack surfaces. In these places, software programs are vulnerable to attack or probe by an adversary. According to the SANS Institute, attack surfaces can include any part of a company’s infrastructure that exposes its networks and systems to the outside, from servers and open ports to SQLs, email authentication, and even employees with “access to sensitive information.” It can also include user input via keyboard or mouse, network traffic, and external hardware that is not protected by cyber hardening technology.
It would be easy to blame the Internet of Things (IoT) for expanding attacks, as Intel projects two billion smart devices worldwide by 2020. But in reality, the IoT is only part of the attack surface epidemic.
According to Cybersecurity Ventures, there are now 111 billion new lines of code written each year, introducing vulnerabilities both known and unknown. Not to be overlooked as a flourishing attack vector are humans, which some argue are both the most important and the weakest link in the cyberattack kill chain. In fact, in many cybersecurity circles, there is a passionate and ongoing debate regarding just how much burden businesses should put on employees to prevent and detect cyber threats. However, what is not up for debate open is just how vulnerable humans are to intentionally or unintentionally open the digital door for threat actors to walk in. This is most evident because 9 out of 10 cyberattacks begin with some form of email phishing targeting workers with mixed levels of cybersecurity training and awareness.
Critical Infrastructure Protection Remains a Challenge
Critical infrastructure, often powered by SCADA systems and equipment now identified as part of the Industrial Internet of Things (IIoT), is a significant contributor to attack surface expansion. Major attacks targeting these organizations occur more from memory corruption errors and buffer overflows exploits than from spear-phishing or email spoofing and tends to be the motive of nation-states and cyber terrorists more so than generic hackers.
“Industrial devices are designed to have a long life span, but most legacy equipment still in use was not originally built to achieve automation and connectivity.” The IIoT does provide many efficiencies and cost-savings benefits to companies in which operational integrity, confidentiality, and availability are of the utmost importance. Still, introducing technology into heavy machinery and equipment that wasn’t built to communicate outside of a facility has proven challenging. The concept of IT/OT integration, which is meant to merge the physical and digital security of corporations and facilities, has failed to reduce vulnerabilities in a way that significantly reduces risk. As a result, attacks seeking to exploit critical infrastructure vulnerabilities, such as WannaCry, have become the rule and not the exception.
To date, ARE CYBERCRIMINALS winning?
Critical infrastructure cybersecurity has relied too much upon network monitoring and anomaly detection to detect suspicious traffic before it turns problematic. The challenge with this approach is that it is reactionary and only effective after an adversary has breached some level of defense.
We take an entirely different approach, focusing on prevention by denying malware the uniformity it needs to propagate. We use a binary randomization technique that shuffles the basic constructs of a program, known as basic blocks, to produce functionally identical code but legally unique. When an attacker develops an exploit for a known vulnerability in a program, it is helpful to know where all the code is located so that they can repurpose it to do their bidding. Binary randomization renders that prior knowledge useless, as each instance of a program has code in different locations.
One way to visualize the concept of binary randomization is to picture the Star Wars universe at the time when Luke Skywalker and the Rebel Alliance set off to destroy the Death Star. The Rebel Alliance had the blueprints to the Death Star and used those blueprints to find its only weakness. Luke set off in his X-Wing and delivered a proton torpedo directly to the weak spot in the Death Star, destroying it. In this scenario, the Death Star is a vulnerable computer program, and Luke is an adversary trying to exploit said computer program.
Now imagine that the Galactic Empire built 100 Death Stars, protected by RunSafe’s new Death Star Weakness Randomization. This protection moves the weakness to a different place on each Death Star. Now imagine you are Luke, flying full speed toward the flaw in the Death Star, chased by TIE fighters, only to find that the weakfaultnot where the blueprint showed. The Rebel attack fails, and the Galactic Empire celebrates by destroying another planet. Like the Death Star scenario above, code protected with binary randomization will still contain vulnerabilities. Still, an attacker’s ability to successfully exploit that vulnerability on multiple targets becomes much more difficult.