CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
What is Botnet - Cybercriminals #1 Weapon
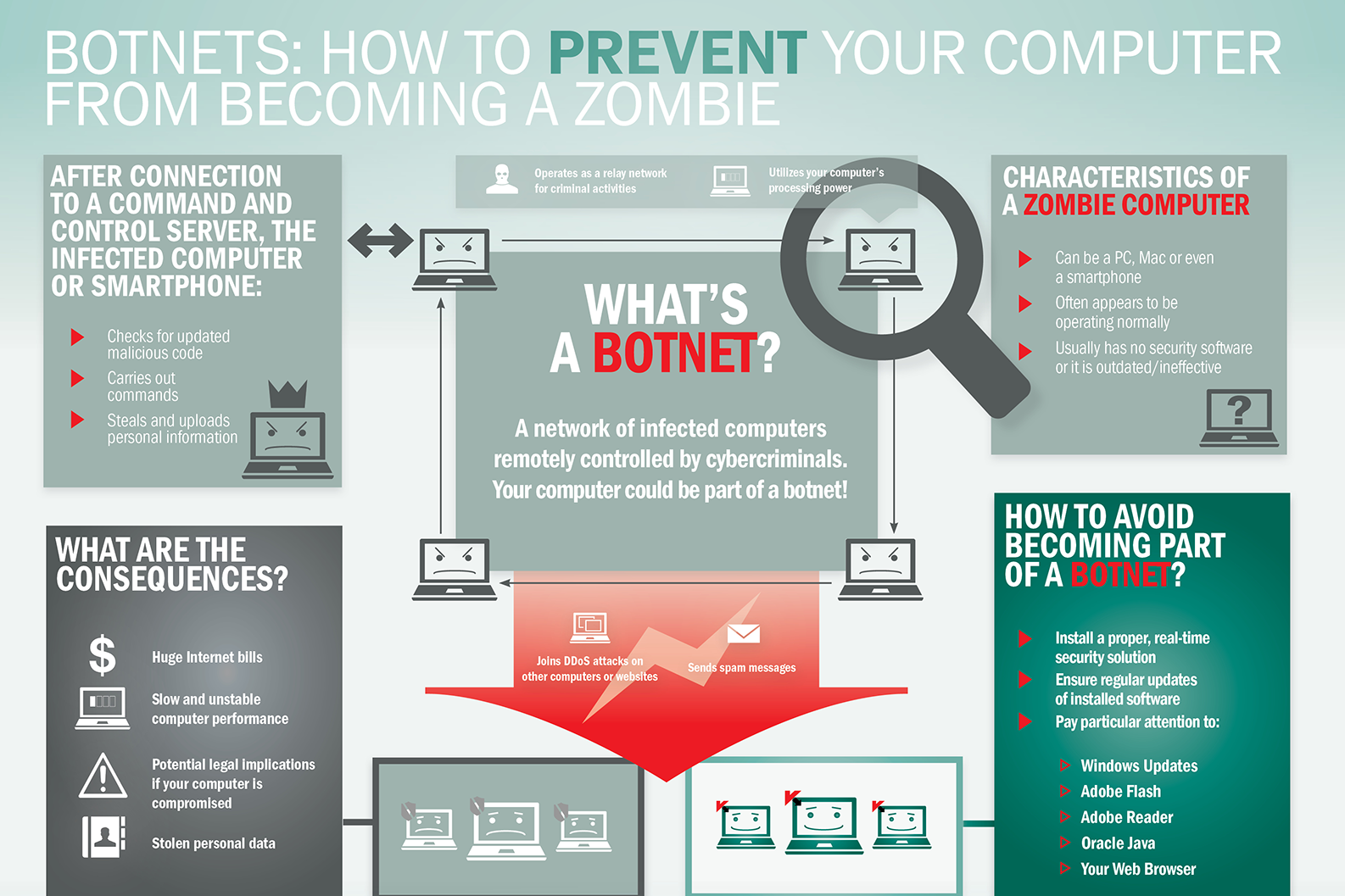
The word Botnet is formed from the words ‘robot’ and ‘network’. Cybercriminals use special Trojan viruses to breach the security of several users’ computers, take control of each computer and organise all of the infected machines into a network of ‘bots’ that the criminal can remotely manage.
Botnet Prevention- What is Botnet
How Botnets can impact you
Often, the cybercriminal will seek to infect and control thousands, tens of thousands or even millions of computers – so that the cybercriminal can act as the master of a large ‘zombie network’ – or ‘bot-network’ – that is capable of delivering a Distributed Denial of Service (DDoS) attack, a large-scale spam campaign or other types of cyberattack.
In some cases, cybercriminals will establish a large network of zombie machines and then sell access to the zombie network to other criminals – either on a rental basis or as an outright sale. Spammers may rent or buy a network in order to operate a large-scale spam campaign.
How to prevent your computer becoming part of a Botnet
Installing effective anti-malware software will help to protect your computer against Trojans and other threats.
What advice does the world's first CISO have
What advice does the world's first CISO have for the current generation of CISOs? Stephen Katz emphasizes, first and foremost, that cybersecurity must be treated as a business risk management issue rather than a technology issue.
"Security has to evolve and grow at the same pace as the business," he stresses in an interview with Information Security Media Group.
The role of the CISO has to be recognized as a core business function, he adds. "Security has to be an enabler of the business; security has to earn a seat at the executive table. Too often, we give people the title of chief information security officer; they don't believe they're an executive, and executives don't believe they are an executive."
In this interview (see audio link below photo), Katz also discusses:
Changes in the threat landscape since becoming the world's first CISO;
Top priorities for CISOs in the coming year;
Why getting back to the basics of security remains so important;
The ongoing growth of machine learning models in all aspects of cybersecurity.
Katz is the founder and president of Security Risk Solutions LLC, an information security company providing consulting, mentoring, coaching and advisory services. He was formerly CISO at JPMorgan Chase, Citigroup and Merrill Lynch.
Secure Google Chrome from Hacking Attacks
Google Chrome is definitely one of the most popular web browsers being used today. Hackers, as we know, are perpetually after whatever gets popular in the world of the internet. This because whatever is popular would help them target more people and steal more data. Thus, Google Chrome too happens to be among the most favorite for cyber criminals across the world. Hence, securing Google Chrome against hacking attacks is really important.
So, how do we secure Google Chrome from cyber attacks? Well, it’s a multi-step process. Lots of things have to be done. Securing your browser is important as it helps secure your device, your internet connection and more importantly, your personal and business data.
Let’s discuss, in detail, what all needs to be done to secure Google Chrome from hacking attacks. Here we go:
Begin by ensuring that your Google account is properly secured!
This is something basic, your Google account needs to be properly secured. Chrome lets you sign in from any device, anytime. Hence, it’s important to ensure the security of your Google account. You need to make sure you are logged out of your account every time you sign in, on any device. You also need to ensure that your password is secure. If you aren’t signed out or if someone knows/cracks your password, it would be easy to manipulate things and cause you harm. Your data could be stolen.
Keeping the browser secured is equally important…
Keeping the browser secured is as important as securing your Google account. You could use a password to protect your browser, and thus, in your absence, no one would be able to take control of your browser and do mischiefs. Similarly, every time you leave your terminal, it’s good to go out of the browser as well.
Keep your browser ‘clean’!
You should make it a habit to keep your browser ‘clean’, by wiping out most of the information from it. In fact, there should be some plan/schedule as regards cleaning the browser. Clear the history periodically, either everytime you log out or at least once every week if not once a day.
Never save passwords on the browser
The browser might offer to ‘remember’ your passwords for you so that you could sign in easily the next time you’re using some service. But it’s always good not to save passwords on the browser. If you save your passwords, it would be possible for someone else to get into your account and misuse it or steal information.
Having a master password helps
Having a master password, which would help you get to your other saved passwords in Chrome, is a good thing to do. Thus you need not worry about remembering all of your passwords and you don’t have to be afraid of your passwords getting stolen or misused either.
Keep your device protected
The device that you use to browse needs to be protected from malware and hacking. For this, you must use whatever security tools you need and also have alerts that tell you if at all your device is compromised. Remember a compromised device means an unsecured browser!
Keep the device locked whenever you’re not using it
Always keep your device locked when you are not using it, be it a computer or any other mobile device. That prevents people from getting on to your device and hijacking your browser and your data as well. Locking your device also gets it off the WiFi network that you are using.
Secure your network, never use unsafe WiFi networks
Securing your network is important; it helps a lot in securing Google Chrome from hacking attacks. Hence you need to do all that is needed to secure your network. Similarly, it’s always advisable never to use unsafe WiFi networks. Whenever you’re using a WiFi network, ensure it’s properly encrypted and if possible use an app or program that would prevent hacking. In fact, using a secure network secures not just your browser, but everything on your device/system.
Trust Chrome for phishing detection
Google Chrome does its own phishing detection and protects you from many phishing websites. So, when your browser tells you that a website is not safe, it’s always advisable to trust it and avoid such sites.
Avoid phishing websites and attachments yourself
In addition to Google Chrome detecting phishing websites for you, it’s always good that you yourself stay away from websites/attachments that could be used for phishing scams. Staying away from such suspicious websites secures your browser, your system/network and your data.
Useful tips for implementing the cloud
Useful tips for implementing the cloud
“One very important thing is to not implement solutions on the cloud with a traditional mindset. Many clients are surprised when they see their first bill because they ‘lift and shift’ the infrastructure,”
“Remember, the cloud is highly elastic in nature and you can scale up and when you require. So, implement the minimum infrastructure needed and scale it based on load. That’s the secret to success in the cloud!”
Focus on entry and exit points in terms of network connectivity. Wherever possible, use private connections such as Microsoft express route, AWS direct connect.
In terms of cloud application connectivity, always encrypt the data in transit using SSL.
Ensure you implement least privileged and conditional based access to cloud administrative portals such as the Azure portal and AWS management console.
Implement RBAC access in providing access to cloud resources. Segregation and isolation of the resources using resource groups, virtual networks is key!
Utilise the security monitoring tools provided by cloud services provider to monitor the solution. Most of the basic functionality is free, such as Azure’s security centre.
In general, always divide the security focus areas into a matrix where rows are networks, compute, storage, applications, databases, and columns are data encryption at rest, encryption at transit, authentication and authorization etc; this will allow focussing on each security cell.
Carry out security risk assessment during the design phase to ensure the design has the appropriate security controls in place to mitigate possible risks.
Nevertheless, problems can arise when storing data in the cloud. “Services & data in the cloud is accessible from the internet. Unless proper controls in place, your users can access and download the data from anywhere in the world,” warns Varma.
Cloud storage security
“The majority of clients require their data to be encrypted in the cloud. Although cloud supports ‘bring your own key’ options, these encryption keys are stored in cloud providers key vaults. So, there is a very narrow chance that cloud providers can access those keys and decrypt the data. It’s also vital to note that cloud providers have very strict governance and accreditations in place to mitigate the same.”
Cloud providers generally keep their cloud services up-to-date with advancements in technology, according to Varma. “On the other end, many of the clients’ data centers he has worked within the past have out-of-date IT infrastructure systems & applications which takes a lot of time and money to replace and are prone to attacks”, he adds.
Varma also advises that you must ask your service provider the following questions about cloud storage security:
What is the authentication and authorization approach to cloud services?
How do you implement access controls for cloud services?
What’s the approach to secure transit and rest data?
What is preventive security monitoring are in place against risks and threats?
Are their solution adheres to such as cyber essentials, cloud security principles, ISO 27002?
Businesses Expansion of Attack Surfaces
One of the main reasons cyber risk increases exponentially is the rapid expansion of attack surfaces. In these places, software programs are vulnerable to attack or probe by an adversary. According to the SANS Institute, attack surfaces can include any part of a company’s infrastructure that exposes its networks and systems to the outside, from servers and open ports to SQLs, email authentication, and even employees with “access to sensitive information.” It can also include user input via keyboard or mouse, network traffic, and external hardware that is not protected by cyber hardening technology.
It would be easy to blame the Internet of Things (IoT) for expanding attacks, as Intel projects two billion smart devices worldwide by 2020. But in reality, the IoT is only part of the attack surface epidemic.
According to Cybersecurity Ventures, there are now 111 billion new lines of code written each year, introducing vulnerabilities both known and unknown. Not to be overlooked as a flourishing attack vector are humans, which some argue are both the most important and the weakest link in the cyberattack kill chain. In fact, in many cybersecurity circles, there is a passionate and ongoing debate regarding just how much burden businesses should put on employees to prevent and detect cyber threats. However, what is not up for debate open is just how vulnerable humans are to intentionally or unintentionally open the digital door for threat actors to walk in. This is most evident because 9 out of 10 cyberattacks begin with some form of email phishing targeting workers with mixed levels of cybersecurity training and awareness.
Critical Infrastructure Protection Remains a Challenge
Critical infrastructure, often powered by SCADA systems and equipment now identified as part of the Industrial Internet of Things (IIoT), is a significant contributor to attack surface expansion. Major attacks targeting these organizations occur more from memory corruption errors and buffer overflows exploits than from spear-phishing or email spoofing and tends to be the motive of nation-states and cyber terrorists more so than generic hackers.
“Industrial devices are designed to have a long life span, but most legacy equipment still in use was not originally built to achieve automation and connectivity.” The IIoT does provide many efficiencies and cost-savings benefits to companies in which operational integrity, confidentiality, and availability are of the utmost importance. Still, introducing technology into heavy machinery and equipment that wasn’t built to communicate outside of a facility has proven challenging. The concept of IT/OT integration, which is meant to merge the physical and digital security of corporations and facilities, has failed to reduce vulnerabilities in a way that significantly reduces risk. As a result, attacks seeking to exploit critical infrastructure vulnerabilities, such as WannaCry, have become the rule and not the exception.
To date, ARE CYBERCRIMINALS winning?
Critical infrastructure cybersecurity has relied too much upon network monitoring and anomaly detection to detect suspicious traffic before it turns problematic. The challenge with this approach is that it is reactionary and only effective after an adversary has breached some level of defense.
We take an entirely different approach, focusing on prevention by denying malware the uniformity it needs to propagate. We use a binary randomization technique that shuffles the basic constructs of a program, known as basic blocks, to produce functionally identical code but legally unique. When an attacker develops an exploit for a known vulnerability in a program, it is helpful to know where all the code is located so that they can repurpose it to do their bidding. Binary randomization renders that prior knowledge useless, as each instance of a program has code in different locations.
One way to visualize the concept of binary randomization is to picture the Star Wars universe at the time when Luke Skywalker and the Rebel Alliance set off to destroy the Death Star. The Rebel Alliance had the blueprints to the Death Star and used those blueprints to find its only weakness. Luke set off in his X-Wing and delivered a proton torpedo directly to the weak spot in the Death Star, destroying it. In this scenario, the Death Star is a vulnerable computer program, and Luke is an adversary trying to exploit said computer program.
Now imagine that the Galactic Empire built 100 Death Stars, protected by RunSafe’s new Death Star Weakness Randomization. This protection moves the weakness to a different place on each Death Star. Now imagine you are Luke, flying full speed toward the flaw in the Death Star, chased by TIE fighters, only to find that the weakfaultnot where the blueprint showed. The Rebel attack fails, and the Galactic Empire celebrates by destroying another planet. Like the Death Star scenario above, code protected with binary randomization will still contain vulnerabilities. Still, an attacker’s ability to successfully exploit that vulnerability on multiple targets becomes much more difficult.
Cyber Criminals Loves the Cloud (Hackers Cloud Life)
Are hackers smarter and more creative than cyber guardians? This is becoming the eternal question of the digital age. While we would like to think the protection of customer passwords and personal credentials is the job of IT experts, reports of recent data breaches now suggest we are losing the battle against online criminals. The situation at hand can be likened to a carjacker who enters a parking lot and simply strolls to the stall where all the keys are kept. The parking guard is mysteriously missing, and the keys are ripe for the taking, even to the big, expensive vehicles. This is essentially the situation hackers are now enjoying on the Cloud—a relatively unguarded and highly accessible environment.
Organizational growth and development have led to increased use of the Cloud, which has exacerbated the problem of compromised user data. Companies have essentially transferred VPN and cloud access credentials to available cloud storage. Hackers are sending bots to scour GitHub, the source code administration framework, searching for advanced access keys to Amazon Web Services and other cloud frameworks. In 2015, one indiscreet developer woke to discover his stolen keys were being utilized to run 140 AWS servers mining bitcoin. Indeed, even U.S. Intelligence facts, including security keys to access “distributed intelligence systems,” were also left exposed to the public suggest Bay Area security firm, UpGuard.
Further, even if credentials aren’t left in a discoverable location, hackers can break into a network and find unprotected or unencrypted keys lying around to gain access. In spite of the dangers, developers are still consistently putting away the digital assets and resources and even client data in the source code, setup documents, and different random, unencrypted areas. Not like run of the mill user who can remember their passwords or store them with a protected secret word, engineers and IT professionals regularly need to keep security credentials where automated programs can find them. What’s more, the sensitive information of ordinary clients is also being inadvertently left unattended on some organization networks, where hackers don’t have to work very hard for access.
SECURING THE CLOUD
Cloud managers are struggling to stop the leak of critical data. Sophisticated new cybersecurity tools designed to safely store these important credentials in a legitimate, automated way are looking to revamp accessibility by scanning uploaded files to the cloud storage to ensure passwords and keys aren’t exposed. According to industry experts, this effort is doing much to turn the tide of cybercrime.
Cloud managers are also trying to close the entryway leading to the exposure of more basic data. Refined new cybersecurity tools want to safely store these sorts of credentials in a genuine way that grants access to automated procedures but not hackers.
Armon Dadgar, founder and co-CTO of San Francisco-based software company HashiCorp explains, “Everyone knew this was a bad thing to do. It wasn’t like anyone had an illusion that keeping these credentials in plain text was smart or sane, but no one had a better answer.”
Amazon launched AWS Secrets Manager last month, its own credential management tool. This was followed by Microsoft’s Azure Key Vault which securely stores, monitors, and controls access to this kind of data. But even as these tools become available, companies with avid developers, all of whom have a wide array of remote tools using credentials, are being continually challenged by security issues. Christoffer Fjellström, a developer at Swedish security firm Detectify says, “The main problem is that companies really don’t have policies for it or they don’t follow up and make sure those policies are followed.”
Recent hacks have made it clear that few organizations can hope to keep their networks entirely free from intrusion. Dadgar goes on to explain, “Many companies paid less attention to the security of data within their firewalls. In that world, things like secret management were just less important. Does it matter that you have my database credential if you’re not on my network?”
Other new tools help detect if secure data is being sent and stored where it doesn’t belong. UpGuard, known for its frequent role in detecting leaks tied to data stored on insecure cloud machines, has released BreachSight which scours the internet for its clients’ exposed code, credentials, personally identifiable information, and other sensitive data.
“You might have this world-class team, but the project manager has an online Kanban board sitting out in the open that he’s using for notes, and it’s full of API keys. But nobody thought to look for it because the company believes everything’s internal,” co-founder and co-CEO Mike Baukes says. “It’s examples like that, which are things happening in the real world, that nobody’s had an answer for until now.”
Amazon has also offered a service called Amazon Macie, which uses machine learning to detect unusual access patterns in cloud storage and uploads of potentially sensitive data like access keys. Amazon also released open source software to prevent the accidental storing of passwords and keys to source code repositories, while other developers have offered similar tools to scrub credentials from existing code. According to Fast Company, those types of tools will be automatically provided as part of cloud computing contracts, just like standard seatbelts in a new car.
A Step-by-Step Guide to a Successful SIEM Deployment
SIEM (Security Information and Event Management) deployment based on firsthand experience implementing SIEM for a broad range of customers.
Discovery Phase - Laying the Groundwork
- Review the organizational security posture and the initial business case for SIEM. Then prioritize the goals of the SIEM implementation from the most critical to the optional—taking into account the tasks that must be performed in order to support the effort.
- Review in detail the organizational security policy to consider the intent behind the policy. Separate those policies from a priority standpoint. Determine what’s critical, what’s necessary for mandatory compliance and what policies are best practices to ensure a secure environment.
- Identify current controls that are auditing those policies to determine compliance level. Ideally, a SIEM implementation should not be the first time the organization identifies that its security policy or how it’s implemented isn’t working according to plan. The reality is that these deployments often expose gaps in security execution that must be remediated before those elements can be integrated into a daily alerting and reporting structure.
- Identify a smaller representative subset of the current policy and devices where SIEM can be applied and enough data can be gathered to determine what changes need to occur.
Pilot Phase - Beginning the Implementation
The primary goal of this phase is to determine which specific SIEM project goals can be implemented in order to establish initial ROI while creating a baseline operational model and run-book.
- The lessons learned from the discovery phase are used to implement a larger subset of technology.
- The assumptions developed during the discovery phase are tested in real time.
- The list of devices should be expanded to incorporate a wider set of technologies and numbers.
- The information developed from this phase is used to determine the final steps of controlled deployment and maturity phase.
Controlled Deployment Phase - Building Capacity
The primary goal of this phase is to develop a deployment workflow that enables the organization to build capacity as full deployment approaches. This phase also serves as the initial production test run and the completion of operational run-books necessary to manage a full deployment.
Maturity Phase - Continuing to Evolve
Significant work must be performed in order to mature the organization’s security posture and implement the finer points of the deployment. This phase never has an end point—since SIEM must continually evolve.
Cyber-Digital Task Force
The Department of Justice’s internal “Cyber-Digital Task Force,” created by Attorney General Jeff Sessions in February, will release its first-ever public report later this month at the Aspen Institute’s annual Security Forum, a department spokesperson told CyberScoop.
The report is expected to detail a series of security recommendations that the government should consider to protect future U.S. elections from a myriad of different threats, including foreign hacking attempts.
A statement by the DOJ previously explained that the Task Force will “prioritize its study of efforts to interfere with our elections; efforts to interfere with our critical infrastructure; the use of the Internet to spread violent ideologies and to recruit followers; the mass theft of corporate, governmental, and private information; the use of technology to avoid or frustrate law enforcement; and the mass exploitation of computers and other digital devices to attack American citizens and businesses.”
When Sessions launched the group earlier this year, he requested that an initial report be completed by June 30. The recommendations were submitted ahead of time, according to DOJ spokesperson Ian Prior. The answers are currently being reviewed ahead of publication.
The DOJ’s disclosure was made hours after the Democratic National Committee (DNC) issued a press release criticizing the department and Trump administration for missing various cybersecurity policy deadlines, including the June 30 submission. The agency contends that it in fact made the deadline, although the publication won’t occur for a few weeks. The Aspen Security Forum begins on July 18.
The creation of the Cybersecurity Task Force on Feb. 20 came less than a week after Special Counsel Robert Mueller indicted a group of Russian internet trolls for interfering in U.S. politics. The Russians allegedly ran an extensive social media campaign that worked to trick American voters in the run-up to the 2016 presidential election, the indictment claims.
Deputy Attorney General Rod Rosenstein is expected to make “an exclusive policy announcement” on July 19 at the Aspen Institute event.
Data Protection Officer- Consultants
Why do I need a Data Protection Officer?
While the desire to protect company, customer, and vendor information isn’t new, there are new laws that are requiring organizations to take a more active role in protecting their data. The EU recently passed the General Data Protection Regulation that requires certain businesses to have a Data Protection Officer. In order to comply with the rule, it has been estimated that nearly 28,000 DPOs will be needed by the end of 2018.
Specifically, the General Data Protection Regulation requires companies that process data with a public authority or that regularly monitor data subjects on a large scale to have a DPO and a plan in place to protect that data. It’s important to note that the rule not only effects companies that are biased in the EU, but also those that conduct business with its partner countries.
Because of the non-specific wording of the GDPR, one of the first steps that any company operating within the EU will need to take is to determine whether or not they are subject to the regulations in the law. It may be necessary to hire a security consultant on a short-term basis to determine this. Fortunately, CyberSecOp has plenty of experience in helping companies comply with EU law and IT security background that this position would require.
What is a Data Protection Officer?
In order to comply with the new regulation, a Data Protection Officer must have, “expert knowledge of data protection law and practices”. Additionally, the DPO must have a good understanding of the organizations' technical structure, organization, IT infrastructure, and technology.
It’s important to note that as long as an employee is capable of performing the basic functions of the role, there is no formal training requirement. This means that the job can be assigned to an existing employee. It is also permissible for an organization to hire an outside consultant or security firm to take on this role.
How will this affect my company?
Due to the massive penalties involved with ignoring the new GDPR, any company that meets the criteria and operates in at least some capacity in the EU will need to appoint a Data Protection Officer. For larger companies, this role is most likely already filled by a data security team. Small companies will most likely find it to be the most cost-effective to hire an outside company to handle its data security issues.
Mid-size companies, however, will likely struggle to come into compliance with this rule. Keeping a full-time Data Protection Officer on staff might prove to be cost prohibitive, but it’s also possible that contracting with an outside firm may also run up costs beyond a sustainable level. In many cases, the solution might be to find a professional with multiple skill sets who could act as the company’s Data Protection Officer while also performing other duties. CyberSecop have a team of security professionals dedicated to helping an organization in comping with GDPR and other data security frameworks.
Secure all networks, from the Internet?
In the coming years in 2019-2020, the active mobile users will cross the 5 billion mark globally, and add to this the number of tablet user will also increase. When we analyze these figures it is not difficult to estimate that there are more than 20 million IoT devices in the pipeline ready to hit the base by 2020. It means the above-given figures are all set to be part of the connected world.
All these devices mean lots of valuable data, and where there’s valuable data there are hackers trying to get access to it. Not only do we need to wrestle with new kinds of networks, many of them wireless, but we need to tackle the security of these networks while simultaneously tackling the massive scale of the problem.
Now imagine the kind of valuable data that will be churned out from these devices, and how it will be a gala time for the hackers to break into these devices and get access. No doubt we need to bring such device in our daily life, but the challenge is to get them all secured taking into account the massive breach in the line.
We asked vendors and resellers how they approach security of the WAN in this challenging environment
The internet is the network
The data center is no more the enter of the universe, but it is the Internet that new network that brings all the network closer to each other.
Mobile phone networks are rapidly being repurposed as a general-purpose data network over which voice calls are just one more application. Inside the telcos themselves, the core networking is already running over IP networks, and consumers are very comfortable with messaging applications that talk over IP networks instead of SMS. Devices in the field are adding LTE interfaces as a cheap and easy way to add networking capability to what were once disconnected devices.
“We have to rethink how we approach things,” Kopelke says. “We need to change our thinking from ‘How do I secure and protect the network?’ to ‘How do I secure and protect the data and applications?’”
Gavin Wilson, Asia-Pacific managing director at Cradlepoint “People expect to always be connected. Increasingly the connection is a mix of technologies, rather than a single layer-1 or layer-2 approach.” Instead of a loose collection of isolated technologies, the network is now an abstraction operating at a higher level, and there is no longer a functional difference between “the internet” of decades past and what all these modern mobile devices use to connect”.
The connected world and benefits
This ubiquitous networking is enabling associations to do things that basically weren’t conceivable previously. Without a system to send the information, gadgets in trucks or conveyed by field laborers would need to store information for later use. Presently they can stream a lot of information back to a server farm or straight into the cloud, and they can be inconsistent contact with different parts of the framework.
“The ability to get information out to remote people is a massive benefit, and, if a truck roll over on a delivery, an immediate duress notification can let others know the driver is in trouble,” says Michael Dyson, general manager at Advanced Mobile IT
“We also have digital signage that can be remotely updated,” Dyson says. “You can receive diagnostics from remote locations without having to send a technician out to the site and there are buses in New Zealand that can do on-board ticketing and have a GPS for accurate next-stop announcements.”
As it turned out to be consistently more steadily and reasonable, the requirement for the specialist like; satellite telephones, CB radios have dropped abruptly. These more seasoned technologies are turning into a fallback — as opposed to the essential strategy for building up correspondences. The generously higher transfer speed access, combined with the across the board accessibility of the supporting framework, influences the cost/to profit examination straightforward: you’d be distraught not to.
Security
Obviously, simply being associated isn’t sufficient. We likewise need to keep information and applications secure when they’re interfacing with an indistinguishable web from each content kiddie and solidified digital crime with a hunger for other individuals’ data.
“The traditional way to secure the WAN was using firewalls at each branch or backhauling branch traffic to a datacenter and use firewalls there to protect the traffic,” says Stree Naidu, vice president. Asia-Pacific and Japan for Cato Networks. “As long as we think about the firewall as a box that sits somewhere, that box defines the perimeter. But what if the perimeter was defined by a firewall that is everywhere? This is the notion of Firewall as a Service (FWaaS).”
Moving from the physical system of security that is as pervasive as the availability itself is it all about. “Systems that are secured from commencement is the name of the diversion. Rather than being a bit of hindsight or an extra, security in a world with no border implies heating it in from the start.
“It has to be about more than taking an appliance and virutalizing it,” says Zscaler’s Kopelke. “We say that’s just cloud-washing.”
Cato Networks’ Scree agrees. “The challenge most organizations face is how to extend enterprise-grade security to all their branches and mobile users globally,” he says. “Cloud networks with built-in network security can offer a way forward.”
“With users expecting a higher standard of service, these standalone appliances won’t cut it anymore,” says Dell EMC’s Elmarji. “You need to be able to provide full security on all connected devices, fast access to data, and 24/7 connectivity.”
While it’s still relatively early days for software-defined networks, it’s clear where the momentum is. Customers and resellers alike should be investigating how they can move to using software-based networking to create the secure, ubiquitous networks of the future
Corporate Information Security Steering Committee
Organizations are becoming increasingly aware that if they fail to implement successful security management processes, it could expose them to untenable risk.
The role of the corporate information security steering committee has become an essential tool in the quest for a coordinated corporate security strategy, for reducing duplication in security spending, taking control of complex infrastructures, and, ultimately, reducing security risk.
One of the first steps for many organizations has been to set up a common security team and embark on enterprise-wide information security programs. However, many of these teams have struggled to align corporate business objectives with strategic security investment.
META Group's research indicates that the majority of new security teams struggle to define and establish their corporate missions, scope, influence, and power bases. Furthermore, these security teams have poorly defined executive charters and operate without effective communications plans. The unfortunate result of such poor grounding is the temptation for newly established teams to immerse themselves in technology quests, searching for elusive enterprise-wide technical solutions.
In contrast, the most effective security organizations are those with clear responsibilities and well-defined processes based upon five primary organizational roles:
Leadership - this is the role of the chief information security officer who deals with both the day to day management of the security team as well as continuous communication of the importance and value of security measures
Analysis/design - these security analysts help information owners develop meaningful security policies as well as adequate security solutions
Security administration - these people look after the day to day administration of access rights, passwords, etc
Security operations - resources that continuously monitor the organization's security status and manage incident response procedures.
Awareness communication - resources that design and manage ongoing security awareness and training programs.
Executive custody and governance -represented by an information security committee
The role of the corporate security steering committee is to coordinate corporate security initiatives at the executive level and thus enable an organization to optimize spending, manage their infrastructure, and minimize security risk. Obtaining consensus and support for corporate-wide security initiatives is especially difficult in highly decentralized and multinational organizations with devolved authority and autonomy. In this type of organization, an executive governance body becomes essential.
Corporate information security steering committees (CISSC) must have a clear charter with a range of functions that should include:
Managing the development and executive acceptance of an enterprise security charter.
Assessing and accepting corporate-wide security policy (e.g., the corporate policy on security incident response, general behavioral approach). This function's primary objective is to ensure that business requirements are reflected in the security policy, thus ensuring that the procedure enables rather than restricts business operations.
Assessing any requests for policy exceptions from individual business units.
Assessing, accepting, and sponsoring corporate-wide security investment (e.g., identity infrastructure deployment, remote access infrastructure) and requests to be excluded from common investment.
Providing a forum for discussion and arbitration of any disputes or disagreements regarding common policy or investment issues.
Acting as custodian and governance body of the enterprise security program by ensuring visible executive support and monitoring progress and achievements. The role of a permanent governance structure reinforces the message that enterprise security becomes an ongoing, long-term initiative.
Assessing and approving the outsourcing of common security services and coordinating investment of inappropriate relationship management resources. As the lack of skilled resources increases the need to outsource operational services, executive due diligence, risk assessment, and ongoing effectiveness assessment must be coordinated through the steering committee.
Initiating ad hoc projects to investigate the advantages, disadvantages, risks, and costs of common security initiatives and advising the committee with appropriate recommendations.
Representing the executive (board of directors) or its nominated information governance body (e.g., an information executive board) in all corporate security matters. Reporting back to these forums on the activities and effectiveness of corporate security programs and investments.
Acting as custodian of corporate-wide strategic security processes (e.g., role analysis, data classification) by validating process ownership, responsibilities, and stakeholders.
Acting as the respondent to enterprise-level audit exceptions (i.e., those audit exceptions where a specific individual cannot be found to be responsible).
Coordinating and validating any external, security-related corporate communications plans and activities (e.g., in the event of a high-profile, publicized security breach).
Tracking major line-of-business IT initiatives to identify synergy opportunities or leverage security investment.
Governing trust relationships with major e-business partners.
It is essential that steering committee members can make decisions at meetings. This requires the active participation of senior executive business managers, or it must be a permanent subcommittee of an organizational information board. To prevent the committee from becoming an ineffective 'debating society' or forum for driving political agendas, the committee's scope, powers, and objectives should be documented and measured.
Typical members of an information security steering committee include all line of business managers, application owners, regional managers, IT managers, the IT director, the chief security officer, the corporate risk manager, and the chief internal auditor. A clear distinction must be made between the role of the CISSC (i.e., executive custody and governance) and the leadership role (i.e., day-to-day management of the security team) of the chief information security officer.
By developing the emerging role of the chief security officer (CSO) and the security team, enterprises can foster a holistic approach to information security - one that recognizes that policy, process, and communication are as important as technology.
Cloud to Streamline Security for Strategic Growth
As the technology director at Inspira Health Network, François Bodhuin and his staff have their work cut out for them, as they strive to support the organization’s strategic growth, stay on top of technology needs and keep patient data secure.
The New Jersey-based organization, in fact, is constantly looking to expand. “We are a medium-sized system, but we are very active in our expansion plans,” Bodhuin said, noting that the system now has more than 150 service locations in five counties. The health network is currently building a new hospital, adding a two- story patient tower to one of its existing hospitals, expanding its behavioral health program, renovating a satellite ER, recently opened a senior emergency department and purchased a regional medical transport company.
In addition, the Inspira technology department has developed an app to better serve all the patients that will flow into this continually growing health system. The app enables patients to request appointments, get directions to facilities, access a list of providers, view emergency department and urgent care wait times, pay bills and even participate in virtual visits.
So, it made perfect sense for Inspira to move its compliance management software to the cloud when FairWarning introduced a cloud-based managed shared services solution that works to ensure all data is secure by continually monitoring user activity and sending out alerts for any suspicious actions. After all, the health system had already moved a variety of systems to the cloud including its electronic health records, security information and event management (SIEM) and wound care solutions, and has experienced myriad benefits by doing so.
“The cloud saves costs; because you are getting a virtual server, the hardware itself costs less,” he said. In addition, when a managed services provider hosts a solution in the cloud, the healthcare organization does not incur on-boarding or ongoing training costs.
By hosting the compliance solution in the cloud under a managed services arrangement, Inspira will be positioned to:
Take advantage of a team of privacy and security experts. “The team concept to me is a key with managed services. We’re always being asked to work more efficiently. In this case, we will be able to really do that because we will have a team of experts that is performing the function,” Bodhuin said. “Because they’re experts, they know when a complaint is significant. They know when an alert is significant. They know when to ask for an investigation.” In addition, because these experts are well versed in the compliance solution, the learning curve that is typically associated with implementing a new solution is eliminated.
Reduce the need to search for IT staff. Hiring experienced, qualified IT staff is a challenge for all healthcare organizations. “In South Jersey, it is especially difficult to attract people to work in security and privacy. [With managed services], we don’t have to search for IT staff and we won’t have any onboarding costs. All that is built-in to our fees,” he said.
Maintain flexibility. With a managed solution in the cloud, it will be easy for Inspira to grow – as the organization does not need to add staff but can instead simply adjust the services agreement to meet evolving needs.
More readily deal with infrastructure challenges. With managed services, Inspira staff do not need to “worry about patching or managing the server,” he said. In addition, staff don’t need to be concerned with “upgrading the hardware, or the software . . . or worry about disaster recovery,” something that traditionally generates significant downtime, according to Bodhuin.
Leverage the experiences of many. Managed services providers work with a variety of organizations making it possible to “bring many best practices to the table,” which is difficult to do when hosting and maintaining systems internally, Bodhuin noted.
Save considerable time. “There's a lot of daily work that, all of a sudden, you don't have to do because it’s being done by the managed service. In privacy and security, we expect to regain about one to two hours a day for each analyst,” he said. “Now, they can focus their time on responding to issues that are reported to them. All that saved time can be allocated to another function.”
Doing managed services right
While Bodhuin expects to realize these benefits when moving the compliance software to the cloud, his past experience with managed services has provided a litany of lessons learned. More specifically, he knows that to successfully work with a managed services provider requires:
- Defining expectations explicitly. “You have to define what you trust them to do. You could let the managed service provider run the whole show if you wanted to, in certain functions,” or limit their scope to a defined set of functions, according to Bodhuin.
- Proactively managing the working relationship. “You really have to keep them on their toes. Make sure they deliver what they say they will deliver,” he advised. “So you really have to pay attention to your statement of work to ensure that you will get what you expect.”
- Treating the managed service provider as one of our own. “It’s really important that you make these people a part of your team. And if you do that, then you’ll get success. If you don’t do that, then there will be a lot instances where there are conflicts in your priorities,” Bodhuin said.
In the final analysis, with the expertise gained via a managed services arrangement, Bodhuin expects Inspira to save time, reduce costs while minimizing the organization’s overall risk profile. As such, Bodhuin can help the health system support its strategic growth goals. “The technology/security must be ‘a department of yes’, not a ‘department of no’. When you start saying no to people, you're going against the business itself and that can be a real problem,” he concluded.
Bypass Two-factor authentication - 2FA Bypass
A majority of users and companies are moving to Two-factor authentication (2FA) for enhancing the security of its data and systems. But contrary to popular belief, it cannot provide a fool-proof layer of security to online accounts since Kevin Mitnick at KnowBe4 has demonstrated that it is very easy to deceive this defensive measure.
KnowBe4 is the world’s leading security awareness training provider and simulated phishing firm with a massive customer base of 17,000 organizations across the world. Mitnick is the company’s chief hacking officer.
In his new exploit, he proved that 2FA is exploitable because hackers can spoof the 2FA requests by sending a fake login page to the user. This may lead to stealing of sensitive user data including username, password and session cookie.
The hacking technique can be seen in the video uploaded here:
The purpose of using 2FA is to add an extra layer of security by combining what an employee already has and what they know. This combination could be between username and password or a code that is sent to the user on the phone or an app.
To exploit the 2FA method of security, the victim is lured into visiting a typo-squatting domain such as LunkedIn.com in order to steal the required user data. Once the information is obtained, the hacker can easily access the actual website and capture session cookie. Once this is achieved, the hacker can remain logged in indefinitely. But this is reliant on accessing the 2FA authentication code once.
As per the CEO of KnowBe4Stu Sjouwerman, Kuba Gretzy, a white hat hacker, and friend of Mitnick, developed a tool for bypassing the 2FA authentication via social engineering techniques and this tool can be “weaponized” for just about any website.
“Two-factor authentication is intended to be an extra layer of security, but in this instance, we clearly see that you can’t rely on it alone to protect your organization,” added Sjouwerman.
The tool is called evilginx. The attack method is based upon proxying the user via the hacker’s system through a credentials phishing technique, which requires the use of a typo-squatting domain. The idea is to let the user give away his/her credentials so that the hacker could steal session cookie.
The phishing email is the core of the attack method. In this particular case, the phishing email is supposedly sent by LinkedIn to a member of the site indicating that somebody is trying to contact through the social network. The email looks authentic initially but if looked closely, it becomes evident that it is a fake email since the return address is incorrect. But, if the user falls for it and clicks on the “interested” button, the malware will soon be downloaded onto the device.
This is the stage when the victim is taken to the authentic LinkedIn website so as to enter login information, which the hacker required. The login information is recorded by the malware as well as the session cookie using the cookie, the attacker acquires direct access to the account and manages to avoid the 2FA phase of the signing-in process.
Watch The Demonstration Here
GDPR Questions Answered: Do We Need Consent to Hold Information in a Database?
Now just a few weeks remain before the deadline for the General Data Protection Regulation (GDPR), so data protection advisor Jon Baines is here to answer your questions.
Today, Jon was asked:
Q: “If our database holds names, email addresses, telephone numbers addresses and job roles of people involved in the classical music industry, of which most of the information is available on their websites, do we have to have specific consent to hold this information, which we use to contact them in terms of business and to occasionally send out a newsletter (twice a year) from which they can unsubscribe? There are a few thousand names involved so it would be good to know whether we need to contact them or not!”
A: “I wish my answer could be a simple one, but, regrettably, the law here is rather complex. However, I will try to explain.
“Unfortunately, what we don’t have here are details on how the business gathered this personal data, and whether the marketing they wish to send is by email (I’ve assumed it is). The author says the information gathered appears publicly on websites, so it might be inferred that the business has ‘scraped’ the details from those sites. If that’s the case, then there may be some problems.
“As a general rule people should be aware (or be made aware) that their personal data is being gathered and collated, even if it’s publicly accessible. Furthermore, sending marketing in electronic form to individual recipients (which I think most of the musicians here would be) requires explicit consent from the recipient (or, in some circumstances, and subject to various qualifications, a prior customer relationship). Sending email marketing, therefore, without consent, would almost certainly be a breach of the law.
“If, contrary to what I’ve inferred, the business got the musicians’ details direct from the musicians themselves, then the question as to whether they can send them email marketing is a bit different. If the business has their prior explicit consent to receive marketing emails, then they can continue to do so. Or if they got the musicians’ details during the sale (or negotiations for sale) of a product or service, they can send them marketing emails, provided that at all stages they have offered, and continue to offer, the option to opt out of receiving them.
“The irony here is that the law in question is not the GDPR but the Privacy and Electronic Communications (EC Directive) Regulations 2003, which often get overlooked. Over recent years the Information Commissioner has issued plenty of fines for breaches of this 2003 law.
“Generally, the firms getting those fines have sent very high volumes of unlawful electronic marketing, and the Commissioner has not tended to target SMEs. Nonetheless, even if the risk to a small business of big fines may be relatively low, they do need to be aware of the other risks, particularly of legal claims by individuals, and reputational harm.”
Ransomware campaign up around the world
A new email ransomware campaign is spreading around the world. Researchers at Fortinet say it’s a spam effort, meaning the messages are not targeted. Instead they are addressed generally, like “Dear customer.” The subject line in the email would be something like “Document number…”, “Your order number” or “Ticket number.” With the email is a malicious attachment that leads to the installation of malware. The initial targets are corporate mail servers used to forward this email. These have been found in Canada, the U.S. the United Kingdom and other countries.
The best defense against ransomware – or any email-delivered malware – is to watch out for it. Be cautious about unsolicited emails, especially those with attachments. And it’s vital you always have a separate backup of your data made it a way that can’t be infected, just in case you make a mistake.
Meanwhile McAfee reports some Canadian organizations have been victimized by a separate operation. A group security that researchers call Hidden Cobra, believed to be backed by North Korea, has been putting surveillance software on the systems of companies. The suspicion is the Canadian victims have been used as listening or data relay points. The malware that this campaign has installed has not stolen financial or sensitive data but appears to be there find out what’s on a computer, and be ready to launch further attacks.
Companies have to make sure their systems have the latest security patches. In addition, because the malware appears to be distributed through email, employees have to be reminded to be careful on what they click on.
For more on this see my story today on ITWorldCanada.com.
The U.S. National Security Agency has just suffered a black eye from an international standards body. According to a blog on Bitdefender, the International Organization of Standardization – known more commonly as ISO – rejected two new encryption algorithms suggested by the NSA to secure Internet of Things devices. The algorithms would scramble information on Internet-connected devices like home surveillance cameras and toys. But the NSA’s reputation for creating tools to hack into applications apparently give it a bad name at the ISO. One ISO delegate accused the NSA of telling half-truths and lies in its presentation.
If that allegation is accurate, it isn’t good. Internet of Things devices badly need better security. People and companies around the world buy tens of thousands of them a year. Insecure devices don’t improve security.
That’s it for Cyber Security Today. Subscribe on Apple Podcasts, Google Play, or add us to your Alexa Flash Briefing. Thanks for listening.
CISO Roles Expanding - Global Risk Management
Traditionally, the mission of the CISO has been to convince the CEO of the capabilities the organisation must put in place to prevent and follow-up on threats and manage crises. At the helm of IT security, CISOs are in their element overseeing the security operations centre (SOC), incident response teams and forensics experts to address threats. But now, many are being forced outside of their comfort zone. With global attacks dominating television news and headlines in Europe, US and the UK, cybersecurity is top of mind for CEOs and their Boards. And this means that the role of the CISO is expanding.
The Evolving Role of the CISO: Handling a Crisis When You Aren’t Under Attack
According to Aon’s 2017 Global Risk Management Survey, cybercrime is now number five among the top 10 concerns for risk decision-makers globally, above failure to innovate, failure to attract and retain top talent, business interruption, political risk/uncertainties and third-party liability. Each time a high-profile attack happens, the CISO gets a phone call from the CEO asking questions like: Are we at risk? Should we be doing something? It is no longer enough to let the CEO know that the organization has not yet been attacked. CISOs need to expand their leadership role and actively engage in risk management.
I have had the opportunity to speak with many CISOs who validate that their jobs are changing.
“Before, we had to fight to explain to the CEO that it would be interesting to know what was coming in and out of our systems,” said Benoit Moreau, CISO of the French ministry of national education and research. “Now, we are expected to have a fine perception of each element of our ‘information ecosystem’ and the interactions that drive it to succeed to predict, almost in real time, the consequences of any stimulus. Our systems have undergone a dazzling Darwinian evolution, driven by new technologies and uses. They went from monocellular organisms that were individually secured to complex protean organisms close to life.”
Today, when the external threat landscape changes and the CEO inevitably calls, CISOs need to respond differently. They need to have situational understanding, be prepared to make decisions on the spot and communicate how they will ensure risk remains at an acceptable level. Moreau explains, “The CISO must equip himself to have ‘awareness’ of the security infrastructure as a whole – to feel the problems, to detect the symptoms. He must understand weaknesses, threats and health risks. He must strengthen his defenses, have the means to carry out further analysis in case of doubt, to inoculate or provide other treatments, and even to amputate in the event of the spread of deadly agents. It is no longer a question for the CISO to deploy some white blood cells, but to be the healthy mind in a healthy body, a robust organism with an effective immune system.”
As a CISO, what does it take to embrace this important change in your role? To begin with, you need instant access to as much information as possible about an attack or campaign. This includes an adversary’s targets and motivations; their tools, techniques, and procedures (TTPs) including tactics and vulnerabilities that may put the organization at risk; as well as the countermeasures available.
Most organizations already have much of this information, but it is spread across many different departments, in multiple external threat data feeds, in your layers of security products, in your SIEM that store logs and events and in analysts’ brains. What you need is a single source of truth – a centralized repository for all this data that you can continuously augment and enrich so that it is contextualized, relevant and prioritized. With a hub for storing, updating and accessing threat intelligence, your teams can learn and share knowledge to assess whether a threat poses short-term danger and determine the appropriate actions. But barriers remain.
Traditionally, siloed teams work independently and in a vacuum without the ability to collaborate throughout the analysis process and execute a coordinated response as needed. Working on parallel tasks, they can miss key commonalities. All teams must be able to work together in a single shared environment for a greater understanding and focus throughout the situation analysis and response process. Using visualization and documentation they can quickly see threat data, evidence, and actions across all the various departments and individual involved in the investigation.
With visibility into this collaborative environment and the situation analysis as it unfolds, CISOs can coordinate between teams and actions taken. A global picture provides the information you need to reply with greater confidence to your CEO’s questions. You can gauge if you’re adequately prepared to withstand an attack and let your CEO know. Or, if not, you can direct the appropriate action faster and assure your CEO you’re taking the right actions to mitigate risk.
Reacting to massive, global threats is a new phenomenon and a new responsibility added to CISOs’ day-to-day tasks. The moment you become aware of a potential new attack, you must be able to assess risk, anticipate potential impact and start crisis management. When a threat is detected, you must be able to respond quickly and comprehensively while maintaining business continuity. It’s no longer enough to protect the organization from an attack – you must be able to handle a crisis even if you aren’t under attack.
(NIST) Framework Cyber Security Updated
Four years after the initial iteration was released, the National Institute of Standards and Technology (NIST) released version 1.1 of the Framework for Improving Critical Infrastructure Cybersecurity.
The framework was developed to be a voluntary, risk-based framework to improve cybersecurity for critical infrastructure in the United States. A President Obama-issued executive order calls for developing a set of standards, guidelines, and practices to help organizations charged with providing the nation’s financial, energy, health care, and other critical systems better protect their information and physical assets from cyberattacks.
Like the first version, Version 1.1 of the framework was created through public-private collaboration via recommendations, drafts, and comment periods. Version 1.1 includes updates on authentication and identity, self-assessing cybersecurity risk, managing cybersecurity within the supply chain, and vulnerability disclosure, among other changes.
The update has renamed the Access Control Category to Identity Management and Access Control to better account for authentication, authorization, and identity-proofing.
It also has added a new section: Section 4.0 Self-Assessing Cybersecurity Risk with the Framework explains how the framework can be used by organizations to understand and assess their cybersecurity risk, including the use of measurements.
On the supply-chain front, an expanded Section 3.3 helps users better understand risk management in this arena. In contrast, a new section (3.4) focuses on buying decisions and the use of the framework in understanding risk associated with commercial off-the-shelf products and services. Additional risk-management criteria were added to the Implementation Tiers for the framework, and a supply-chain risk-management category has been added to the Framework Core.
Other updates include a better explanation of the relationship between Implementation Tiers and Profiles; added clarity around the term “compliance,” given the variety of ways an organization can use the framework; and the addition of a subcategory related to the vulnerability disclosure lifecycle.
“This update refines, clarifies, and enhances Version 1.0,” said Matt Barrett, program manager for the Cybersecurity Framework. “It is still flexible to meet an organization’s business or mission needs. It applies to various technology environments such as information technology, industrial control systems, and the Internet of Things (IoT).”
Its goal is to be flexible enough to be adopted voluntarily by large and small companies and organizations across all industry sectors and federal, state, and local governments.
Nist 1.1
The release of the Cybersecurity Framework Version 1.1 is a significant advance that truly reflects the success of the public-private model for addressing cybersecurity challenges
“The release of the Cybersecurity Framework Version 1.1 is a significant advance that truly reflects the success of the public-private model for addressing cybersecurity challenges,” said Walter Copan, NIST director. “From the very beginning, the Cybersecurity Framework has been a collaborative effort involving government, industry, and academia stakeholders.”
So far, adoption of the framework has been relatively widespread: PwC’s 2018 Global State of Information Security Survey (GSISS), for instance, found that respondents from healthcare payer and provider organizations, as well as oil and gas companies, said the NIST Cybersecurity Framework is the most commonly adopted set information security standards in their respective industries. The report also found that financial institution clients widely embraced benchmarking their cyber risk management programs against the NIST Cybersecurity Framework.
“Cybersecurity is critical for national and economic security,” said Secretary of Commerce Wilbur Ross. “The voluntary NIST Cybersecurity Framework should be every company’s first line of defense. Adopting version 1.1 is a must-do for all CEOs.”
Efforts to expand its influence are continuing: In May 2017, President Trump issued the Executive Order on Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure, which directs all federal agencies to use the Cybersecurity Framework. Also, NIST noted that corporation,s, organizations, and countries around the world, including Italy, Israel, and Uruguay, have adopted the framework or their adaptation.
Meanwhile, to help ease the adoption process, the Information Security Forum (ISF) has mapped the framework and its annual Standard of Good Practice for IT security professionals. Last year, IT governance organization ISACA launched an audit program aligning the NIST framework with COBIT 5, designed to provide management with an assessment of the effectiveness of an organization’s plans to detect and identify cyber-threats and protect against them.
“We’re looking forward to reaching more industries, supporting federal agencies, and especially helping more small businesses across the U.S. benefit from the framework,” said Barrett.
Later this year, NIST plans to release an updated companion document, the Roadmap for Improving Critical Infrastructure Cybersecurity, which describes crucial development, alignment, and collaboration areas.
“Engagement and collaboration will continue to be essential to the framework’s success,” said Barrett. “The Cybersecurity Framework will need to evolve as threats, technologies, and industries evolve. With this update, we’ve demonstrated a good process for bringing stakeholders together to ensure the framework remains a great tool for managing cybersecurity risk.”
Small Business Benefits from Cybersecurity Consulting Services
Cybersecurity news stories are becoming more and more prevalent, especially over the last few years. Whether the stories are about stolen emails or huge data breaches, it has been virtually impossible to ignore them.
While the major stories about compromised corporations and hacked email accounts make the news, cybersecurity is something that concerns everyone who uses a computer. Even small business owners can become victims of cybercrime. In fact, small business owners, in particular, need to be concerned with cybersecurity so they can protect their intellectual property. No matter whether the intellectual property is research or recipes, it is one of the greatest assets a small business has. Intellectual property is a prime target for hackers, whether they are stealing information for a competitor or running a ransomware scheme where a hacker demands something in return for the stolen information.
The trouble is that protecting that intellectual property and keeping other sensitive information, such as client and customer data, isn’t cheap. Many small business owners may not have the available capital to afford a cybersecurity system. Although this puts an owner in a tough spot, you can’t put a price on peace of mind, and neither can a small business owner afford the losses associated with becoming the victim of a cybercrime.
As with most things for small-business owners, cybersecurity comes down to a cost analysis. A cybersecurity system can be a big expense. On the other hand, a small business owner has to consider the cost of not having their systems protected from hackers. It’s hard enough for a large corporation to recover from a cyber attack, even with all the resources and infrastructure they have. According to the U.S. National Cyber Security Alliance, 60 percent of small businesses fold within six months of a cyber attack.
Ultimately, each business owner has to decide if and when a formal data security protection plan is necessary. A consultation with an expert may help you better weigh the pros and cons of taking on this type of business expense. Start with this list of Cybersecurity Consulting Providers as a jumping off point for your research. After comparing the benefits of these companies’ plans, set up a few consultations to see if and how these providers can best help protect your business, and what it costs to do so. You may find that it’s worth the investment.
Are you ready for GDPR compliance?
GDPR Is Coming. Are You Ready
What is the GDPR requirements:
EU Compliance - General Data Protection Regulation (GDPR
For more details on GDPR see GDPR a risk to your organization
Cyber Security Developments
Cyber Security Is The Backbone Any Online Businesses – Here Are Some Quick Tips To Keep Yourself Informed About The Latest Threats Surrounding Your Business.
Cyber Security Developments
Within a standard nine to five working day, it’s said that there are almost two million data records lost or stolen. Cybercrime has become something of an epidemic in recent years – and it’s no exaggeration to say that everyone is at risk.
Hackers operate in an increasingly complex way and are happy to target small businesses and individuals, who are most likely to be vulnerable to attack. The nature of the threat changes as technology advances and so the only way to stay safe is to stay up to date.
But that’s easier said than done, right? How do you keep up to date with the latest cybersecurity developments?
Follow The News
When it comes to cyber security, ignorance is not bliss – it’s a recipe for disaster. It’s imperative that you identify and follow a news feed that you can trust. By doing so, you can keep on top of any fresh threats that have emerged, learn lessons from other cyber attacks and pick up the latest tips and advice from influencers and experts in this field.
News from this sector really shouldn’t be seen as the preserve of IT specialists – the scale and nature of the threat suggest that this should be of interest to everyone. There’s a burgeoning band of podcasts available on the subject for people who prefer to digest content in this way too.
Bring Up The ‘Security Question’
If you think that installing an anti-virus program is enough, then you’re mistaken. Don’t just presume that you’re safe because you have this because this is merely the first line of defense to root out attacks. By adopting a safety first mindset you can ensure that the way you handle your data is less risky.
Whether it’s securing your Wi-Fi network at home, managing and updating your passwords on a regular basis or the way you collect, collate and analyze data throughthe point of sale software at work, continually ask yourself ‘is this safe?’ Just as ignorance isn’t bliss, complacency could prove your undoing. Place ‘security’ high on the list of credentials to consider when buying new software or hardware, don’t just go for the cheapest option.
Training
Even the experts are constantly having to refresh their understanding of the threat posed by cyber attacks. It pays to search out training opportunities, especially if you’re a business. You are, after all, only as safe as the people operating your software and systems and you don’t want to put the security of your business in the hands of someone who is unsure about what they are doing. Individuals and businesses alike can find free learning materials on Cybrary to help plug any knowledge gaps they have.
It’s Good To Talk
Cyber attacks are incredibly common – but people don’t often enough talk about their experiences. Perhaps you’re afraid or embarrassed to have been caught out? There’s no need to be. In fact, talking with friends and colleagues could really help you to stay safe. Pass on tips about new apps, good software, neat tips and tricks and any new cyber attack tactics you have come across and you can help to do your own bit to combat the criminals.
By keeping up to speed with security news, refreshing your training, sharing tips and tricks and adopting a safety first attitude you’ll give yourself the best possible chance of staying on top of cyber security developments and, best of all, safe.