CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
CEOs / CISOs Cybersecurity Plans For 2023 and 2024 (Copy)
CEOs and CISOs have a crucial role in ensuring cybersecurity for their organizations. Their focus is on protecting sensitive information and critical assets from cyber threats such as data breaches, hacks, and cyber attacks. To achieve this, they must implement a comprehensive cybersecurity strategy that addresses all aspects of security, including people, processes, and technology.
Regarding people, CEOs and CISOs must ensure that employees and contractors are trained in cybersecurity best practices and aware of their roles and responsibilities when it comes to protecting company data. They should also implement policies and procedures that promote a culture of security and accountability throughout the organization.
Regarding processes, CEOs and CISOs must establish and enforce policies and procedures that govern how information is accessed, used, and stored. They must also ensure that security measures are integrated into all stages of the software development lifecycle and that regular security assessments are conducted to identify vulnerabilities and risks.
Regarding technology, CEOs and CISOs must deploy and maintain a suite of security technologies that are designed to protect against cyber threats. This includes firewalls, intrusion detection systems, antivirus software, and encryption tools, among others. They must also stay current with the latest security trends and technologies and be prepared to implement new measures as needed to address emerging threats.
Overall, CEOs and CISOs must work together to develop and implement a holistic cybersecurity strategy that addresses people, processes, and technology. By doing so, they can help protect their organizations from cyber threats and maintain the confidentiality, integrity, and availability of their data and assets.
CEOs and CISOs are focused on ensuring cybersecurity through a combination of people, process, and technology measures.
Some of the steps that CEOs and CISOs may take to ensure cybersecurity in 2023 include:
Increasing awareness and training: CEOs and CISOs may focus on increasing employee awareness of cybersecurity risks and providing training to help employees identify and avoid potential threats.
Strengthening policies and procedures: CEOs and CISOs may review and update their organization's policies and procedures to ensure they are aligned with the latest industry best practices and regulations.
Implementing advanced technologies: CEOs and CISOs may leverage advanced cybersecurity technologies, such as AI-powered threat detection and response tools, to improve their organization's ability to identify and respond to threats.
Conducting regular audits and assessments: CEOs and CISOs may conduct regular cybersecurity audits and assessments to identify potential vulnerabilities and develop plans to address them.
Artificial Intelligence Enhances Cyber Security
AI is playing a critical role in protecting organizations by providing advanced threat detection and response capabilities. AI-powered cybersecurity tools can analyze vast amounts of data in real-time to identify patterns and anomalies that could indicate a potential threat. AI can also help automate the incident response process, enabling organizations to respond to threats faster and more effectively.
Furthermore, AI is also used to improve the security of the software development lifecycle (SDLC) and the security of software applications themselves. By automating security testing and analysis, AI can help identify vulnerabilities in applications before they are deployed, reducing the risk of cyber attacks.
In summary, CEOs and CISOs are likely to focus on a combination of people, process, and technology measures to ensure cybersecurity in 2023, and AI is playing a critical role in protecting organizations by providing advanced threat detection and response capabilities and improving the security of the SDLC and software applications.
Cyber security IT skills in-demand in US
There’s no doubt that demand for the technologically skilled will only increase in the upcoming years, as practically every company becomes a software-driven enterprise. A survey by the jobs site Monster found that in the US, jobs in the digital sector have multiplied at more than twice the rate of other non-digital tech sectors, and are predicted to grow by 20% in the next decade.
However, which skills will be particularly in demand? While it’s unlikely that the IT skills demanded by the jobs market today will become redundant within our lifetimes, the field is constantly evolving, and there are certainly growth areas on the horizon that IT professionals would do well to educate themselves in.
Cyber security
Cyber security is an area set to grow exponentially in importance in the upcoming years. Every time a breach is suffered by an organisation, there is a huge cost both in terms of financial loss and loss of reputation and brand value.
A recent study carried out by jobs site Indeed indicated that the US is dangerously short on cyber security skills and that the number of cyber security jobs advertised in the US is the third highest globally, meaning demand exceeded candidate interest by more than three times.
Development
Demand for skills in development is here to stay (for the time being anyway – this could change as soon as AI is more widely used to code). In 2017, the demand for software developers and engineers increased by 13% in the UK.
Devops
Another important area of growth is the trend for companies to take a devops approach to their IT departments, meaning that developers well versed in this outlook will be the most employable.
Cloud computing
It’s widely recognised that cloud computing is the future, and every IT professional should feel comfortable using these systems. Demand for cloud infrastructure specialists is increasing across the board.
Machine Learning and AI
These are two obvious areas of increasing growth. In the US, demand for AI jobs increased threefold between 2015 and 2018, even surpassing the UK in terms of demand.
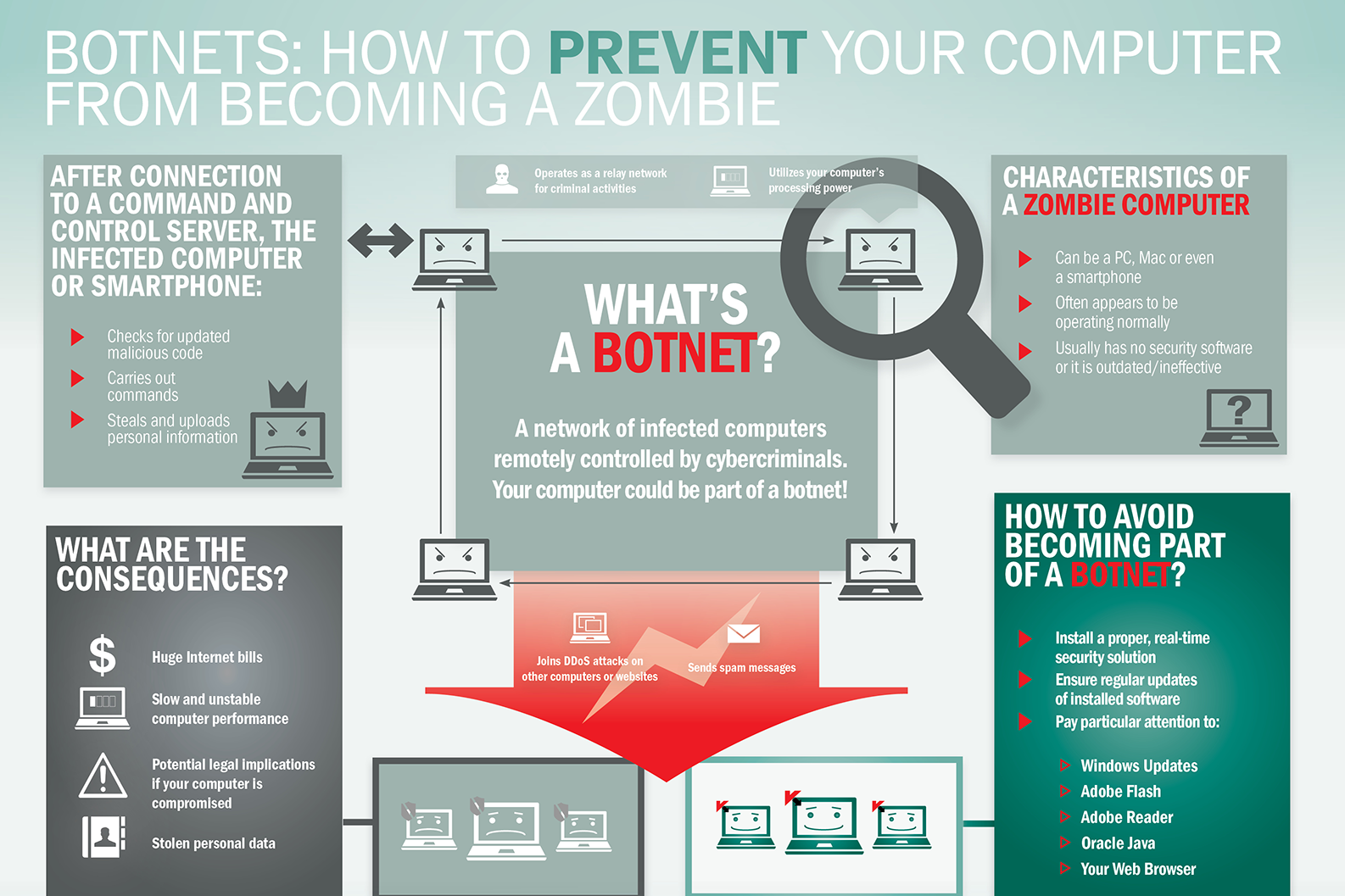
What is Botnet - Cybercriminals #1 Weapon
The word Botnet is formed from the words ‘robot’ and ‘network’. Cybercriminals use special Trojan viruses to breach the security of several users’ computers, take control of each computer and organise all of the infected machines into a network of ‘bots’ that the criminal can remotely manage.
Botnet Prevention- What is Botnet
How Botnets can impact you
Often, the cybercriminal will seek to infect and control thousands, tens of thousands or even millions of computers – so that the cybercriminal can act as the master of a large ‘zombie network’ – or ‘bot-network’ – that is capable of delivering a Distributed Denial of Service (DDoS) attack, a large-scale spam campaign or other types of cyberattack.
In some cases, cybercriminals will establish a large network of zombie machines and then sell access to the zombie network to other criminals – either on a rental basis or as an outright sale. Spammers may rent or buy a network in order to operate a large-scale spam campaign.
How to prevent your computer becoming part of a Botnet
Installing effective anti-malware software will help to protect your computer against Trojans and other threats.
What advice does the world's first CISO have
What advice does the world's first CISO have for the current generation of CISOs? Stephen Katz emphasizes, first and foremost, that cybersecurity must be treated as a business risk management issue rather than a technology issue.
"Security has to evolve and grow at the same pace as the business," he stresses in an interview with Information Security Media Group.
The role of the CISO has to be recognized as a core business function, he adds. "Security has to be an enabler of the business; security has to earn a seat at the executive table. Too often, we give people the title of chief information security officer; they don't believe they're an executive, and executives don't believe they are an executive."
In this interview (see audio link below photo), Katz also discusses:
Changes in the threat landscape since becoming the world's first CISO;
Top priorities for CISOs in the coming year;
Why getting back to the basics of security remains so important;
The ongoing growth of machine learning models in all aspects of cybersecurity.
Katz is the founder and president of Security Risk Solutions LLC, an information security company providing consulting, mentoring, coaching and advisory services. He was formerly CISO at JPMorgan Chase, Citigroup and Merrill Lynch.