CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
Vishing Awareness
Vishing
Spoofing a legitimate phone number, voice phishing scammers lead people to believe the call is legitimate
What is Vishing?
We’ve all heard the countless stories on phishing and how much of a threat is it in today’s information security landscape. Social engineering to solicit confidential information via email is a threat that all of us have been made aware of. Extensive efforts have been made to not only reduce the influx of phishing emails, but also to raise awareness so that users have the know-how to assess and respond to the threat when a malicious email hits their inbox.
In response, threat actors have turned to a newer form of exploitation: Vishing. Vishing is a form of criminal phone fraud that uses social engineering over the phone or SMS to gain confidential information. Here are some examples
Fake call from “Help Desk” asking for credentials
Unsolicited calls for credit and loans
Calls from a fake client asking about an invoice
Vishing is becoming an increasingly favored tool attackers use, due to the Covid-19 pandemic. With the shift to work-from-home environments, corporate VPNS, and elimination of in-person verification, threat actors are shifting their tactics to exploit this widespread weakness.
How do I protect my firm against Vishing?
Security awareness is the best line of defense against this type of attack, so be sure to incorporate vishing education into your information security awareness program. Policies and procedures should be established and communicated to ensure that employees can verify identity when the helpdesk or anyone else from the company calls and asks after proprietary topical information. It is imperative that information security managers instill a sense of suspicion for any caller asking for said information.
Enabling MFA for any system that has access to confidential information, network or system is non-negotiable; that second factor of authentication can halt many types of attacks. When you enable MFA you avoid the use of SMS as a means of authentication as SMS is easily manipulated and exploited.
Lastly, always apply least privilege so that in the event an account is compromised, there will be minimal damage.
AUTHOR: CARLOS NETO
Information Security Officer
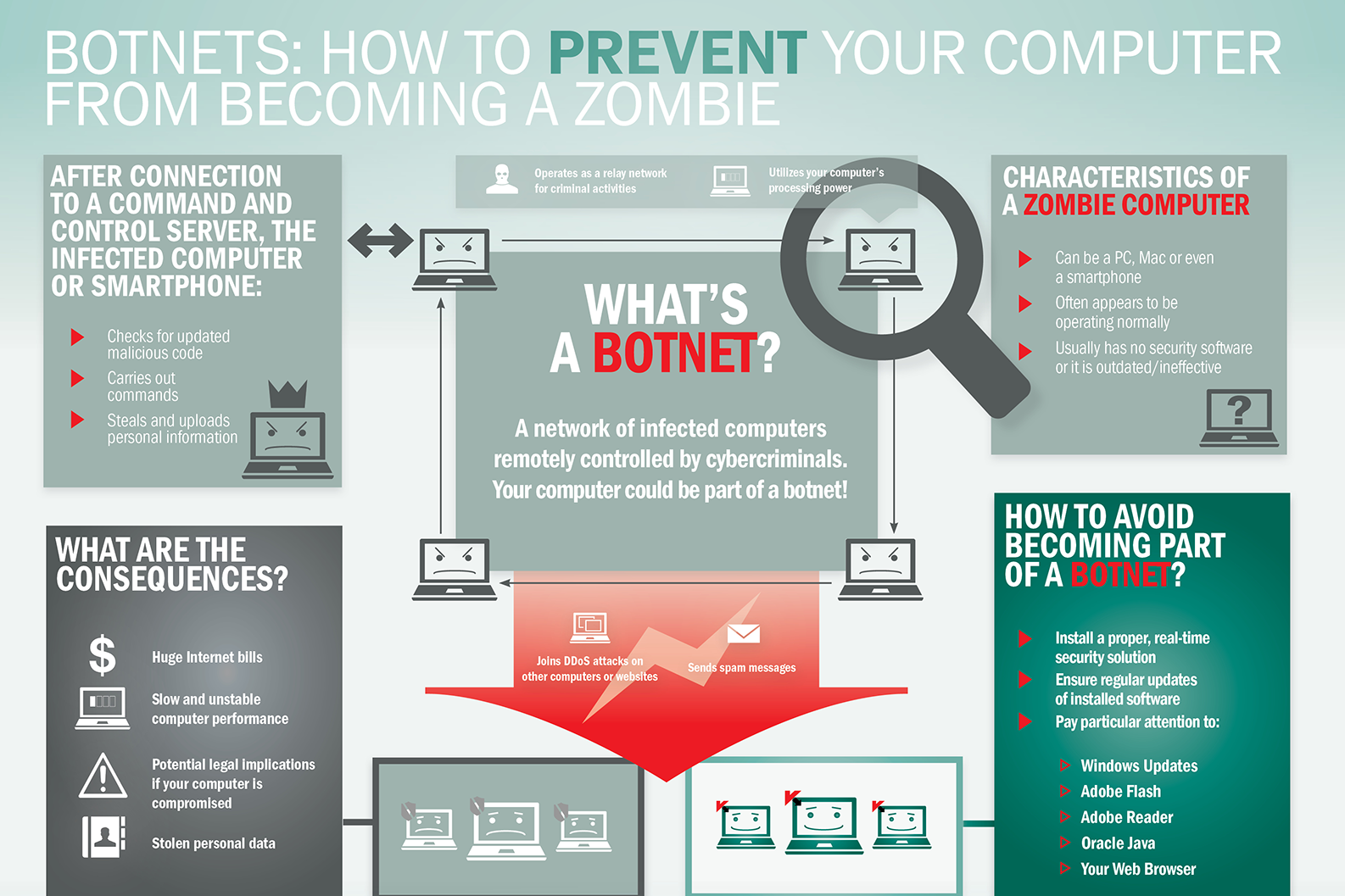
What is Botnet - Cybercriminals #1 Weapon
The word Botnet is formed from the words ‘robot’ and ‘network’. Cybercriminals use special Trojan viruses to breach the security of several users’ computers, take control of each computer and organise all of the infected machines into a network of ‘bots’ that the criminal can remotely manage.
Botnet Prevention- What is Botnet
How Botnets can impact you
Often, the cybercriminal will seek to infect and control thousands, tens of thousands or even millions of computers – so that the cybercriminal can act as the master of a large ‘zombie network’ – or ‘bot-network’ – that is capable of delivering a Distributed Denial of Service (DDoS) attack, a large-scale spam campaign or other types of cyberattack.
In some cases, cybercriminals will establish a large network of zombie machines and then sell access to the zombie network to other criminals – either on a rental basis or as an outright sale. Spammers may rent or buy a network in order to operate a large-scale spam campaign.
How to prevent your computer becoming part of a Botnet
Installing effective anti-malware software will help to protect your computer against Trojans and other threats.
Bypass Two-factor authentication - 2FA Bypass
A majority of users and companies are moving to Two-factor authentication (2FA) for enhancing the security of its data and systems. But contrary to popular belief, it cannot provide a fool-proof layer of security to online accounts since Kevin Mitnick at KnowBe4 has demonstrated that it is very easy to deceive this defensive measure.
KnowBe4 is the world’s leading security awareness training provider and simulated phishing firm with a massive customer base of 17,000 organizations across the world. Mitnick is the company’s chief hacking officer.
In his new exploit, he proved that 2FA is exploitable because hackers can spoof the 2FA requests by sending a fake login page to the user. This may lead to stealing of sensitive user data including username, password and session cookie.
The hacking technique can be seen in the video uploaded here:
The purpose of using 2FA is to add an extra layer of security by combining what an employee already has and what they know. This combination could be between username and password or a code that is sent to the user on the phone or an app.
To exploit the 2FA method of security, the victim is lured into visiting a typo-squatting domain such as LunkedIn.com in order to steal the required user data. Once the information is obtained, the hacker can easily access the actual website and capture session cookie. Once this is achieved, the hacker can remain logged in indefinitely. But this is reliant on accessing the 2FA authentication code once.
As per the CEO of KnowBe4Stu Sjouwerman, Kuba Gretzy, a white hat hacker, and friend of Mitnick, developed a tool for bypassing the 2FA authentication via social engineering techniques and this tool can be “weaponized” for just about any website.
“Two-factor authentication is intended to be an extra layer of security, but in this instance, we clearly see that you can’t rely on it alone to protect your organization,” added Sjouwerman.
The tool is called evilginx. The attack method is based upon proxying the user via the hacker’s system through a credentials phishing technique, which requires the use of a typo-squatting domain. The idea is to let the user give away his/her credentials so that the hacker could steal session cookie.
The phishing email is the core of the attack method. In this particular case, the phishing email is supposedly sent by LinkedIn to a member of the site indicating that somebody is trying to contact through the social network. The email looks authentic initially but if looked closely, it becomes evident that it is a fake email since the return address is incorrect. But, if the user falls for it and clicks on the “interested” button, the malware will soon be downloaded onto the device.
This is the stage when the victim is taken to the authentic LinkedIn website so as to enter login information, which the hacker required. The login information is recorded by the malware as well as the session cookie using the cookie, the attacker acquires direct access to the account and manages to avoid the 2FA phase of the signing-in process.
Watch The Demonstration Here