CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
CyberSecOp is an ISO 27001 Certified Cyber Security Consulting Firm
CyberSecOp is proud ISO 27001 Certified Organization
The team at CyberSecOp is ISO/IEC 27001:2013 (ISO 27001) certified.
International Organization for Standardization (ISO) is an internationally recognized standard that ensures that firms such as CyberSecOp, meet best practices for information security management systems and vigorous risk-based framework approach.
We are committed to following a high-quality and consistent security management system. A-lign, an independent, third-party auditor, found CyberSecOp to have technical controls in place and formalized IT Security policies and procedures. A-lign is an ISO / IEC 27001 certification body accredited by the ANSI-ASQ National Accreditation Board (ANAB) to perform ISMS 27001 certifications. Therefore, through ISO 27001, we have developed and implemented processes and procedures in order to provide requirements for establishing, implementing, maintaining, and continually improving an information security management system. The entire certification leads us to the appropriate requirements for an Information Security Management System (ISMS) in our company — a systematic approach to managing sensitive company information so that it remains secure. It includes people, processes, and IT systems by applying a risk management processes.
Achieving the ISO 27001 certification is the result of a great amount of effort, dedication, and involvement from every member of the CyberSecOp team. We are constantly challenging ourselves to improve our service and provide the highest security and privacy standards to meet or exceed the needs and expectations of our customers.
Author: Carlos Neto
Information Security Officer
Top 14 Cyber Security Vendor Due Diligence Questions
What is a cybersecurity vendor due diligence questionnaire? Vendor cyber security due diligence questionnaire is a prewritten assessment gain visibility into supplier or vendor cybersecurity posture. Vendor cyber security due diligence questionnaire assist organizations with identify potential risks before onboarding vendors/suppliers.
CyberSecOp vendor management program supports multiple compliance requirement. The following four and other regulations are set forth by different regulatory bodies across the globe for various purposes, including the protection of financial, personal, and healthcare information.
- PCI DSS (The Payment Card Industry Data Security Standard). This is the information security standard for organizations handling branded credit cards.
- GDPR (The General Data Protection Regulation). This legal framework sets guidelines for the collection and processing of personal information for those living in the European Union (EU).
- HIPPA (Health Insurance Portability and Accountability Act of 1996). This U.S. legislation provides data privacy and security for safeguarding all medical information.
- OCC (The Office of the Comptroller of the Currency). This federal agency oversees the execution of laws for national banks, and functions to regulate and supervise banks in the United States.
Reputation Risk
Reputation risk refers to negative public opinion or customer perception that stems from irresponsible vendor practices. Unsecure vendor remote access can lead to a number of problems that may destroy customer relationships and harm your company's reputation, including:
- Customer complaints
- Dissatisfied customers
- Interactions inconsistent with company policies
- Security breaches resulting in the disclosure of customer information
- Violations of laws and regulations
Operational Risk
Operational risk results from internal breaches, processes, and system failures. Third-party vendors are increasing as an extension of operational risk since they are closely tied to operational processes and business practices. Operational risks may be caused by:
- Employee error
- Failure to adhere to internal policies
- Internal and external fraud or criminal activity
- System failures
Top 14 Cybersecurity Vendor Due Diligence Questionnaire
they have a security contact or chief information security officer in place? If a third party deploys dedicated resources to manage risks and safeguard its critical information, it shows they take their security posture with the utmost seriousness.
Do they have industry certification, or are they aligned with an industry framework such as NIST/ISO? While industry certification may not necessarily indicate the effectiveness of third-party security controls, it does provide additional assurance about the vendor's commitment to protecting their systems and customers' information.
Are penetration tests performed by a qualified third-party vendor? If so, how often are they performed and when was the last test performed? Ensuring your vendor has regularly scheduled penetration tests performed by a third party is essential in knowing how secure their environment is and where the weaknesses are so they can be secured before they’re exploited by an attacker.
Is there a formal information security program in place? A security program provides the framework for keeping a company at a desired security level by assessing the risks that are faced, deciding how those risks will be mitigated and planning for how to keep the program and security practices current.
Do they have a mature threat management and intelligence program in place? It's important to ascertain the effectiveness of their security controls. This can be done by reviewing independent security audit reports to assess the vendor's vulnerability management, secure software development processes and threat management programs, such as cyber intelligence.
Is there a formal logical access review process? Having regularly scheduled access reviews of users is essential in knowing who should have access to your system and who no longer needs access. Failures in logical access review procedures are the top reason for exceptions in SOC reports.
How has your vendor implemented the principle of least privilege? Role-based access privileges are vital in only allowing employees to have access to data they need while denying access to data they don’t need to perform their job.
How is data protected in transit between the vendor and the client as well as between the vendor and the end-user? How is data protected at rest on servers and backup media? Encryption of data in both in-transit and at-rest stages is extremely important to keeping it safe from unauthorized access.
How is retired media (hard drives, flash drives, CDs, documents, etc.) sanitized? Physical and electronic data should be disposed of in a secure manner when no longer needed to keep information from falling into the wrong hands. This has become more difficult with the adoption of public cloud services as data may move across multiple physical systems and reside on shared resources.
Are employees and contractors required to attend security training? Providing security awareness education to users of all systems is an important step in limiting user errors that could harm your IT infrastructure and information.
What due diligence is performed on contractors and vendors prior to and post contract? Completing due diligence over your vendor’s third party (your fourth party) is important especially if they have access to your data. You want to make sure they have a secure environment to help keep your information secure.
Do they have a good cyber score? It is prudent to ascertain exposure of an organization at the surface web, deep web and dark web to predict the likelihood of a potential breach due to their exposure. There are several organizations that provide cyber scoring for vendors and also allow you to benchmark them against similar vendors.
Is there a formal incident management program in place? Proper incident handling procedures allow situations to be analyzed and prioritized so that the next appropriate course of action can be taken to address the problem. Breach notification, a key component of incident management, is now included within multiple regulations with emphasis on vendor reporting.
Does your vendor describe technical prevention measures in place? Utilizing various security tools such as firewalls, anti-virus products and intrusion detection and prevention systems allow you to help secure your network from adversaries.
Strategic risk is created from failed business decisions, or the inability to implement strategies consistent with the organizational goals. Third-party vendors that are not aligned with your company’s practices may threaten operations or your ability to effectively execute business strategies. It may take some time to fully build and/or review a comprehensive cybersecurity questionnaire, but it could save you a lot of time and risk exposure in the future. It’s an invaluable questionnaire that provides a lot of insight.
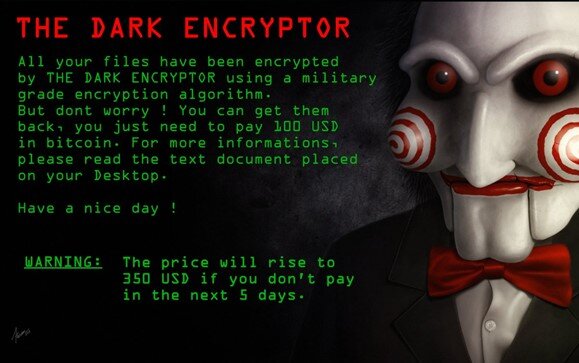
Facilitation of Ransomware Payment Sanction Risk
US Treasury Department Issues Ransomware Advisory
The ransomware advisories provides guidances and tools to recognize, resist, and report attacks.
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) is issuing this advisory to highlight the sanctions risks associated with ransomware payments related tomalicious cyber-enabled activities. Demand for ransomware payments has increased during the COVID-19 pandemic as cyber actors target online systems that U.S. persons rely on to continue conducting business. Companies that facilitate ransomware payments to cyber actors on behalf of victims, including financial institutions, cyber insurance firms, and companies involved in digital forensics and incident response, not only encourage future ransomware payment demands but also may risk violating OFAC regulations. This advisory describes these sanctions risks and provides information for contacting relevant U.S. government agencies, including OFAC, if there is a reason to believe the cyber actor demanding ransomware payment may be sanctioned or otherwise have a sanctions nexus.
Facilitating ransomware is harmful long term
Not only do ransomware payments fuel future attacks, OFAC explained it also threatens US national security interests given their profit and later ability to advance their cause. Paying ransom to a sanctioned entity or jurisdiction could fund activities in conflict with national interests.
What is Ransomware? Ransomware is a form of malicious software (“malware”) designed to block access to a computer system or data, often by encrypting data or programs on information technology systems to extort ransom payments from victims in exchange for decrypting the information and restoring victims’ access to their systems or data. In some cases, in addition to the attack, cyber actors threaten to publicly disclose victims’ sensitive files. The cyber actors then demand a ransomware payment, usually through digital currency, in exchange for a key to decrypt the files and restore victims’ access to systems or data.
Ransomware Payments with a Sanctions Nexus Threaten U.S. National Security Interests
Facilitating a ransomware payment that is demanded as a result of malicious cyber activities may enable criminals and adversaries with a sanctions nexus to profit and advance their illicit aims. For example, ransomware payments made to sanctioned persons or to comprehensively sanctioned jurisdictions could be used to fund activities adverse to the national security and foreign policy objectives of the United States. Ransomware payments may also embolden cyber actors to engage in future attacks. In addition, paying a ransom to cyber actors does not guarantee that the victim will regain access to its stolen data.
Facilitating Ransomware Payments on Behalf of a Victim May Violate OFAC Regulations
Under the authority of the International Emergency Economic Powers Act (IEEPA) or the Trading with the Enemy Act (TWEA),9 U.S. persons are generally prohibited from engaging in transactions, directly or indirectly, with individuals or entities (“persons”) on OFAC’s Specially Designated Nationals and Blocked Persons List (SDN List), other blocked persons, and those covered by comprehensive country or region embargoes (e.g., Cuba, the Crimea region of Ukraine, Iran, North Korea, and Syria). Additionally, any transaction that causes a violation under IEEPA, including transactions by a non-U.S. person which causes a U.S. person to violate any IEEPA-based sanctions, is also prohibited. U.S. persons, wherever located, are also generally prohibited from facilitating actions of non-U.S. persons, which could not be directly performed by U.S. persons due to U.S. sanctions regulations. OFAC may impose civil penalties for sanctions violations based on strict liability, meaning that a person subject to U.S. jurisdiction may be held civilly liable even if it did not know or have reason to know it was engaging in a transaction with a person that is prohibited under sanctions laws and regulations administered by OFAC.
Victims of Ransomware Attacks Should Contact Relevant Government Agencies OFAC encourages victims and those involved with addressing ransomware attacks to contact OFAC immediately if they believe a request for a ransomware payment may involve a sanctions nexus. Victims should also contact the U.S. Department of the Treasury’s Office of Cybersecurity and Critical Infrastructure Protection if an attack involves a U.S. financial institution or may cause significant disruption to a firm’s ability to perform critical financial services.
U.S. Department of the Treasury’s Office of Foreign Assets Control
- Sanctions Compliance and Evaluation Division: ofac_feedback@treasury.gov;
- (202) 622-2490 / (800) 540-6322
- Licensing Division: https://licensing.ofac.treas.gov/; (202) 622-2480
U.S. Department of the Treasury’s Office of Cybersecurity and Critical Infrastructure
- Protection (OCCIP)
- OCCIP-Coord@treasury.gov; (202) 622-3000
- Financial Crimes Enforcement Network (FinCEN)FinCEN Regulatory Support Section: frc@fincen.gov 12 See FinCEN Guidance, FIN-2020-A00X, “Advisory on Ransomware and the Use of the Financial System to Facilitate Ransom Payments,” October 1, 2020, for applicable anti-money laundering obligations related to financial institutions in the ransomware context.
Contact Information for Other Relevant U.S. Government Agencies:
Federal Bureau of Investigation Cyber Task Force
U.S. Secret Service Cyber Fraud Task Force
Cybersecurity and Infrastructure Security Agency
Homeland Security Investigations Field Office
Using Linux Won't Save You from Ransomware - Here's Why
"Ransomware attacks are becoming more targeted, sophisticated, and costly, even as the overall frequency of attacks remains consistent." (FBI, 2019)
Since early 2018, there has been a sharp spike in the cleverness, thoroughness, and precision of the security breaches we see in the ransomware landscape. Regardless of attack vector - whether it's from phishing, vishing, or the classic insider threat - once ransomware is on your computer, it's incredibly difficult to restore your files. It takes some serious intervention to stand a chance of recovering your business (or personal) data.
The easiest solution is to get the appropriate key and decryption tool, and use them together to unlock your files...but typically you only receive those resources in exchange for paying the ransom, and many companies can’t afford the ransom at its original price. By that time, there's a good chance you've taken a catastrophic financial blow. From hospitals, to insurance companies, to banks, there are plenty of highly valuable (and highly vulnerable) assets to be manipulated, and threat actors don’t hesitate to put lives at stake for the benefit of their wallets.
So how can we prevent these breaches? What is the key to staying safe from attackers?
The answer may be simpler than you think.
The three most impactful measures you can take to stay safe are as follows:
★ Quarantine
○ Take your computer off the network or wifi and reset your data by wiping the device entirely back to its factory settings (the way it came when you bought it) the moment you can confirm there has been a breach.
★ Have a backup
○ You can only take the first measure if you either don’t care at all about your data, or you have bothered to back it up so you have an unencrpted copy.
★ Get help negotiating your ransom down
○ If you need to pay the threat actor the ransom money to recover your data, there are many firms that can help you with this - don’t pay the full price of the ransom! Firms that can help with ransom negotiation and essential protections include CyberSecOp, which you can reach by using Our Contact Form.
So what’s so special about the threat of Linux-based malware? A Linux-based ransomware variant has the potential to take down any and every industry. Major cloud providers like AWS (Amazon Web Services), Oracle, and Microsoft base entire workloads on Linux; malware sweeping through those servers could bring down any company that uses a modernized cloud stack to host their sites and data.
And then there are hacktivists - hackers who hack to do activism for their cause (which can vary greatly in scope between organizations). Hacktivists have a history of using their ransomware attacks to make a point - whether it’s political or personal - and to incite fear in other companies or individuals who support the cause represented by the victim. While you might not think this presents a threat to you personally, or even to your business, the truth is that innovations in cyberattacks threaten us all. If the target were to have a Linux-based system, the hacktivist group targeting that individual would be devoted to finding a way to spread ransomware across Linux-based devices. When ransomware is evolved by perpetrators to this degree, we are likely to see major outages across all the cloud providers listed above, and it could cripple any business or personal account that is hosted therein.
To avoid such a catastrophic and monolithic problem, we should learn to govern our systems from a more ecosystem-centric approach, rather than depend on the classic signature-based antivirus alerts that have become standard. You may recognize Norton Antivirus alerts or even operating-system-based protection like Windows Defender presenting to you pop-ups about updating your signatures.
The truth is that we shouldn’t rely on the technical drivers of these updates, the people who hunt down and publish these known virus signatures, to keep us safe. We should be educating our employees, friends, and families, on the essentials of how to stay digitally secured and prevent breaches in the modern threat landscape. This concept is especially important as a mere tweak in the code of a virus and a quick recompilation of that code can cause the hash (or signature) of the virus to change, causing these famous signature-based antivirus softwares to completely miss the threat on your device.
A phenomenal example of how dangerous this variant-based workaround can be is what happened to the Colorado State Department of Transportation (CDOT) in early 2018.
“As CDOT’s Information Security group scrambled to contain the spread and impact of SamSam’s first wave, their efforts were quickly undermined by another variant of the same ransomware strain that was spreading throughout many of the newly sanitized zones of their network.”[1] (Richard Horne for the SANS Institute)
In an interview with the Denver Post, Brandi Simmons, a spokeswoman for the state's Office of Information Technology said, “The variant of SamSam ransomware just keeps changing. The tools we have in place didn't work. It's ahead of our tools.” The tools in question were signature-tracking antivirus software, like what many of us use on our home computers. In the end, Colorado's Office of Information Technology, the Colorado National Guard, and the FBI all had to collaborate to contain this threat, and by the time they had, over 2,000 computers running Windows and McAfee security software had been taken offline.
In conclusion, it seems inevitable that we will see Linux systems fall prey to the same types of ransomware we currently battle; it’s only a matter of time. Make sure you’re safe and you know how to protect your data: maintain a backup of all your files, be ready to quarantine in the event of a breach, and remember not to panic. We are here to help.
Sources:
https://www.sans.org/reading-room/whitepapers/tools/strings-me-linux-ransomware-39870
https://www.darkreading.com/attacks-breaches/second-ransomware-round-hits-colorado-dot/d/d-id/1331197
Authored by Alison Stuart
What is Cyber Security, IT Security, and Data Security?
What is the need for IT security and CyberSecurity?
Computer security, cybersecurity or information technology security (IT security) is the protection of computer systems and networks from the theft of or damage to their hardware, software, or electronic data, as well as from the disruption or misdirection of the services they provide.
IT security is a set of cybersecurity strategies that prevents unauthorized access to organizational assets such as computers, networks, and data. It maintains the integrity and confidentiality of sensitive information, blocking the access of sophisticated hackers.
What is Data Security?
Data security means protecting digital data, such as those in a database, from destructive tampering and unauthorized access. Hardware based security or assisted computer security offers an alternative to software-only computer security.
Common examples of:
- Data encryption
- Tokenization
- Key management
- Data loss prevention
- Data classification
- Data accees management
What is the need for network security?
Network security is the practice of securing a computer network from intruders, whether targeted attackers or opportunistic malware. Application security focuses on keeping software and devices free of threats. A compromised application could provide access to the data its designed to protect.
What is Internet security
Internet security involves the protection of information that is sent and received in browsers, as well as network security involving web-based applications. These protections are designed to monitor incoming internet traffic for malware as well as unwanted traffic. This protection may come in the form of firewalls, antimalware, and antispyware.
What is Critical infrastructure security:
Critical infrastructure security consists of the cyber-physical systems that modern societies rely on.
Common examples of critical infrastructure:
- Electricity grid
- Water purification
- Traffic lights
- Shopping centers
- Hospitals
What is Application security:
You should choose application security as one of the several must-have security measures adopted to protect your systems. Application security uses software and hardware methods to tackle external threats that can arise in the development stage of an application.
Applications are much more accessible over networks, causing the adoption of security measures during the development phase to be an imperative phase of the project.
Types of application security:
- Software development
- Application testing
- Code review
- Vunerablity and penetration testing
What is Network security:
Network security ensures that internal networks are secure by protecting the infrastructure and inhibiting access to it.
Common examples of network security implementation:
- Extra logins
- New passwords
- Application security
- Antivirus programs
- Antispyware software
- Encryption
- Firewalls
- Monitored internet access
Types of cyber threats:
The threats countered by cyber-security are three-fold:
Cybercrime includes single actors or groups targeting systems for financial gain or to cause disruption.
Cyber-attack often involves politically motivated information gathering.
Cyberterrorism is intended to undermine electronic systems to cause panic or fear.
So, how do malicious actors gain control of computer systems? Here are some common methods used to threaten cyber-security:
Malware
Malware means malicious software. One of the most common cyber threats, malware is software that a cybercriminal or hacker has created to disrupt or damage a legitimate user’s computer. Often spread via an unsolicited email attachment or legitimate-looking download, malware may be used by cybercriminals to make money or in politically motivated cyber-attacks.
There are a number of different types of malware, including:
Virus: A self-replicating program that attaches itself to clean file and spreads throughout a computer system, infecting files with malicious code.
Trojans: A type of malware that is disguised as legitimate software. Cybercriminals trick users into uploading Trojans onto their computer where they cause damage or collect data.
Spyware: A program that secretly records what a user does, so that cybercriminals can make use of this information. For example, spyware could capture credit card details.
Ransomware: Malware which locks down a user’s files and data, with the threat of erasing it unless a ransom is paid.
Adware: Advertising software which can be used to spread malware.
Botnets:Networks of malware infected computers which cybercriminals use to perform tasks online without the user’s permission.
SQL injection
An SQL (structured language query) injection is a type of cyber-attack used to take control of and steal data from a database. Cybercriminals exploit vulnerabilities in data-driven applications to insert malicious code into a databased via a malicious SQL statement. This gives them access to the sensitive information contained in the database.
Phishing
Phishing is when cybercriminals target victims with emails that appear to be from a legitimate company asking for sensitive information. Phishing attacks are often used to dupe people into handing over credit card data and other personal information.
Man-in-the-middle attack
A man-in-the-middle attack is a type of cyber threat where a cybercriminal intercepts communication between two individuals in order to steal data. For example, on an unsecure WiFi network, an attacker could intercept data being passed from the victim’s device and the network.
Denial-of-service attack
A denial-of-service attack is where cybercriminals prevent a computer system from fulfilling legitimate requests by overwhelming the networks and servers with traffic. This renders the system unusable, preventing an organization from carrying out vital functions.
8 Cyber Security Best Practices for Business
- Conduct Phishing Simulations
- Implement Risk Management Governance Approach
- Secure Remotely Working and Travelling Employees
- Plan for mobile devices
- Create a Cybersecurity Awareness Training Program
- Monitor User and File Activity
- Enforce password best practices
- Enforce the Use of Password Managers, SSOs, and MFAs
- Audit Privileged Access
- Implement Data Loss Prevention
- Update Software and Systems
- Implement and monitor EDR, MDR, and SIEM
- Regularly back up all data, and offsite backup
CyberSecOp cybersecurity solution provide pace of mind when it comes to privacy and security. Ensuring data security in the cloud or onpfremisies , compliant and protected by best-in-class security: your data, and the tools you use to harness it, can truly empower your business.
Vishing Awareness
Vishing
Spoofing a legitimate phone number, voice phishing scammers lead people to believe the call is legitimate
What is Vishing?
We’ve all heard the countless stories on phishing and how much of a threat is it in today’s information security landscape. Social engineering to solicit confidential information via email is a threat that all of us have been made aware of. Extensive efforts have been made to not only reduce the influx of phishing emails, but also to raise awareness so that users have the know-how to assess and respond to the threat when a malicious email hits their inbox.
In response, threat actors have turned to a newer form of exploitation: Vishing. Vishing is a form of criminal phone fraud that uses social engineering over the phone or SMS to gain confidential information. Here are some examples
Fake call from “Help Desk” asking for credentials
Unsolicited calls for credit and loans
Calls from a fake client asking about an invoice
Vishing is becoming an increasingly favored tool attackers use, due to the Covid-19 pandemic. With the shift to work-from-home environments, corporate VPNS, and elimination of in-person verification, threat actors are shifting their tactics to exploit this widespread weakness.
How do I protect my firm against Vishing?
Security awareness is the best line of defense against this type of attack, so be sure to incorporate vishing education into your information security awareness program. Policies and procedures should be established and communicated to ensure that employees can verify identity when the helpdesk or anyone else from the company calls and asks after proprietary topical information. It is imperative that information security managers instill a sense of suspicion for any caller asking for said information.
Enabling MFA for any system that has access to confidential information, network or system is non-negotiable; that second factor of authentication can halt many types of attacks. When you enable MFA you avoid the use of SMS as a means of authentication as SMS is easily manipulated and exploited.
Lastly, always apply least privilege so that in the event an account is compromised, there will be minimal damage.
AUTHOR: CARLOS NETO
Information Security Officer
Pandemic & Post Pandemic Cyber Security Remote Workforce
The current pandemic gives cloud computing a push forward; our clients are taking advantage of CyberSecOp Alliance resilient cloud-based digital infrastructure for businesses of every size to protect their data. We have noticed 58% growth in our Cloud services, securing and protecting data while working remotely is one of the top concerns for most of our clients.
During the crisis, cyberattacks have increased worldwide, including against critical healthcare institutions, which have been the target of ransomware attacks. Private-sector data reveals a 350% surge in phishing websites since the start of the pandemic.
Our security professionals prepare for a new level of untrusted network activity and cyber attacks as remote working is expected to continue. What are the questions you should be asking, and what controls need to be in place?
Pandemic & Post Pandemic Cyber Security
While we are still very much on this transformation journey, we are working on the mindset of our clients to be prepared for quicker response to a crisis like COVID-19, by doing this we will increase business continuity and build-in security for all remote working processes. Removing legacy systems, introducing more automation, better identity and access management for remote systems, secure build for remote devices, extended security services such as Managed Detection and Response (MDR), IPS/IDS, Advanced Endpoint Protection, Application Firewall, DNS Filtering, Automated Virus Containment, and Filer Reputation Detection this will provide an additional layers of security for remote workforce, please see below for other recommendations.
Telecommuting is the only way of working for many
1. Adoption of virtual desktop will finally see an upswing:
With tele-working likely to become the norm, virtual desktops could become the security baseline for IT teams to enforce data management standards. Virtual desktops emulate a computer system so that IT can control access as such adding input/output devices as well as software and applications. This could become an important control point when remote workers are operating outside the safety of a corporate network.
To meet the stringent criteria of regulatory and corporate compliance regarding data security, many companies will see the adoption of virtual desktops as the go-to solution.
2. We will notice surge in adoption of decentralized cyber security:
Traditional cyber security controls dictate a centralized approach where data is consolidated from different sources to perform analysis and investigation. With swift digitization, security controls will shift to data sources, similar to the trend witnessed in IoT. We could start seeing a new wave of anti-virus, data loss protection, digital rights management and endpoint-based firewalls and other security controls gaining traction.
With millions of employees working from home, hackers’ focus has shifted from enterprise to remote working individuals. To handle the menace that exists in cyberspace, decentralized cyber security will rise where greater emphasis will be placed on data sources such as actual remote employees themselves.
3. Rise in bio metric way of authentication:
User access controls have largely revolved around one or two-factor authentication. These methods rely on “something you know (username)” and “something you have (password)” and given hackers’ interest in employees as the weak link to start a technical exploit, we will see cyber attacks directed towards individuals.
This means identity protection will be of priority and the best defense should focus on building authentication systems which focus on “who you are.” This would require advanced bio metric solutions such as fingerprint/thumbprint/hand print, retina, iris, voice, and facial recognition technologies.
With bio metrics, hackers’ attempt at impersonating you just got a lot harder than trying to break into passwords.
New processes will govern our way of work
1. Global privacy regulation and policies will require a re-look:
The current state of privacy regulations is designed around the enterprise network and building the proverbial wall to keep sensitive data out of prying eyes. With remote working concepts taking center stage, re-evaluation of these policies is needed to address the new cyber threats.
From a risk management perspective, global privacy policies will need to encapsulate standard operating procedures regarding BYOD, GDPR, NYDFS, CCPA, SHIELD Act compliance and state privacy laws.
Governance around companies and employees’ social media profiles would also have to be included as these platforms are frequently trolled by hackers as they carry out reconnaissance before launching a cyber attack.
2. Cloud will become more important than ever before:
The shift to cloud services offers employees, customers, suppliers, and everyone else across the ecosystem a seamless and frictionless access to data and applications. Remote access by various users would compound security challenges and presents many new potential attack vectors.
In the post-pandemic world, IT resources would shift towards data, particularly keeping data secure across cloud platforms.
3. Containerization technology will be extended beyond enterprise network to include endpoints:
IT architectures will extend containerization and zoning concepts to include not just systems, but also people, roles, and the level of sensitive data they possess. Containerization, thus, will be extended beyond enterprise networks to include endpoints such as remote worker machines and mobile devices.
This will facilitate cyber security teams to apply varied access controls and demarcate data storage to minimize risk of cyber intrusion and data breach.
Source: Cybersecurity Ventures
What is Cybersecurity Maturity Model Certification (CMMC)
The Cybersecurity Maturity Model Certification (CMMC) is a unified standard intended for implementing cybersecurity across DoD contractors.
The CMMC has been in development for a number of years, but the first details on the framework were released in January 2020. The framework makes use of a “maturity” model, in which audits will be conducted by third-party assessors. Firms will be assigned a “level” that represents the cybersecurity protections, or maturity level they have demonstrated.
Breach Report and predicted loss by 2024
A recent study predicted that business losses due to cybercrime will exceed $4.5 trillion by 2024. The threat to the Defense Industrial Base (DIB)--the network of more than 300,000 businesses, organizations, and universities that research, engineer, develop, acquire, design, produce, deliver, sustain, and operate military weapons systems--is especially alarming due to current cyber warfare activities by cybercriminals and state-sponsored actors.
Security is a foundational component of acquisition
The Office of the Under Secretary of Defense for Acquisition and Sustainment (OUSD(A&S) recognizes that security is a foundational component of acquisition and that some contractors are trading security to benefit cost, schedule, and performance. It's estimated that the DoD supply chain consists of more than 300,000 businesses and organizations, all of which are targets. Most of these organizations are small to mid-size businesses, which are the most vulnerable to cyber-attacks. Based on over 100 Data Breach Investigation's CyberSecOp recognized that organizations between 100 -300 employees are prime victims for cyber criminals because of lack of security controls.
CMMC Model Structure
The goal of CMMC is to provide a framework for the improvement of cybersecurity in DIB sector organizations. CMMC currently defines 17 domains of technical capability, each with five levels of certification (L1 through L5) and specific practices. The DoD will require an organization to have CMMC Level 3 certification before it can receive Controlled Unclassified Information (CUI) in any domain.
CMMC Domains
CMMC Leveled Practices
The majority of the practices (110 of 171) originate from the safeguarding requirements and security requirements specified in FAR Clause 52.204-21 and DFARS Clause 252.204-7012. The practices fall into five levels:
Level 1 represents basic cyber hygiene, and focuses on the protection of federal contract information (FCI). It consists of practices that correspond only to the basic safeguarding requirements specified in 48 CFR 52.204-21 ("Basic Safeguarding of Covered Contractor Information Systems").
Level 2 is a transitional step in cybersecurity maturity progression to protect CUI. Level 2 consists of a subset of the security requirements specified in NIST SP 800-171, as well as practices from other standards and references.
Level 3 focuses on the protection of CUI. It encompasses all of the security requirements specified in NIST SP 800‑171, as well as additional practices from other standards and references.
At Level 4, the model begins to focus more on the proactive activities an organization can take to protect, detect, and respond to threats. These practices enhance the organization's ability to address and adapt to the changing tactics, techniques, and procedures (TTPs) used by advanced persistent threats (APT)s.
Level 5 focuses on the protection of CUI from APTs. The practices increase the depth and sophistication of cybersecurity capabilities.
CMMC Cyber Compliance Services
DOD has made the effort to simplify CMMC, but it is surely still complicated. CMMC is based on several other standards, including DFARS, CERT RMM, 800-171, AU ACSC Essential Eight, UK NCSC Cyber Essentials, ISO 27001, CIS Critical Security Controls, and the NIST Cyber Security Framework. Utilizing all the above information security standards make it very challenging for most DOD contractors to copy with CMMC. Get compliant with CyberSecOp CMMC Assessment, Security Program & Advisory Services.
Author: Kaushik Reddy
New Remote Attack on Workforce Asks For Consent
A newer type of attack that is gaining momentum on the WFH revolution is Consent Phishing, which seeks the user’s permission as opposed to password.
With today’s widespread use of cloud applications like Webex, Zoom, and Box for increased productivity, the average person has no doubt ran across an application that asks for consent. Attackers have leveraged this familiarity to create malicious applications that request permission for access to sensitive data. Once the user has granted the application access it’s Game Over.
How it works
While each attack method varies, it usually comes down to the following steps:
Threat actor registers a malicious app with an OAuth 2.0 provider, such as Azure Active Directory, AWS, or Google Cloud
The app is configured in an inconspicuous way that makes it seem legitimate
The threat actor gets a link to pop up for the user which may be done through conventional email-based phishing, by compromising a non-malicious website
The victim clicks the link and is shown the familiar-looking consent prompt asking them to allow the application permission to sensitive data
Once the user clicks accept, they have granted the application permissions to access sensitive data
The malicious application receives an authorization code, which it then redeems for an access token, and potentially a refresh token
The access token is used to make API calls on behalf of the user
How to protect against this type of attack
Advanced endpoint protection
User awareness, if the application consent prompt contains misspelling or grammar errors, those are telltale signs that it may be malicious
Configure your organization to only allow applications that are published and verified
Configure policies to whitelist only certain apps for use
Author: Carlos Neto
Home Routers Major Weakness in Work from Home Revolution
‘Prepping’ for Work from Home
For the past few years employees and employers alike extolled the virtues of working from home (‘WFH’). We’ve heard the stories of how it leads to a happier and more productive employee, less overhead for the employer, and just more flexibility overall. Most people knew a shift would come eventually – kind of like the shift to IPV6- but it stalled and stalled. Then the pandemic happened and WFH had been thrust upon us with such force that businesses were, and still are, scrambling to get the pieces in place for an effective remote staff.
It is no longer a secret that WFH is here to stay. Many businesses including Fujitsu and Twitter have just gone ahead and implemented WFH ‘forever’. With this change come challenges. One of those is the security of routers in the millions upon millions of homes that now serve as working offices. According to a study by Germany’s Fraunhofer Institute for Communication, vendors have failed to fix hundreds of vulnerabilities in their consumer-grade routers, leaving hundreds of thousands of users exposed to a wide range of attacks. "Nearly all were found to have security flaws, some of them very severe," the Fraunhofer Institute said in a press release. "The problems range from missing security updates to easily decrypted, hard-coded passwords, and known vulnerabilities that should have been patched long ago."
Advice on next steps
So what should we do? The first step is to know the make and model of your router. Research it for any known vulnerabilities, as there may be some cases where the device is so insecure that even patching it still leaves it vulnerable. Once you’ve decided if it is worth keeping the device make sure that it automatically installed firmware updates. If not you may need to manually update it. A task that is well worth the effort. Another task is to make sure that the administrator password for the router has been changed from the default admin password. Many routers now have unique default passwords for their routers- but there are still plenty out there that don’t.
WFH Users should use complex passwords on their routers including:
· Uppercase and Lowercase
· Numbers and Symbols
· At least 8 characters long
You should also use the strongest Wi-Fi encryption your router supports. WPA3 (Wi-Fi Protected Access Version 3) is best.
You may have children working, playing, and streaming while you are home. Ensure they use their own devices and do not surf on your work devices.
Router configuration and device hardening are just one of the many layers of security that businesses need to adapt and expand to their remote workforce. We here at CyberSecOp would not be surprised if, sooner rather than later, companies begin purchasing, installing, and administering home routers to ensure a secure endpoint to endpoint networking. Until then remain vigilant and patch patch patch!
Author: Carlos Neto
Cybersecurity Risks in a Pandemic: What you need to know
The COVID-19 pandemic has alerted many organizations to gaps in their information security infrastructure heretofore unrealized. Most of these deficiencies have been revealed as a direct outcome of the shift from a workforce-in-place physical environment centered around a fixed and determinable worksite location to a distributed, unstructured environment where most employees and individuals are working remotely.
At CyberSecOp, we can help your organization address these, as well as other concerns related not only to the current operating environment but also pertaining to any and all operating challenges you may face as part of your ongoing operations.
The lack of a centralized workspace raises a multiplicity of information security concerns, including but not limited to the following:
1. Does the company have an established Work-From-Home (WFH) information security policy, and if not, how is remote worker security managed?
2. Are employees adequately trained to work remotely, and do they have the appropriate tools at their disposal to ensure the preservation of the security environment?
3. How does the organization manage mobile device and laptop security, including encryption?
4. Control and testing of the commercial VPN?
5. Does the organization maintain a comprehensive data loss protection policy?
6. How, if at all does the organization address data loss protection?
7. Does the organization have a breach response plan for mobile and remote WFH employees?
At CyberSecOp, we can help your organization address these, as well as other concerns related not only to the current operating environment but also pertaining to any and all operating challenges you may face as part of your ongoing operations. Our skilled team of information security professionals can provide a comprehensive assessment of your information security framework and suggest remediation and complementary additions to your existing framework, as the case may be.
There are several things to consider if and when the time comes for firms to return to the office. CyberSecOp recommends:
Third-Party network risk assessment
Operational Responses to Security Incidents
Work from Home Security
Virtual Meeting Applications
Updates and Patches
A full virus scan on workstations returning to the office
Full Windows/Mac updates
Review Wi-Fi connections on returning devices: Some people may come back and still connect to Optimum Wi-Fi (This can be very risky)
Delete any accounts not for company use
Provisioning devices employees may have bought in haste (Hardening AV adding to the domain)
Mobile device management strategy for new mobiles, or devices that employees are using more
Pandemic Policy, Cybersecurity Policy Wireless policy
It is important for organizations to foresee possible consequences transitioning from working remotely to returning to the office. CyberSecOp can help facilitate this transition.
AUTHOR: Michael Young
Achieve an Effective Security Awareness Program
For any company, especially technology-oriented ones, being aware about the cyberthreat landscape is critical. There is often the mindset that most cyberattacks can be warded off by procuring and implementing the latest security technologies, and relying on consultants and internal resources to police implementation.
While this passive strategy may yield a certain level of effectiveness, it also takes a high level of active, participatory security awareness on part of both employees and management in order to 100% fortify the lines of defense around the business or corporation.
STEPS TO ACHIEVE AN EFFECTIVE SECURITY AWARENESS PROGRAM
1. The Major Orienting Components – A comprehensive, participatory information security awareness program should have as its three foundational pillars the principles of confidentiality, integrity, and availability. While the first two terms speak for themselves, the third is often misapprehended. Here, it refers to the organization maintaining a comprehensive system of controls over information security such that employees can be assured of having access to all information necessary to perform their roles without risk of breach.
2. The Protection of Corporate Resources - “Corporate resources” does not just refer to digital assets — it also refers to physical assets, such as paper documents. A security awareness checklist should include the proper usage of document-shredding machines and how the shredded documents should be disposed of.
3. Protection of Corporate Facilities - Employees should be trained not only in how to look for suspicious behavior from the outside, but from the inside as well. This will ensure against unauthorized personnel gaining access to the premises for purposes of mounting internal attacks against the information infrastructure.
4. The Formal Security Awareness Training Program – The corporation should maintain a comprehensive security awareness training program and all employees, irrespective of position with the organization and/or function, should regularly participate.
5. Determining Levels of Responsibility and Segregation of Duties – All employees involved in the day to day management of security over the corporation’s digital and physical information assets should have their roles clearly defined and responsibilities enumerated and documented in a comprehensive ‘R & R’ policy.
CyberSecOp Security Awareness Courses specializes in helping employees understand the mechanisms of spam, phishing, spear-phishing, malware, and social engineering and are able to apply this knowledge in their day-to-day job. Our Security Awareness training solutions effect meaningful, sustainable changes in any workforce. With CyberSecOp Security Awareness Training, employees are not just aware of the dangers presented by an ever-changing threat landscape: they’re empowered to protect your organization from them.
AUTHOR: RICH FIORE
Comodo and CyberSecOp Announce Strategic Partnership
Comodo and CyberSecOp Announce Strategic Partnership
after Award-Winning MSSP Dropped Leading Competitor
Clifton, NJ – June 30, 2020 – Comodo and CyberSecOp today announced their strategic partnership. CyberSecOp, an award-winning, independent security consulting firm providing a range of information security consulting services, has partnered with Comodo to expand its security services offering for its customers. Comodo displaced a leading competitor.
“We focus on the customer experience—delivering what our customers want when they want it. That is our commitment and we take it seriously” said Jeffrey Walker, Chief Information Security Officer at CyberSecOp. “We needed to expand our security operations to fit the growing demand from our customers. Once we saw Comodo's complete SOC as a platform (SOCaaP) offering for MSSP partners and its ingenious auto containment technology, we knew they were the right partner for us. Occasionally, we have a partnership that our firm can't survive without, and we are confident that this is the relationship we are building with Comodo.”
CyberSecOp chose Comodo because it’s the world’s only complete, next-gen SOC-as-a platform offering — which includes people, process, and technology. The patent-pending auto containment technology is the world’s only active breach protection that renders ransomware, malware or cyber-attacks useless. In addition, the platform saves MSSP partners time and money, without zero capital outlay.
“Our partners and the channel are in our DNA. Comodo is a partner-centric company and our goal is to make sure our MSSP partners and their clients are secure and happy,” said Alan Knepfer, President and Chief Revenue Officer at Comodo. “We are proud that such a respected MSSP has selected us. Our partners expect the best from us, and this allows us both to take our high standards to the next level.”
About CyberSecOp
CyberSecOp cybersecurity consulting services was founded by two information security professionals, and a managed services IT firm. They recognized the need for cyber security consulting services for small and medium-sized companies, and that small and medium businesses need to be secured with an information cyber security program. We provide Managed Security Services, Cyber Security Consulting, Security Consulting VISO Services, and Security Staffing.
Mission: To redefine customer business equity with best-of-breed transformation, technology, and talent.
Vision: Empower our customers to focus on core business competence through innovative and competitive IT and secure business process outsourcing.
About Comodo Security Solutions, Inc.
Comodo delivers next generation cybersecurity solutions to protect businesses, schools, and government organizations in today’s risk-filled business environment. Headquartered in Clifton NJ, Comodo’s global development team and threat intelligence laboratories deliver innovative, category-leading, solutions for a company’s endpoints, network boundary, and internal network security.
Thousands of companies and organizations rely on Comodo’s technology to authenticate, validate, and secure their most precious asset—information—and to combat constant cyberattacks and threats like ransomware from wreaking havoc on a global scale.
www.comodo.com
sales@comodo.com
+1 888 551 1531
What Is Ransomware?
Ransomware is a type of malicious software that is designed to block access to a computer system or its data until a sum of money is paid. Ransomware attacks typically involve encrypting the victim's data and demanding a ransom from the victim to restore access to the data upon payment. Ransomware attacks can be extremely disruptive and costly for individuals and organizations, as they may result in the loss of important data and interruption of business operations.
There are several ways that ransomware can be delivered, including through email attachments, malicious websites, and vulnerable software. It is important to protect yourself and your organization from ransomware by regularly updating your software and operating systems, using strong passwords and two-factor authentication, and being cautious when opening emails or downloading attachments from unknown sources. If you do fall victim to a ransomware attack, it is important not to pay the ransom and to seek out professional help to restore your system and data.
Ransomware attacks can have significant impacts on businesses.
Ransomware attacks can have significant impacts on businesses, including financial losses, reputational damage, and disruption of operations. According to a 2021 report by the cybersecurity firm Emsisoft, the average ransom demand for a ransomware attack on a business in 2021 was $233,817, with the highest ransom demand being $50 million. The report also found that the number of ransomware attacks on businesses increased by 89% in 2021 compared to the previous year.
In addition to the direct financial costs of ransomware attacks, businesses may also incur indirect costs such as loss of productivity, damage to customer relationships, and legal fees. Ransomware attacks can also lead to reputational damage, as customers and stakeholders may lose trust in the affected business if their data is compromised or if the business is unable to provide its products or services due to the attack.
It is important for businesses to implement strong cybersecurity measures to protect themselves from ransomware attacks, as the costs of such attacks can be significant. This may include regularly updating software and operating systems, using strong passwords and two-factor authentication, and implementing backup and recovery systems to minimize the impact of a successful attack.
ransomware prevention technology
There are several technologies that can be used to prevent ransomware attacks and protect against the damage they can cause. Some of these technologies include:
Antivirus software: Antivirus software can identify and block ransomware before it is able to infect a system.
Firewalls: Firewalls can block incoming connections from known malicious sources, including those used to deliver ransomware.
Email filtering: Email filters can block or quarantine email messages that contain malicious attachments or links, which can prevent ransomware from being delivered through email.
Web filtering: Web filters can block access to malicious websites, which can prevent ransomware from being downloaded from these sites.
Network segmentation: Network segmentation can help to isolate different parts of a network from one another, which can limit the spread of ransomware within an organization.
Backup and recovery systems: Regularly backing up data and implementing recovery systems can help businesses to minimize the impact of a ransomware attack by allowing them to restore their systems and data from a known good state.
It is important to note that no single technology can provide complete protection against ransomware attacks. It is recommended to use a combination of technologies and to regularly update and maintain them to ensure the best possible protection against ransomware.
So, What Exactly Is the Dark Web, Anyway?
The first time I heard the term ‘Dark Web’ was in the context of a case of misappropriated identity. A close relative of mine had begun receiving all sorts of communications from credit card companies and debt collectors concerning delinquencies that they were completely unfamiliar with. One even included an attempt at collecting back premises rent for an apartment in Dallas, Texas where my relative had never visited in their life. After spending months fighting off financial claims and trying to repair their credit history, my relative contracted a computer security professional to perform a forensic investigation of their home PCs. It was ultimately discovered that some or all of the data breach enabling the identity theft had been the outcome of a fairly sophisticated spear-phishing attack combined with the installation of a key logger agent. The forensics also revealed that much of their Personal Identifying Information had migrated to the Dark Web and was presently freely available to whomever-or whichever entity-might be interested.
Dark Web and how it functions
Dark Web, I thought. Huh. I’ve heard of the Dark Web but don’t know much about what it is or more specifically, how it functioned. Heretofore I’d (wrongly) believed it was composed of a bunch of gamers sharing logins to cloud gaming services along with the ever-present and always thriving market for pornography. My investigatory efforts yielded that the Dark Web is so, so much more, however; and I thought it was important to share my findings to clear up any popular misconceptions of which there is legion. Therefore, I’ve decided to put together a brief post that provides the nuts and bolts of what’s become an increasingly important cog in the global economy for ill-gotten bits and pieces of data and information. It turns out, the Dark Web wasn’t nearly as elemental as I’d initially suspected.
The Dark Web is a collection of thousands of websites that use anonymity tools to hide their IP addresses. While it's most famously been used for black market drug sales and even child pornography, the Dark Web also enables anonymous whistleblowing and protects users from surveillance and censorship. Readers will recall that the Dark Web played an intermediary role in WikiLeaks dissemination of certain confidential U.S. Department of Defense documents related to the conflicts in Iraq and Afghanistan.
Who created the Dark Web and how can it be assessed?
The majority of Dark Web sites use the anonymity software Tor with was created by the U.S. Department of Defense, though a smaller number also uses a similar tool called I2P. Both of those systems encrypt web traffic in layers and bounce it through randomly-chosen computers around the world, each of which removes a single layer of encryption before passing the data on to its next hop in the network. In theory, that prevents any spy—even one who controls one of those computers in the encrypted chain—from matching the traffic’s origin with its destination. In layman’s terms-traffic on the Dark Web is untraceable.
Though the Dark Web is most commonly associated with the sale of drugs, weapons, counterfeit documents, and child pornography, not everything on the Dark Web is quite so “dark.” One of the first high profile Dark Web sites was the Tor hidden service WikiLeaks created to accept leaks from anonymous sources. Even Facebook has launched a Dark Web site aimed at better catering to users who visit the site using Tor to evade surveillance and censorship. The Dark Web is also a vehicle for hackers to buy and sell personal information such as names, addresses, social security numbers, credit card information, etc. The more information they obtain from the unsuspecting victim, the higher the price.
Can Dark Web provide privacy
Just how completely Dark Web users can evade the surveillance of highly-resourced law enforcement and intelligence agencies, however, remains an open question. The FBI and EUROPOL have both launched successful Dark Web investigations aimed at stopping human trafficking, identity theft, and drug smuggling, and in most cases, the agencies were able to identify the threat actor by setting up relays and scripts on websites they frequently visit. It's also possible that the agencies employed sophisticated DNS attacks on TOR servers or used other exploits; then again, it’s also possible they were able to rely on good old Human Intelligence-informants. Everyone seems to have a price.
So in summary, we know that the Dark Web exists, it’s a marketplace for all sorts of data and information exchange, not all of it legal or voluntarily disclosed. The best way to ensure you don’t wind up on the wrong side of information exchange? Secure your information systems, be very, very judicious in responding to emails and if you have any questions or concerns, contact a licensed information technology security professional. The stakes are high, and only getting higher.
Author: Rich Fiore
Moving to the cloud: Efficiency and Reduced Organizational Risk Posture
Moving to the cloud: A Study in Security, Efficiency & Reduced Organizational Risk Posture
A recent Gartner study indicates that cyber crimes are at an all-time high, up 30% year over year. This is and should be of tremendous concern to C-suite executives and boards of directors.
The root cause of cybercrimes varies; however, most organizations will experience vulnerabilities arising from technological gaps due to neglected software patching initiatives, outdated firmware, continued use of hardware beyond manufacturer ‘end of life’ standards, limited resources, limited budgets, multiple new compliances, and of course externalities such as the recent global pandemic.
In efforts to protect against threat actors while simultaneously acknowledging their companies’ limitations, more and more C-suite information security executives are proposing complete moves to cloud-based computing environments along with the ‘shared resource’ model characteristic thereof. This will help ensure information security integrity, reduce or eliminate the threat of bad actors wreaking havoc on the company’s information systems and will allow the organization to achieve its goals with some element of cost-efficiency. To ensure these systems are implemented in the most efficient manner possible, many concerns will turn to Managed Security Services Providers (MSSPs).
1. Lack of resources create an unintended risk appetite
Some specific security challenges organizations face in today’s operating environment, based on experience include: A lack of resources creates an unintended risk appetite leads to organizational dysfunction and job loss. Organizations need to provide their CISO with their own budget, independent of IT, and the CISO needs to report at the same level as the CIO with a direct line to the Board of Directors and should feel comfortable addressing any vulnerabilities that may arise, notwithstanding resource requirements to address them. Recently, we were tasked with performing a security assessment and reporting our results directly to the client’s Chief Information Officer. The Chief Information Officer, in turn, requested that we provide our findings simultaneously, at a joint meeting of the Board of Directors. The Chief Information Security Officer had previously briefed the board on the organization’s information security posture and had suggested that risk levels were at a minimum and that there were no vulnerabilities or deficiencies that could pose mission-critical faults; in this, the CISO had sought to ‘paper over’ problems that had not been budgeted for and instead treated with an ‘it’s your job, you fix it’ mentality, creating a lose-lose proposition. Our findings and report directly contravened what the Board had previously been told, and this led to the firm initiating a comprehensive systems audit which resulted in the dismissal of multiple information technology executives.
2. Cloud Security Competency, Efficiency, and Cost-Effectiveness. As the cloud computing environment becomes mainstream, organizations will realize the competitive benefit of having so many competitors offering similar services. This allows organizations to seek out the best technology and team while adhering to internal resource limits.
3. Application and Network Monitoring
This service is critical for identifying potential risks and attacks from internal and external threats and one of the single largest information security infrastructure areas of investment for companies today. CyberSecOp has seen a volumetric increase in requests for our Security Information and Event Management (SIEM), Managed Detection and Response (MDR), Data Loss Prevention (DLP), Security Operations Center (SOC) and Cloud Access Security Brokers (CASB) services over the last year, which dovetails with broader global market trends. With ransomware and data security breaches at an all-time high, organizations are looking to managed IT security and managed compliance services providers to bridge the resource gap.
4. Data Security Governance Framework
Organizations are utilizing the cloud to aid with compliance, reducing the upfront cost of buying all the necessary security solutions and related resources needed to get them configured and managed; indeed, the focus has switched to using cloud and shared resources provided by managed IT and managed security providers.
5. Enterprise Security Partners
Bringing on an Enterprise Partner enables companies to focus on those factors that promote business growth as opposed to focusing on back-end solutions and internal control structures. In turn, the Enterprise Partner (MSSP) is often able to provide its services at a substantially more cost-efficient and competency structure than if the company had attempted to replicate those services internally; examples of specific areas of favorability are hiring and staffing the function, keeping up with and implementing vulnerability management, leaner staffing levels, and overall cost efficiencies.
6. Authentication
Over the past year, we have seen a 70% increase in the adoption of multifactor authentication technologies, including but not limited to ‘password-lite’ cloud-based solutions capable of biometric authentication, geolocation fence authentication, anomaly detection, end-user based risk scoring, and evaluation. Partnering with an Enterprise Security Partner can ensure such technologies are rolled out across all organization information technology platforms in a coordinated and effective manner, with a minimum risk of non-adoption and systemic conflicts.
CyberSecOp provides proven Risk Management and Digital Transformation: As one of the most called on firms for security breach response services per Google Analytics, we have assisted with over 550 incident responses spanning 2019 and 2020. CyberSecOp helps organizations assess their cloud or on-premise environments and implement a security program that provides the safeguards needed in the cloud or on-premises. We also offer incident response and forensics teams to assist with containment, remediation, recovery from ransomware attacks, and other security breaches.
FBI, DHS CISA Publish Top Ten Cybersecurity ‘Hit List’
FBI, DHS CISA Publish Top Ten Cybersecurity ‘Hit List’ for State-Based and Non-State Based threat actors
Recently, two prominent US cybersecurity agencies disclosed, according to their internal metrics, the 10 most commonly exploited software vulnerabilities. The relevant time interval was 2016 through 2019, inclusive, as well as separate guidance listed for 2020.
The report, authored by the Department of Homeland Security Cybersecurity and Infrastructure Security Agency (DHS CISA) and the Federal Bureau of Investigation (FBI), urges organizations in the public and private sector to apply all software patches and updates in order to prevent the most common forms of attacks encountered today.
This includes, but is not limited to, attacks carried out by state-sponsored, non-state, and unattributed threat actors.
US government officials have argued that applying patches could degrade the cyber arsenal of foreign actors targeting US entities, as they'd have to invest resources into developing new exploits, rather than relying on old and tested bugs.
"Exploitation of these vulnerabilities often requires fewer resources as compared with zero-day exploits for which no patches are available," US officials said.
"A concerted campaign to patch these vulnerabilities would introduce friction into foreign adversaries' operational tradecraft and force them to develop or acquire exploits that are costly and less widely effective."
A summary of the FBI and CISA’s ‘Top 10 Vulnerabilities from 2016 through 2019’
OLE - According to U.S. Government technical analysis, malicious cyber actors most often exploited vulnerabilities in Microsoft’s Object Linking and Embedding (OLE) technology. OLE allows documents to contain embedded content from other applications such as spreadsheets. Of the top 10, the three vulnerabilities used most frequently across state-sponsored cyber actors from China, Iran, North Korea, and Russia are related to Microsoft’s OLE technology.
Apache Struts - After OLE the second-most-reported vulnerable technology was a widespread Web framework known as Apache Struts.
Windows Common Controls - As of December 2019, Chinese state cyber actors were frequently exploiting the same Windows OS vulnerability, an exploit in the Windows Common Controls that could allow for remote code execution.
Unpatched Devices - Deploying patches often requires IT security professionals to balance the need to mitigate vulnerabilities with the need for keeping systems running and ensuring installed patches are compatible with other software. This can require a significant investment of effort, particularly when mitigating multiple flaws at the same time. The FBI and CISA noted that this is a vulnerability as many organizations focus on their IT infrastructure as an area for cost-saving measure.
Microsoft and Adobe Flash products - A U.S. industry study released in early 2019 similarly discovered that the flaws malicious cyber actors exploited the most consistently were in Microsoft and Adobe Flash products, probably because of the widespread use of these technologies.
A summary of the FBI and CISA’s top vulnerabilities from 2020
Bugs detected in Citrix VPN appliances, specifically the Citrix Application Delivery Controller (ADC) and Gateway 10.5, 11.1, 12.0, 12.1, and 13.0; allows for directory traversal.
Bugs detected in Pulse Secure VPN servers; specifically, In Pulse Secure Pulse Connect Secure (PCS) 8.2 before 8.2R12.1, 8.3 before 8.3R7.1, and 9.0 before 9.0R3.4, an unauthenticated remote attacker can send a specially crafted URL to perform an arbitrary file reading.
COVID-19 Prompts Increased Ransomware Attacks Against SMBs Healthcare Providers
With the inception of the COVID-19 pandemic, malicious actors are increasingly targeting small hospitals and health centers with ransomware attacks. This is likely because these organizations are more likely to pay the ransom to recover data, as they weigh the perceived cost/benefit to strengthening their IT infrastructure security, or moving part or all of their IT operations to cloud-based solutions.
Cybercriminals tend to specifically target direct patient care facilities such as hospitals, healthcare centers, medical practices and health and wellness centers; although their efforts are certainly not confined to the above-referenced provider classes. The average ransomware demand is in the neighborhood of $60,000; however, simply paying the ransom in no way guarantees that the attacker will remit the decryption key; in fact, quite the opposite may occur; paying a ransom may encourage the attacker to maintain the leverage they enjoy over the target.
The ultimate consequences of ransomware attacks can and often are quite severe, ranging from continued involuntary exploitation of the attacker/victim relationship, to business closure. In some cases, class action lawsuits (dependent on the attack vector and information yield).
As more organizations move employees to work from home, remote staff make it increasingly difficult for IT teams to police computer systems and prevent cyber-attacks. Attackers now have far more access points and endpoints to probe or exploit, with little to no security oversight.
Here at CyberSecOp, we have formulated several countermeasures that healthcare employers should employ to minimize the risk of their networks being penetrated and secure their sensitive information.
Add data storage: After backing up data, the next step is to store data offline, on a different network, or a cloud-based environment.
Maintain a strong information encryption policy: Healthcare data must be encrypted at rest and transit with the highest standards available so that even if cybercriminals acquired it, they would not be able to read it.
Formulate and maintain an Incident Response Plan: Develop and test an incident response plan to help mitigate the impact of certain destructive malware attacks.
Track all data: Security personnel should closely monitor the company’s digital assets within the organization. This is of particular importance now as healthcare facilities’ attack surface expands and becomes more complex with some staff working remotely.
Establish and maintain firewalls: To harden networks and connected equipment, healthcare facilities with devices running open services should place them behind the latest application firewalls. They should also implement proper change management and firewall reviews to ensure proper documentation and optimization of these devices.
Follow the trends: Be aware of current ransomware threats, attack trends, and make sure those trends are socialized and communicated throughout the organization. Awareness is key.
Remote Working And Online Safety Tips
1. Avoid Creating Easy or Common Passwords
Password123 is a big no-no. Hackers have become bolder and have been using password deciphering tools to infiltrate vulnerable accounts. Multi-factor authentication (discussed later in this list) will most likely prevent them from going further, but it is always recommended to create a password with a mix of symbols, numbers, capital letters, and a lengthy number of characters to make it harder to crack. Also, the more frequently you change a password, the better. We also recommend using different passwords for different accounts. If the same password is used for multiple accounts, it becomes easier for hackers to infiltrate multiple accounts.
2 Connect Only to Protected Private WiFi Networks or (VPN) Virtual Private Networks
Always use private, password-protected WiFi networks to connect remotely. Security experts consider signing in to sensitive office networks with public WiFi or unsecured network connections akin to “swimming in shark-infested waters”—it’s only a matter of time before you get bit. Experts recommend consulting a trusted IT provider about setting up a VPN that can minimize the risk to devices and data.
3. Unusual Phrasings in subject lines/body, misspellings, poor-quality images or bad grammar
Although corona-virus-related phishing schemes are currently at an all-time high, the good news is that they aren’t much different from past attempts. Paying extra attention to message details—capitalization, punctuation, paragraph structure, sloppy design/formatting, or any language that seems out of the norm, makes detecting fake ones easier.
4. Don’t download unfamiliar attachments or click on unfamiliar links
In the age of remote work, collaborative OneDrive, Google Docs, or general Cloud sharing is a common way to redirect others to a malicious website. If you aren’t expecting a specific file from a specific sender, don’t open any attachments in an unknown message. This applies to links as well. To check if a link is safe, hover your mouse over the link to confirm the target URL matches what’s written (on a desktop or laptop). For extra precaution, type out the website to avoid being unknowingly redirected.
5. Activate multi-factor authentication (MFA) on every account you can
Many phishing schemes try to get you to re-enter your password for common apps or social media accounts—all in hopes that hackers can steal your password. Using multi-factor authentication can mitigate this since MFA requires something you know (your password) with something you have (a unique code delivered via text message or email).
6. Confirm the sender's email address
It’s easy for a hacker to mimic someone’s display or contact name—always double-check to confirm what shows up with the actual email address the message was sent from to make sure the sender is who he or she is claiming to be.
7. Do not respond to email correspondence from any financial institution
This goes for any communications via email or phone. You will not be prompted to sign in to your account or receive a call from your financial institution asking for your PIN or other personal information. In fact, most updates are sent with a 'do-not reply' email handle. Most official communications from financial firms are usually sent via snail mail. To ensure you are in contact with an actual representative of the firm, call the number on the back of your card or the phone number provided on your financial statements.
We hope you find these tips helpful.
Safe remote working and browsing!
- The CyberSecOp Team
Hackers Taking Advantage of Covid19 to attack major industries
With the unprecedented events of the past few months and no end in sight to the COVID-19 pandemic, hackers are leveraging the related chaos as a means of targeting, hi-jacking, infiltrating, and generally creating havoc among major industries around the globe.
The suddenness of the global governmental response combined with the rapid shift to remote work solutions has created a haphazard environment for many businesses that simply do not have the time to implement due diligence and information security controls. Unfortunately, the smart bad guys are taking advantage.
In California’s’ Bay Area, two school districts have become recent victims of breaches that exploited the unexpected thrust to online learning. Video conferencing sessions were hacked and infiltrated by uninvited guests; hundreds of online learning passwords were inadvertently exposed to public consumption. School administrators were left scrambling and ultimately had to ban all usage of video conferencing until proper security measures were implemented.
Hospitals and medical facilities are reeling from the virus spread, and hackers are paying no solace to this industry as they hammer away with targeted phishing campaigns and other website-based attacks. The World Health Organization (WHO) has reported several unsuccessful attacks against their network, with one geared around impersonating the WHO email system. Hammersmith Medicines Research (HMR) a UK based research team tasked with creating a Covid19 vaccine, unfortunately, did fall victim to a cyber-attack, as malicious actors were able to access and then post medical data from thousands of patients.
Education and healthcare are not the only sectors being infiltrated. Financial firms are being hit with targeted phishing attacks called whale or spear-phishing - Using Covid19 as the backdrop. Attackers are creating very specific, sophisticated emails that create a sense of urgency and ultimately increase the odds of the recipient becoming a victim.
It is an important time to ensure that your business leaders are setting an example by exhibiting best practice security behaviors that will ultimately set the tone and trickle down the entire organization. Top management commitment, effective strong policies that are communicated to the entire organization, and a measurable security awareness along with a sound risk management framework; are just some of the layers in security that will decrease the attack surface of any business.
CyberSecOp offers a full suite of cyber-security solutions that include:
Full Security Assessments
Gap Analysis
Policy Creation
Security Awareness Training and Measurement
24/7 Security Operations Center (SOC)
Ransomware Response
Penetration Testing
Vulnerability Scanning and Management
Forensics
VISO (Virtual Information Security Officer)