CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
Risk Mitigate vs. Remediate: Understanding the Key Differences in Risk Management
In risk management, cybersecurity, and compliance, the terms "mitigate" and "remediate" often surface. Though sometimes used interchangeably, they denote distinct approaches to addressing issues. Understanding the differences between mitigation and remediation is crucial for implementing effective strategies. This blog post will clarify these terms and explore their roles in risk management.
What Does It Mean to Mitigate?
Mitigation refers to the actions taken to reduce the severity, seriousness, or harmful effects of a risk or issue. It involves implementing measures to lessen the impact or likelihood of a potential problem. The goal of mitigation is not to eliminate the risk entirely but to make it more manageable and less damaging.
Examples of Mitigation:
Installing Firewalls: In cybersecurity, installing firewalls can mitigate the risk of unauthorized access to a network.
Employee Training: Providing training to employees on best practices for data security can mitigate the risk of data breaches.
Regular Maintenance: Regular maintenance on machinery can mitigate the risk of mechanical failures.
What Does It Mean to Remediate?
Remediation involves the actions taken to correct or fix a problem that has already occurred. It is a reactive approach that focuses on eliminating the issue and restoring the system or environment to its normal state. Remediation aims to resolve the problem at its source and ensure it does not recur.
Examples of Remediation:
Patching Software: After a vulnerability is discovered in software, applying patches to fix the vulnerability is a remediation action.
Data Recovery: Restoring lost data from backups after a data breach or accidental deletion is a form of remediation.
Cleaning Contaminated Sites: In environmental management, cleaning up polluted sites to remove contaminants is remediation.
Key Differences Between Mitigation and Remediation
1. Proactive vs. Reactive:
Mitigation is a proactive approach, aiming to prevent or lessen the impact of potential problems before they occur.
Remediation is a reactive approach, addressing and correcting issues that have already happened.
2. Objective:
Mitigation seeks to reduce risk and make potential issues more manageable.
Remediation seeks to eliminate problems and restore normalcy.
3. Scope:
Mitigation often involves ongoing measures and practices to continuously manage risk.
Remediation involves specific actions taken to resolve a particular issue.
Why Both Are Important
Effective risk management requires both mitigation and remediation strategies. Mitigation helps in minimizing the chances and impact of risks, while remediation ensures that any issues that do arise are swiftly and effectively dealt with. By combining these approaches, organizations can maintain a robust defense against potential threats and ensure rapid recovery from any incidents that occur.
Conclusion
Mitigation and remediation are essential components of risk management, each serving a unique purpose. Mitigation focuses on proactive measures to reduce the likelihood and impact of risks, while remediation addresses issues that have already occurred. By understanding and implementing both strategies, organizations can better protect themselves against threats and ensure a swift recovery when problems arise.
CyberSecOp Ranked #1 on Gartner Peer Insights for Security Consulting Services, Worldwide
CyberSecOp has earned the prestigious recognition of being the top customer-rated company on Gartner Peer Insights in the category of Security Consulting Services, Worldwide. This achievement is a testament to our commitment to excellence and customer satisfaction.
About Gartner Peer Insights Customers’ Choice
Gartner Peer Insights Customers’ Choice distinctions are awarded to vendors and products that consistently receive high customer ratings. This recognition reflects the trust and satisfaction of IT Enterprise professionals in our solutions.
The data collected by Gartner represents a top-level synthesis of the most valued vendor software products, as rated by those who use them daily. CyberSecOp's position at the top underscores our dedication to delivering outstanding security consulting services that meet the evolving needs of our clients.
Hackers Now Utilizing Standard Tools in Data Breaches
Several significant developments have emerged in today's dynamic cybersecurity landscape, highlighting threat actors' evolving tactics and the critical importance of robust cybersecurity measures.
Firstly, the emergence of ShrinkLocker, a ransomware variant exploiting Windows BitLocker, underscores cybercriminals' adaptability in leveraging built-in encryption features for malicious purposes.
Secondly, pharmacy benefit management company Sav-Rx's disclosure of a data breach affecting 2.8 million Americans underscores the ongoing challenges in safeguarding sensitive personal and medical information.
Standard tools are now being employed against organizations, as hackers no longer need to develop or learn new techniques, all while evading detection. This trend has significantly reduced the time required to execute a successful attack, particularly because most organizations rely on well-known software.
1. Ransomware Exploits Windows BitLocker
A new strain of ransomware, dubbed ShrinkLocker, has surfaced. It leverages the Windows BitLocker feature to encrypt victim data. Threat actors are manipulating BitLocker, a full-volume encryptor integrated into the Windows operating system, to encrypt entire hard drives, rendering data inaccessible. Researchers from Kaspersky have identified this new threat, highlighting the importance of robust cybersecurity defenses.
2. Sav-Rx Discloses Data Breach
Pharmacy benefits management company Sav-Rx has disclosed a data breach affecting 2.8 million Americans. The cyberattack, which occurred last October, resulted in the theft of personal data, including sensitive medical information. Investigations into the breach have been ongoing for eight months, underscoring the complex nature of cyber incidents and the importance of timely detection and response.
3. New ATM Malware Poses Global Threat
A new strain of ATM malware has been advertised on the dark web, claiming to compromise a significant percentage of ATMs worldwide. Targeting machines from leading manufacturers, including Diebold Nixdorf and NCR, the malware seriously threatens financial institutions and consumers. The availability of a three-day trial further underscores the sophistication of cybercriminal tactics.
4. Phishing Campaigns Targets Finance Companies
A phishing campaign employing a Python clone of the popular game Minesweeper has surfaced, targeting finance companies in Europe and the U.S. The campaign utilizes malicious scripts hidden within the game code to install remote management software, granting threat actors access to compromised systems. Vigilance against phishing attempts remains essential in mitigating cyber risks.
5. High-Severity Vulnerability Affects Cisco Firepower Management Center
Cisco has issued a warning regarding a high-severity vulnerability in the web-based management interface of the Firepower Management Center (FMC) Software. Exploitable via SQL injection, the vulnerability poses a significant risk to organizations using Cisco's security solutions. Immediate action is advised to mitigate potential exploitation.
6. Recovery Efforts Continue at Ascension Following Cyberattack
Healthcare network Ascension is gradually recovering from a recent cyberattack, which disrupted operations across its 140 member hospitals and senior care centers. The incident underscores the critical importance of cybersecurity in safeguarding patient care and sensitive medical information. Despite ongoing recovery efforts, challenges persist, highlighting the far-reaching impact of cyber incidents on healthcare organizations.
7. Courtroom Recording Software Compromised with Backdoor Installer
Justice AV Solutions (JAVS), a widely used technology for recording courtroom proceedings, has been compromised by hackers. A backdoor installer implanted in a software update allows threat actors to gain complete control of systems, posing significant privacy and security risks. Organizations utilizing JAVS technologies are advised to address the security issue and mitigate potential threats immediately.
Stay informed and proactive about evolving cyber threats. Cybersecurity remains a top priority for safeguarding digital assets and maintaining trust in an increasingly interconnected world.
In summary, the cybersecurity landscape continues to evolve, presenting complex challenges for organizations and individuals alike. By remaining vigilant, proactive, and leveraging robust cybersecurity solutions, stakeholders can effectively mitigate risks and safeguard against emerging threats in an increasingly interconnected digital environment.
Stay informed and proactive in the face of evolving cyber threats. Cybersecurity remains a top priority in safeguarding digital assets and maintaining trust in an increasingly interconnected world.
3CX DesktopApp Supply Chain Attack: What You Need to Know
After being alerted by several security researchers of an ongoing supply chain attack in its 3CX DesktopApp, 3CX is currently working on a software update. According to the company's CEO, Nick Galea, the malware affects the Windows Electron client for customers running update 7. As an immediate response, the company has advised users to uninstall and reinstall the app, and in the meantime, use its PWA (progressive web application) client instead.
3CX is a Voice Over Internet Protocol (VoIP) IPBX software development company with over 600,000 customers and 12 million users in 190 countries. Its 3CX DesktopApp allows users to make calls, chat, video conference, and check voicemail using their desktop. Some of its customers include BMW, Honda, Ikea, Pepsi, and Toyota.
The ongoing attack was detected by security researchers at Sophos, Crowdstrike, and SentinelOne, who observed malicious activity originating from a trojanized version of the 3CX DesktopApp. Sophos reported that the software is a digitally signed version of the softphone desktop client for Windows and is packaged with a malicious payload. The application has been abused by the threat actor to add an installer that communicates with various command-and-control servers.
According to SentinelOne, the threat actor registered a massive attack infrastructure in February 2022 and is tracking the attack under the name SmoothOperator. Researchers noted that it is a chain attack that takes advantage of the DLL side-loading technique to load a malicious DLL that's designed to retrieve an icon file payload. The trojanized 3CX DesktopApp is the first stage in a multi-stage attack chain that pulls ICO files appended with base64 data from GitHub and ultimately leads to a third-stage infostealer DLL still being analyzed as of the time of writing.
Crowdstrike also found that the malicious activity includes beaconing to actor-controlled infrastructure, deployment of second-stage payloads, and hands-on-keyboard activity in a small number of cases. Sophos noted that the DLL side-loading is designed in such a way that users will not realize any difference while using the application. The information stealer can gather system information and sensitive data stored in Google Chrome, Microsoft Edge, Brave, and Mozilla Firefox browsers.
In conclusion, the ongoing supply chain attack on the 3CX DesktopApp has prompted urgent action from the company, with a software update in progress and a recommendation for users to switch to its PWA client in the meantime. Security researchers have detected malicious activity originating from the trojanized version of the app, which has been abused by the threat actor to communicate with command-and-control servers and steal sensitive data. As always, it is important to stay vigilant and take immediate action in response to any security alerts or warnings.
Digital Transformation and the Future of IT Operations Management
IT Operations Management (ITOM) manages and maintains an organization's IT infrastructure and services to ensure they operate effectively and efficiently. Hybrid digital operations management solutions combine traditional ITOM and cloud-based technologies to manage IT operations across both on-premise and cloud environments.
A critical aspect of ITOM is protecting endpoints. Endpoints are devices and machines connected to an organization's network, including desktop computers, laptops, servers, and mobile devices. Protecting endpoints involves implementing security measures such as firewalls, anti-virus software, and intrusion detection systems to prevent unauthorized access, malware infections, and other security threats.
To effectively protect endpoints, ITOM teams must take a proactive approach to security, regularly monitoring and analyzing network traffic and proactively addressing potential vulnerabilities. This may involve implementing patch management processes, conducting regular vulnerability scans, and creating incident response plans to address security incidents quickly.
Hybrid digital operations management solutions can help ITOM teams protect endpoints by providing a centralized view of network activity and security events across both on-premise and cloud environments. These solutions can also automate many routine ITOM tasks, freeing IT staff to focus on complex security issues.
In summary, protecting endpoints is a critical aspect of ITOM. Hybrid digital operations management solutions can help organizations manage and secure their IT infrastructure across both on-premise and cloud environments.
Streamlining IT Operations and Enhancing Cybersecurity with Hybrid Solutions
Hybrid digital operations management solutions are closely related to cybersecurity because they can help organizations manage and secure their IT infrastructure and services effectively. In particular, these solutions can provide ITOM teams with a centralized view of network activity and security events across both on-premise and cloud environments, allowing them to detect and respond to security threats quickly.
Cybersecurity is a critical aspect of ITOM, and protecting endpoints is essential to securing an organization's IT infrastructure. Hybrid digital operations management solutions can help ITOM teams protect endpoints by providing tools and automation to monitor and manage network security and streamlining routine ITOM tasks, such as patch management and vulnerability scanning.
CyberSecOp, a cybersecurity consulting firm, helps organizations assess and manage their cybersecurity risk. Hybrid digital operations management solutions can help organizations to achieve better cybersecurity risk management by providing comprehensive monitoring and analysis capabilities, helping to detect and respond to security incidents quickly, and automating many of the routine tasks involved in managing and securing IT infrastructure.
In summary, hybrid digital operations management solutions are closely related to cybersecurity and can help organizations achieve better cybersecurity risk management. Furthermore, by partnering with cybersecurity consulting firms like CyberSecOp, organizations can maximize the effectiveness of their ITOM solutions and ensure they are adequately protecting their IT infrastructure against security threats.
Defending Against Cybersecurity Threats: Best Practices for Individuals and Organizations
Cybersecurity breaches have become increasingly common in recent years, affecting organizations and individuals alike. According to a report by Risk Based Security, there were over 18,000 publicly disclosed data breaches in the first half of 2021, resulting in the exposure of over 18 billion records. This represents a 47% increase in the number of breaches compared to the same period in 2020.
The consequences of a cybersecurity breach can be severe and long-lasting. Breaches can lead to the theft of sensitive data, financial losses, reputational damage, and legal liabilities. For businesses, a cybersecurity breach can result in lost productivity, customer loss, and damage to the company's brand and reputation.
To address the growing threat of cybersecurity breaches, organizations need to take a proactive approach to cybersecurity. This includes implementing robust security measures, regularly monitoring systems for signs of intrusion, and educating employees about safe online practices. Organizations should also have an incident response plan in place to quickly and effectively respond to a breach if one occurs.
Individuals can also take steps to protect themselves from cybersecurity breaches, such as using strong and unique passwords, enabling two-factor authentication, and being cautious of phishing attacks.
Defending against cyber security threats
Defending against cyber security threats is a complex and ongoing process that requires a combination of technical, administrative, and physical measures. Here are some general steps you can take to improve your cyber security posture:
Keep software and systems up-to-date: Regularly update your operating system, applications, and antivirus software to patch vulnerabilities and fix bugs.
Use strong and unique passwords: Use complex passwords and avoid using the same password across multiple accounts. Consider using a password manager to generate and store strong passwords.
Enable two-factor authentication: Enable two-factor authentication (2FA) on all your online accounts, which adds an extra layer of security beyond passwords.
Be cautious of phishing attacks: Be suspicious of emails or messages that ask for personal or financial information or contain suspicious links. Always verify the source before providing any information.
Use a firewall: A firewall can help protect your network by filtering traffic and blocking unauthorized access.
Back up your data regularly: Back up your important data regularly to protect against data loss in case of a security breach or hardware failure.
Limit access to sensitive data: Restrict access to sensitive data to only those who need it and use secure methods to share data.
Educate yourself and others: Stay informed about the latest cyber security threats and educate others, including employees, family members, and friends, about safe online practices.
Remember, cyber security is an ongoing process, and it requires constant attention and vigilance. By implementing these steps, you can help protect yourself and your organization from cyber threats.
In conclusion, cybersecurity breaches are a growing threat that can have severe consequences for both organizations and individuals. By implementing robust security measures and staying vigilant, organizations and individuals can help reduce the risk of a breach and minimize the impact if one occurs.
Chat GPT 3 and Chat GPT 4: How They're Helping the World
In the last few years, artificial intelligence has revolutionized the way we interact with technology. One of the most remarkable developments in this field is the creation of advanced chatbots powered by natural language processing (NLP). Among them, Chat GPT 3 and Chat GPT 4 are two of the most popular and powerful NLP models.
Chat GPT 3, released in 2020 by OpenAI, is a third-generation language model that can generate human-like responses to a wide range of prompts, from simple questions to complex essays. Its developers trained it on a massive corpus of text data, including books, articles, and websites, using an unsupervised learning algorithm that allowed it to learn patterns and structures in language without explicit guidance from humans.
Since its release, Chat GPT 3 has been used for a variety of applications, such as chatbots, language translation, content creation, and even coding. Its ability to understand natural language and generate coherent responses has made it a valuable tool for businesses, developers, and researchers alike.
Chat GPT 4, which is currently in development and expected to be released in the near future, promises to take NLP to the next level. According to OpenAI, Chat GPT 4 will be even more powerful and versatile than its predecessor, with the ability to perform tasks that are currently beyond the reach of AI, such as reasoning and common-sense understanding.
The Benefits of Chat GPT 3 and Chat GPT 4
The benefits of Chat GPT 3 and Chat GPT 4 are numerous and far-reaching. Here are a few examples:
Improved Customer Experience: Chatbots powered by Chat GPT 3 and Chat GPT 4 can provide personalized and natural interactions with customers, improving the overall experience and satisfaction.
Language Translation: The ability of Chat GPT 3 and Chat GPT 4 to understand and generate language can be used to create better translation services, improving communication and understanding between people from different cultures and languages.
Content Creation: Chat GPT 3 and Chat GPT 4 can generate high-quality content for a variety of purposes, such as marketing, journalism, and education, saving time and resources for businesses and individuals.
Education: Chat GPT 3 and Chat GPT 4 can be used to create intelligent tutoring systems, helping students learn more effectively and efficiently.
Who is Using Chat GPT?
Many companies and organizations are already using Chat GPT 3 for various applications. Some of the notable examples are:
Microsoft: Microsoft has integrated Chat GPT 3 into its Power Virtual Agents platform, enabling developers to create conversational AI experiences with ease.
OpenAI: OpenAI has developed GPT-3-powered chatbots that can perform various tasks, such as writing emails, generating code, and even composing poetry.
Intel: Intel has used Chat GPT 3 to create an AI-powered chatbot to help customers find the right products and services.
The Future of Chat GPT
As AI technology continues to evolve, the future of Chat GPT looks promising. With the release of Chat GPT 4, we can expect even more advanced and sophisticated NLP models that can perform tasks that were previously thought impossible. In the coming years, we may see the emergence of AI-powered virtual assistants that can understand and respond to our needs naturally and intuitively, revolutionizing the way we interact with technology.
Conclusion
Chat GPT 3 and Chat GPT 4 are two of the most exciting developments in the field of artificial intelligence. Their ability to understand and generate language has opened up a world of possibilities.
Staying on the Offence: SIEM & SOC Benefits
Many businesses these days do not have the resources or the skill set in-house to effectively create, administer and manage a fully operational Security Operations Center. A Security Operations Center (SOC) is a critical component of an organization's overall security strategy. It is a centralized team responsible for detecting, analyzing, and responding to security incidents in real time. In today's rapidly changing threat landscape, having a SOC is more important than ever.
Benefits of SOC as a SIEM
Protects against cyber threats: A SOC monitors and analyzes the organization's networks, systems, and applications for signs of cyber threats, such as hacking attempts, malware infections, and phishing attacks. By detecting threats early and taking action to prevent or mitigate them, a SOC helps to protect the organization from harm.
Increases efficiency: By centralizing security operations, a SOC helps organizations to be more efficient in their response to security incidents. The SOC team can respond quickly to incidents without coordinating with multiple departments and can share information and resources more efficiently.
Enhances compliance: Organizations are increasingly required to meet strict security and privacy regulations, such as the Payment Card Industry Data Security Standard (PCI DSS) or the General Data Protection Regulation (GDPR). A SOC can help organizations to comply with these regulations by monitoring their networks and systems for compliance and ensuring that any necessary changes are made.
Improves incident response: A SOC provides a dedicated team trained to respond to security incidents. This team can quickly contain and resolve incidents, reducing the impact on the organization and its customers.
In conclusion, having a security operations center is essential for organizations looking to protect their assets, reduce the risk of security incidents, and comply with industry regulations. By centralizing security operations, a SOC helps organizations respond to incidents more efficiently and effectively, ultimately reducing the risk of harm. CyberSecOP utilizes a US-based SOC team that is available 24/7/365 to ensure your business is protected by the latest ransom and malware threats out there.
The Majority Of US Defense Contractors Fails To Meet Basic Cybersecurity Standards.
According to the study, this could have severe consequences for defense contractors, with nearly half losing up to 60% of their revenue if DoD contracts are lost.
"CMMC is a set of commercially reasonable standards to protect data," said CyberSecOp CISO. Organizations must address it as a part of doing business or risk losing the contract. “Nearly nine in ten (90%) of US defense contractors need to meet basic cybersecurity regulatory requirements.
According to the survey, defense contractors still need to implement basic standards. A sampling:
· 35% have security information and event management (SIEM)
· 39% have an endpoint detection response solution (EDR)
· 18% have a vulnerability management solution
· 28% have multi-factor authentication (MFA)
Defense contractors are being targeted by state hackers.
Defense contractors are a popular target for nation-state groups due to the sensitive information they possess about the US military. The Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory in October 2022 highlighting advanced persistent threat (APT) activity detected on a defense organization's enterprise network.
CyberSecOp CISO is concerned that four out of five defense contractors reported a cyber-related incident, with nearly three out of five reporting business loss due to a cyber-related event.
CyberSecOp is a CMMC-AB REGISTERED PROVIDER ORGANIZATION (RPO)
DOD has made an effort to simplify CMMC, but it is undoubtedly still complicated. CMMC is based on several other standards, including DFARS, 800-171, and ISO 27001. Utilizing all the above information security standards make it very challenging for most DOD contractors to copy with CMMC. Get compliant with CyberSecOp CMMC Assessment, Security Program & Advisory Services.
NIST Practices in Cyber Supply Chain Risk Management
Company Overview
Through its products and solutions, CyberSecOp offers cyber security tools, such as network, email, and mobile security as well as forensic investigation following a breach. As stated by the business:
The landscape of cyber threats is quickly changing. Organized threat actors are laser-focused on hacking systems and stealing data using sophisticated attacks that are tailored to compromise a specific target and evade traditional signature-based defenses, a key component of what currently constitutes basic cyber hygiene, instead of the broad scattershot attacks of the past.
SolarWinds Supply Chain Against US Agencies
The recent SolarWinds attack made the entire world aware of the danger of a cyber supply chain attack, or an attack on or through the vendors or suppliers of your company. It is becoming increasingly apparent that your business and its data are only as secure as the weakest link among your suppliers, even if you take all the necessary precautions to secure your own computer systems. This risk includes potential computer system attacks as well as the possibility of a disruption to the operations of your suppliers.
Common Risks for Supply Chains
Many risks can cause supply chain disruption, and those threats can have severe consequences for your business. Some of the more common risks are:
Cybersecurity Risks
Hackers can enter your supply chain and then move throughout your firm. Cybersecurity breaches can also wreak havoc on your day-to-day operations. So information security should be at the forefront of your mind when considering new vendors.
Compliance Risks
You’ll need to make sure your vendor can meet any regulatory compliance requirements your company has, which will subsequently affect your supply chain. For example, suppose a vendor bribes foreign government officials on your behalf. In that case, your company will be charged with violating the U.S. Foreign Corrupt Practices Act and all the legal ramifications that it entails.
Financial Risks
When collaborating with other companies, the risk of financial loss is always present. For example, if your contractor goes bankrupt or faces its own supply issues, this could have significant economic consequences for you and your organization.
Reputational Risks
Reputational risk is the most unpredictable type of risk because incidents that affect your reputation might happen out of nowhere. Damage to your contractors’ reputations can also harm yours, so consider reputational risk when choosing providers.
Cyber Supply Chain Principles and Supply Chain Risks
NIST identifies primary principles to consider for successful C-SCRM. These considerations are comprehensive and broadly apply to critical infrastructure, business processes, and intellectual property.
Understand the Security Risks Posed by Your Supply Chain
Examine the specific dangers that each supplier exposes you to, the products or services they provide, and the value chain as a whole.
Supply chain risks come in a variety of shapes and sizes. A supplier, for example, may not have enough security, may have a hostile insider, or its employees may not correctly handle your information. Gather sufficient information to better evaluate these security concerns, such as an insider data collection report or risk assessment.
Develop Your Organizational Defenses With “Assume Breach” in Mind
Assuming a breach means an organization approaches its cybersecurity posture by anticipating that its networks, systems, and applications are already compromised. Treating an internal network as if it’s as open as the internet readies the system for various threats and compromises.
Set Minimum Security Requirements for Your Suppliers
You should establish minimum security requirements and metrics for suppliers that are justified, proportionate, and achievable. Make sure that these standards reflect not only your evaluation of security risks but also the maturity of your suppliers’ security arrangements and their capacity to achieve the requirements you’ve set.
Minimum requirements should be documented and standardized to streamline enforcement. This technique will help you lower your effort and prevent giving these parties unnecessary work.
Cybersecurity is a People, Process, and Technology Problem
People, processes, and technology are the triad of solving problems. Supply chain management also focuses on these three areas to enhance supply chain performance, make it more secure, and do more with less.
Look at the Entire Landscape
There are multiple security standards that interact with each other in a variety of cybersecurity frameworks and best practices. A few examples are the NIST Cybersecurity Framework (CSF), Center for Internet Security (CIS) Controls, and the International Organization for Standardization (ISO) series.
To be efficient and flexible, your C-SCRM should follow the guidelines established by your third-party risk management program. That is especially important today, where outsourcing is common. Always remember that your C-SCRM program is only as good as the data security provided by your least secure third- or fourth-party supplier.
Encourage the Continuous Improvement of Security within Your Supply Chain
Encourage your vendors to keep improving their security measures, emphasizing how this will help them compete for and win future contracts with you.
Advise and support your suppliers as they seek to make these improvements. Allow your suppliers time to achieve improvements but require them to provide you with timelines and project plans.
Listen to and act on any issues arising from performance monitoring, incidents, or bottom-up supplier reports that imply current approaches aren’t functioning as well as they should.
Best Practices for Cyber Supply Chain Risk Management
An organization can employ a variety of best practices in its C-SCRM program. Best practices improve the ability to identify and mitigate potential risks over time. In addition, these practices include remediation steps to apply if you experience a data breach.
Here is a list of some of the best practices to keep in mind as you set to work on your cyber supply chain risk management program:
Security requirements need to be defined in requests for proposals (RFP). In addition, use security questionnaires to hone in on the current standards practiced by each bidder.
An organization’s security team must assess all vendors, and you must remediate vulnerabilities before sharing information, data, or goods and services with them.
Engineers must use secure software development programs and keep up-to-date on training.
Software updates need to be available to patch systems for vulnerabilities, and they must be downloaded and installed in real time.
Dedicated staff that is assigned to ongoing supply chain cybersecurity activities.
Implement and enforce tight access controls to service vendors.
The new NIST guidance reflects the increased attention companies are paying to manage cyber supply chain risks. It is a useful resource for enterprises of all sizes, though some of the recommendations may be too burdensome or complex for smaller organizations to reasonably adopt. Small businesses may lack the sufficient purchasing power to require their suppliers to complete certifications or participate in contingency planning, as NIST suggests, and may not have the resources to create internal councils and intricate review procedures.
16 Microsoft Outlook Security & Optimization Tips
This article provides advice on how to increase Outlook productivity, improve security, and get the most out of this critical program. We can assist you in protecting your account if you receive a link in an email that appears to be from your bank but isn't fake notifications from social networking sites or malicious advertisements. We stay up to date on the latest scams, so you don't have to. Though we protect your account from a variety of threats, there are several steps you can take to keep your account and personal information safe.
Outlook Security Tips
1. Outlook user Email Security Tips
If you see a yellow safety bar at the top of your message, then the message contains blocked attachments, pictures, or links to websites. Ensure you trust the sender before downloading any attachments or images or clicking any links. Emailing the sender to verify they intended to send you an attachment is also a good practice for any attachments you're not expecting.
A red safety bar means that the message you received contains something that might be unsafe and has been blocked by Outlook.com. We recommend that you don't open those email messages and delete them from your inbox.
When you add an address to your Outlook safe sender’s list, all messages you receive from that address go right to your inbox. Adding a sender to your blocked sender’s list sends messages from that address to your Junk email folder.
If the URL that appears in the address bar when you sign in doesn't include login.microsoftonline.com or login.live.com, you could be on a phishing site. Don't enter your password. Try to restart your browser and navigate to login.microsoftonline.com or Outlook.com again. If the problem continues, check your computer for viruses.
2. Use multi-factor authentication.
Multi-factor authentication (MFA) also known as two-step verification, requires people to use a code or authentication app on their phone to sign into Outlook and Microsoft 365, and is a critical first step to protecting your business data. Using MFA can prevent hackers from taking over if they know your password.
3. Protect your administrator accounts.
Administrator accounts (also called admins) have elevated privileges, making these accounts more susceptible to cyberattacks. You'll need to set up and manage the right number of admin and user accounts for your business. We also recommend adhering to the information security principle of least privilege, which means that users and applications should be granted access only to the data and operations they require to perform their jobs.
4. Use preset security policies.
Your subscription includes preset security policies that use recommended settings for anti-spam, anti-malware, and anti-phishing protection.
5. Protect all devices.
Every device is a possible attack avenue into your network and must be configured properly, even those devices that are personally owned but used for work.
Help users set up MFA on their devices
Protect unmanaged Windows and Mac computers
Set up managed devices (requires Microsoft 365 Business Premium or Microsoft Defender for Business)
6. Train everyone on email best practices.
Email can contain malicious attacks cloaked as harmless communications. Email systems are especially vulnerable because everyone in the organization handles email, and safety relies on humans making consistently good decisions with those communications. Train everyone to know what to watch for spam or junk mail, phishing attempts, spoofing, and malware in their email.
7. Use Microsoft Teams for collaboration and sharing.
The best way to collaborate and share securely is to use Microsoft Teams. With Microsoft Teams, all your files and communications are in a protected environment and aren't being stored in unsafe ways outside of it.
Use Microsoft Teams for collaboration.
Set up meetings with Microsoft Teams
Share files and videos in a safe environment
8. Set sharing settings for SharePoint and OneDrive files and folders.
Your default sharing levels for SharePoint and OneDrive might be set to a more permissive level than you should use. We recommend reviewing and if necessary, changing the default settings to better protect your business. Grant people only the access they need to do their jobs.
9. Use Microsoft 365 Apps on devices.
Outlook and Microsoft 365 Apps (also referred to as Office apps) enable people to work productively and more securely across devices. Whether you're using the web or desktop version of an app, you can start a document on one device and pick it up later on another device. Instead of sending files as email attachments, you can share links to documents that are stored in SharePoint or OneDrive.
10. Manage calendar sharing for your business.
You can help people in your organization share their calendars appropriately for better collaboration. You can manage what level of detail they can share, such as by limiting the details that are shared to free/busy times only.
11. Maintain your environment.
After your initial setup and configuration of Microsoft 365 for business is complete, your organization needs a maintenance and operations plan. As employees come and go, you'll need to add or remove users, reset passwords, and maybe even reset devices to factory settings. You'll also want to ensure people have only the access they need to do their jobs.
Top 10 Microsoft Outlook Tips to Boost Productivity
12. Create folders to organize your emails.
This is the apparent first step if you want to simplify how you use email. However, it may also be the most difficult, particularly if your inbox is overloaded. Even so, it makes the most sense to organize your emails into a user-friendly folder system so that you won't have to spend hours sifting through hundreds of emails in search of the one you're looking for. An easy-to-use folder system will also encourage you to respond to each email as it comes in rather than putting it off till later all the time.
13. Utilize the simple email templates provided by Outlook.
Save one of the emails as a template if you frequently write the same type of message so that you may conveniently access it in the future when you're ready to use that previously saved form.
14. Accept the web-based future of Outlook.
Most of the email, calendar, and contact infrastructure is moved to a web-based view in Outlook Office 365, and other recent versions of the program so that it can be accessed on any device. Even sending brief notes amongst coworkers is straightforward with Microsoft's Send email software for cellphones, which also enters all the communications into your Microsoft Outlook history for convenient archiving and access.
15. Adjust desktop notifications so that you only receive critical messages.
If you get a notification every time a message arrives in your inbox, you'll be distracted. But you don't want to miss important emails, so disable desktop alerts in File > Options > Mail Options, then create a custom rule to only display alerts for messages sent to you by specific contacts.
16. Make a folder for frequently used searches.
Looking for a specific folder among a hundred can be time-consuming if you still do so by typing words or phrases into the search field above the message list. You can, however, make the job easier by creating a "Search" folder for frequently searched terms.
To make one, go to the "Folder" tab and right-click on "Search Folder.
Gartner Recognizes CyberSecOp - Ranked 2nd for Security Consulting Worldwide.
CyberSecOp receives the highest overall score on Gartner Peer Insights for Security Consulting Services, Worldwide in 2022.
June 8, 2022 - CyberSecOp today announced that its Security Consulting Services received a 4.9 out of 5 overall rating from Gartner Peer Insights, placing CyberSecOp in the top two on Gartner’s Security Consulting Services Worldwide category.
"Peer reviews are extremely valuable for evaluating any purchase decision," said Josh Bauer, Executive Director at Loxo Oncology/Lilly. “CyberSecOp appears to actively and continuously listen to us as a customer to ensure they deliver innovative solutions and a valuable user experience."
“CyberSecOp is honored to receive our current ranking status and client feedback, and we will continue to prioritize customer satisfaction across the board." Vincent LaRocca, CEO & Co-Founder.
2022 Gartner Peer Insight
Gartner Peer Insights is the firm's platform for rating and reviewing enterprise technology solutions by end-user professionals for end-user professionals. Through user-contributed reviews from people who have actually used the services, the rating system combines expert opinions and peer insights. Peer Insights User Reviews offers a suite of interactive features for technology buyers, including the ability to customize evaluation criteria to create a quadrant view tailored to the user's goals and priorities. The platform employs rigorous methodologies, processes, and quality standards to deliver unbiased research and authentic peer reviews.
What is Gartner’s research?
Gartner research: Trusted insight for executives and their teams
Gartner research, which includes in-depth proprietary studies, peer and industry best practices, trend analysis, and quantitative modeling, enables us to offer innovative approaches that can help you drive stronger, more sustainable business performance.
Gartner research is unique, thanks to:
Independence and objectivity
Our independence as a research firm enables our experts to provide unbiased advice you can trust.
Actionable insights
Gartner’s research is unbiased, containing vital takeaways and recommendations for impactful next steps.
Proprietary methodologies
Our research practices and procedures distill large volumes of data into clear, precise recommendations.
Don't let a cyber security breach damage your reputation
Cybersecurity breaches have cost many organizations some of their largest clients. While most organizations quickly hire legal experts, public relations teams, and a cyber security firm like CyberSecOp, the reputation damages have already begun. For example, your client may not have access to your services for hours before you realize that your system was affected.
Prime attack time
Attackers are strategic with time selection to minimize their activities being seen by employees. Most attackers operate on weekends or at night, knowing that most organizations’ employees do not access or monitor systems at this time.
When does reputation damage begin?
Reputation issues may begin long before the organization knows about an attacker. Some attackers disclose information on social media so that the organization will act quickly to their demands. Most cybercriminals spend an average of three months on clients’ systems before they act, but by this point, they may have already sold your data on the dark web or to your competitor.
Disclosing sensitive information violates privacy policies and requirements such as CCPA, GDPR, and some states’ and countries’ data protection regulations or requirements. The data disclosed may also include clients and your client’s customer information, putting your clients at risk. They, too, need to report the breach to their customers and provide the necessary protection to protect their customer’s credit and identity.
Reputation damage extends to your client.
At this point, not only is your organization’s reputation is in jeopardy, but also the reputation of your client and your client’s customers. All of these expenditures may be a liability to your organization if the breach is on your side, especially if there is evidence that you didn’t take due care regarding your organization’s security posture.
Conclusion
Defense-in-depth security program
Having a defense-in-depth security program such as those offered by CyberSecOp, cannot only save your business money but can also help you compete against other companies that have not implemented a security program. Most organizations have implemented a vendor management program to mitigate their threat against a third-party risk. A security program that includes third-party risk management is critical to identifying and remediating internal and external threats.
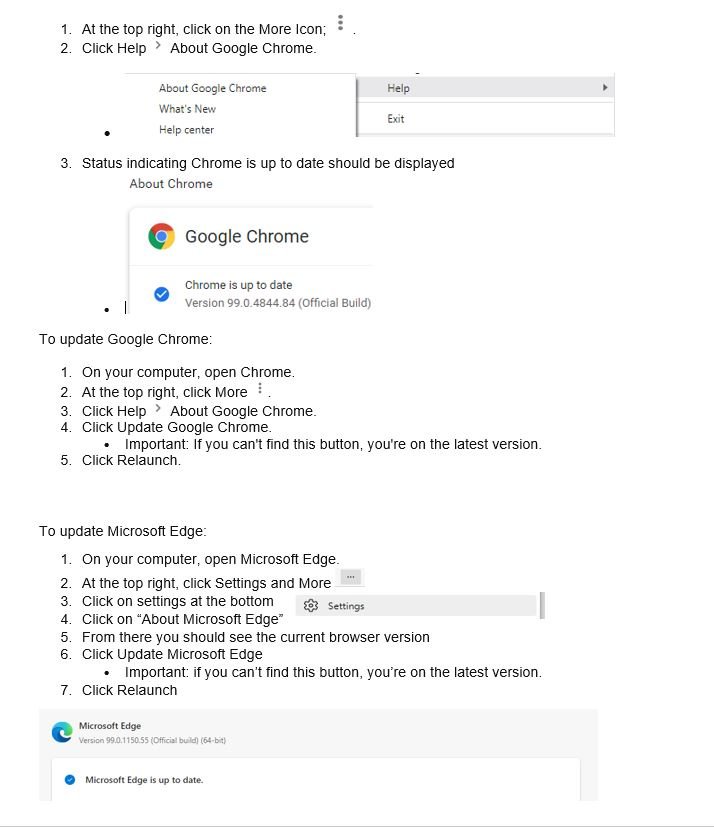
Chrome and Edge Should Be Updated Due to a Zero-Day Vulnerability
Google and Edge has released an update to remediate a critical zero-day chrome exploit. The zero-day is a weakness in Edge and Chrome's JavaScript engine that can be used by hackers to inject their code into your browser. Google explains for zero-day exploit CVE-2022-1096, first reported to the company by an anonymous tip on March 23. As part of our commitment to continuous support in security monitoring and enhancement we advise all clients to update to Chrome version 99.0.4844.84 and Microsoft Edge 99.0.1150.55 of as soon as possible.
DETAILS AND REMEDY FOR MICROSOFT AND GOOGLE
At this time Microsoft and Google won't provide much more information other than admitting there have already been attacks leveraging this zero-day weakness and keeping some information away from the public as a safety measure, stating that full details on how the exploit worked won't be made public until most users have the fix. Fortunately, this time Microsoft and Google was apparently able to issue a patch before the exploit became widely known.
Normally Chrome updates happen in the background when you close and reopen your computer's browser.
Microsoft issued its own notice and said the issue was fixed in Edge.
Please follow the steps below to ensure you have the latest version of Chrome.
Remediation Efforts
On your computer, open Chrome.
Author: Tanvir Ahmed
ADVISORY: Reports of possible digital breach
ADVISORY: Reports of possible digital breach
Okta investigating reports of possible digital breach
Lapsus$, a cyber extortion gang, has announced that they have breached Microsoft and Okta.
The gang has leaked torrents containing source code for Bing, Bing Maps, and Microsoft Cortana, as well as a screenshot of an internal Microsoft Azure DevOps account. They also claim to have had “Superuser/Admin” access to Okta’s systems for two months, and said its focus was “only on Okta customers.”
Both Microsoft and OKTA have started an investigation to confirm or disprove they’ve been breached.
Recommended Actions:
These attacks are a striking reminder of the supply chain’s cyber risks - Real risks brought to organizations by use of softwares and systems like OKTA, Microsoft, as well as many others.
Please work with your vCISO or Risk Manager to ensure the proper Vendor Security controls and processes are in place as well as other vital security controls that will drastically reduce the possibility of these dangerous hacks spilling into your network and systems.
Author: Michael Sardari
CISA's 'Shields Up' Alert Highlights Foreign Cyberthreats
Cyberwarfare is the battlefield of today. Increased geopolitical tensions stemming from Russia's unprovoked attack on Ukraine has led to CISA (the Cybersecurity & Infrastructure Security Agency) issuing a "Shields Up" bulletin. Every organization must be prepared to respond to disruptive cyber activity, especially those in critical infrastructure fields.
Here are some tips to help you keep your organization safe in these trying times.
Reduce the likelihood of a damaging cyber intrusion
Use MFA or Multi-Factor-Authentication everywhere.
Ensure all Systems are patched and up to date.
Consider increasing patch frequency if not already real-time.
Take steps to quickly detect a potential intrusion
Run, update and monitor a strong Endpoint Protection Program.
Consider increasing Spam and Phishing filter sensitivity.
Disable any non-essential ports and protocols, specifically through external gateways.
Ensure that the organization is prepared to respond if an intrusion occurs
Review your incident response plan and ensure it is up to date and all parties are clear on their roles.
Maximize your organization's resilience to a destructive cyber incident
Ensure that you are taking regular backups and that your backups are encrypted and immutable.
Test your backup and recovery procedures.
Communicate with your users, the best and strongest defense is a well-educated and well-prepared workforce.
If you are a CyberSecOp customer today in either our vCISO or vSOC program your risk manager will be reaching out shortly to ensure this guidance is being implemented to the extent possible within your organization.
If you are not currently enrolled in one of our plans and need assistance assessing your posture and capabilities, please feel free to reach out.
Ransomware Protection with Zero Trust Security
Zero Trust Security Architecture: Why is the Zero Trust Security Model important?
Endpoints represent the most significant attack surface, according to IDC, with over 70% of breaches originating on the endpoint. Organizations have a diverse mix of endpoints connected to their network, whether laptops, mobile endpoints, servers, firewall, wireless hotspots, or IoT devices. Zero-trust architecture works to ensure that users, devices and network traffic are all verified and subjected to least-privilege rules when accessing trusted resources. This way, compromised assets are limited in their scope and an attacker is prevented from moving laterally across the network.
With the rise of remote endpoints and high-profile ransomware attacks, businesses face more cybersecurity threats than ever before. Traditional network security models which assume users and computing devices within the “trusted” network environment are free from compromise and cannot secure organizations. Businesses are also now recognizing that attacks are more sophisticated and that internal networks are no longer more trustworthy than what lies outside the firewall. CyberSecOp and the security community recognized that Zero-trust security is the ultimate protection against ransomware.
Zero Trust Security Optimization
Zero Trust Network (ZTN) concept follows the mantra of never trust, always verify. Through this approach, organizations can reduce their open attack surface and adopt enhanced security capabilities beyond traditional defenses. Zero Trust enables organizations to reduce risk of their cloud and container deployments while also improving governance and compliance. Organizations can gain insight into users and devices while identifying threats and maintaining control across a network.
Traditional – manual configurations and attribute assignment, static security policies, least-function established at provisioning, proprietary and inflexible policy enforcement, manual incident response, and mitigation capability.
Advanced – some cross-solution coordination, centralized visibility, centralized identity control, policy enforcement based on cross-solution inputs and outputs, some incident response to pre-defined mitigations, some least-privilege changes based on posture assessments.
Optimal – fully automated assigning of attributes to assets and resources, dynamic policies based on automated/observed triggers, assets have dynamic least-privilege access (within thresholds), alignment with open standards for cross pillar interoperability, centralized visibility with retention for historical review
10 Ransomware Prevention Best Practices
Below are 10 best practices to help security professionals improve endpoint management:
CyberSecOp Managed Zero Trust security services were built with a new approach that creates zero-trust connections between the users and applications directly to solve this unique challenge. As a scalable, cloud-native platform, it enables digital transformation by securely connecting users,
devices, and applications anywhere, without relying on network-wide access. This platform is delivered by five key architecture attributes, unique to the CyberSecOp Managed Zero Trust Security services that together enable organizations to provide strong security and a great user experience to their employees and customers.
Multi-Factor Authentication (MFA) is is an electronic authentication method in which a computer user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication.
Email Security is critical because 74% of organizations in the United States experienced a successful phishing attack. Implementing email security gateway, DMARC, SPF, DKIM, stronger encryption, and MFA can reduce email compromise by over 98%.
CyberSecOp endpoint management solution that supports application isolation and containment technology is a form of zero-trust endpoint security. Instead of detecting or reacting to threats, it enforces controls that block and restrain harmful actions to prevent compromise. Application containment is used to block harmful file and memory actions on other apps on the endpoint. Application isolation is used to prevent other endpoint processes from altering or stealing from an isolated app or resources. This can prevent ransomware from being deployed on devices.
CyberSecOp endpoint management solution support Protective DNS Service (PDNS) refers to a service that provides Domain Name Service (DNS) protection (also known as DNS filtering) by blacklisting dangerous sites and filtering out unwanted content. It can also help to detect & prevent malware that uses DNS such as URL in phishing emails and hiding tunnels to communicate attackers' command and control servers.
CyberSecOp endpoint management solution supports bandwidth throttling so that remote endpoints can be continuously patched and secured rather than having to periodically send IT resources to remote locations. Our solution delivers patch management over the internet without requiring corporate network access. This ensures that internet-facing systems are patched in a proactive, timely manner rather than IT having to wait for these devices to visit the corporate network before they can be scanned and remediated.
CyberSecOp endpoint management reduces administrative overhead of endpoint management solutions to accommodate tight budgets and future growth. Our solutions support many endpoints using a single management system.
Consolidate endpoint management tools. Use a single tool to patch systems across Windows, Mac and variations of Unix operating systems to simplify administration, minimize the number of open network ports, and reduce the number of active agents on endpoints.
Validate that the endpoint management solution provides accurate, real-time endpoint data and reports. End users make changes to endpoints all the time and information that is hours or days old may not reflect a current attack surface.
CyberSecOp endpoint management allows administrators to apply patches that address the highest levels of risk first based on current endpoint status. This gives the biggest impact from remediation efforts.
Make sure the endpoint management solution enforces regulatory and corporate compliance policies on all endpoints constantly to avoid unintended drift and introduction of new vulnerabilities.
To conclude
Ransomware protection needs to go beyond detecting and blocking an initial malware infection at the email perimeter. Malware can enter your organization by other means, and cyber attacks often use the web channel to contact command and control servers and download the encryption keys necessary to complete the cyber attack.
Why a vCISO may be right for your organization cyber security
Since the start of the COVID19 pandemic, several societal changes have shaped how firms function in the current climate. Many firms have implemented a work-from-home model to help prevent the spread of the novel coronavirus and ensure employees are comfortable with their surroundings. What many organizations didn’t anticipate are the cyber security-related risks.
Once employees leave the security of their offices, they increase their attack surface and open themselves and their employer to attendant Information Security vulnerabilities that may come with working remotely. Remote work changes have prompted heightened instances of cyber attacks that have worsened in style and quantity over time. The pandemic has created the perfect environment for hackers to attack with more accuracy, and with greater cost to the firm, than ever. Learn more about remote working in relation to the pandemic.
How a vCISO can help protect your firm from cyber attacks
A vCISO can function as an additional set of eyes that constantly monitors your firm’s security operations. The additional security will aid in preventing possible security breaches. A vCISO can also bring expertise to assist in developing a strategy to strengthen your firm’s security program.
The benefits of a vCISO:
A board-level cyber security consultant fulfilling the CISO responsibilities
A team of security risk assessment experts
Employee security awareness education
Dark Web Monitoring 24/7/365
Full enterprise risk management for any required compliance
Comprehensive third party/vendor management
Compliance support for NIST, ISO, GDPR, CCPA, NYDFS, PCI/DSS among others
A more affordable approach as opposed to hiring a full-time CISO
Eliminate internal training costs and have our seasoned experts handle your security
CyberSecOp offers vCISO services. Click here to learn more.