CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
Chrome and Edge Should Be Updated Due to a Zero-Day Vulnerability
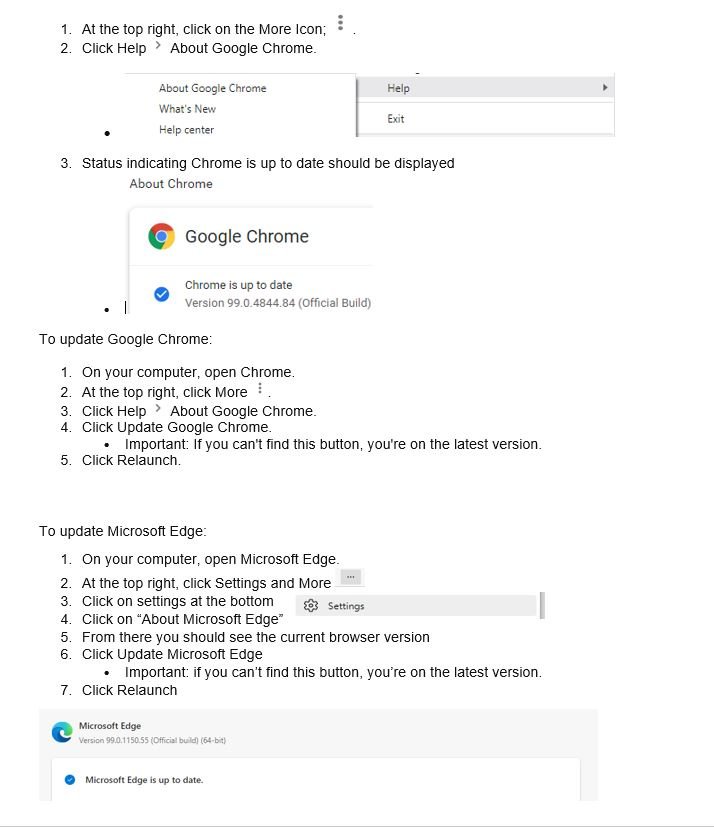
Google and Edge has released an update to remediate a critical zero-day chrome exploit. The zero-day is a weakness in Edge and Chrome's JavaScript engine that can be used by hackers to inject their code into your browser. Google explains for zero-day exploit CVE-2022-1096, first reported to the company by an anonymous tip on March 23. As part of our commitment to continuous support in security monitoring and enhancement we advise all clients to update to Chrome version 99.0.4844.84 and Microsoft Edge 99.0.1150.55 of as soon as possible.
DETAILS AND REMEDY FOR MICROSOFT AND GOOGLE
At this time Microsoft and Google won't provide much more information other than admitting there have already been attacks leveraging this zero-day weakness and keeping some information away from the public as a safety measure, stating that full details on how the exploit worked won't be made public until most users have the fix. Fortunately, this time Microsoft and Google was apparently able to issue a patch before the exploit became widely known.
Normally Chrome updates happen in the background when you close and reopen your computer's browser.
Microsoft issued its own notice and said the issue was fixed in Edge.
Please follow the steps below to ensure you have the latest version of Chrome.
Remediation Efforts
On your computer, open Chrome.
Author: Tanvir Ahmed
Using Linux Won't Save You from Ransomware - Here's Why
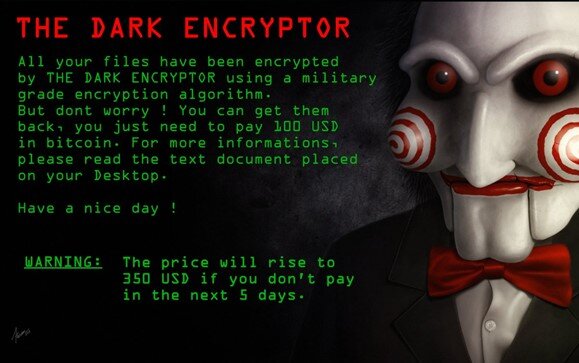
"Ransomware attacks are becoming more targeted, sophisticated, and costly, even as the overall frequency of attacks remains consistent." (FBI, 2019)
Since early 2018, there has been a sharp spike in the cleverness, thoroughness, and precision of the security breaches we see in the ransomware landscape. Regardless of attack vector - whether it's from phishing, vishing, or the classic insider threat - once ransomware is on your computer, it's incredibly difficult to restore your files. It takes some serious intervention to stand a chance of recovering your business (or personal) data.
The easiest solution is to get the appropriate key and decryption tool, and use them together to unlock your files...but typically you only receive those resources in exchange for paying the ransom, and many companies can’t afford the ransom at its original price. By that time, there's a good chance you've taken a catastrophic financial blow. From hospitals, to insurance companies, to banks, there are plenty of highly valuable (and highly vulnerable) assets to be manipulated, and threat actors don’t hesitate to put lives at stake for the benefit of their wallets.
So how can we prevent these breaches? What is the key to staying safe from attackers?
The answer may be simpler than you think.
The three most impactful measures you can take to stay safe are as follows:
★ Quarantine
○ Take your computer off the network or wifi and reset your data by wiping the device entirely back to its factory settings (the way it came when you bought it) the moment you can confirm there has been a breach.
★ Have a backup
○ You can only take the first measure if you either don’t care at all about your data, or you have bothered to back it up so you have an unencrpted copy.
★ Get help negotiating your ransom down
○ If you need to pay the threat actor the ransom money to recover your data, there are many firms that can help you with this - don’t pay the full price of the ransom! Firms that can help with ransom negotiation and essential protections include CyberSecOp, which you can reach by using Our Contact Form.
So what’s so special about the threat of Linux-based malware? A Linux-based ransomware variant has the potential to take down any and every industry. Major cloud providers like AWS (Amazon Web Services), Oracle, and Microsoft base entire workloads on Linux; malware sweeping through those servers could bring down any company that uses a modernized cloud stack to host their sites and data.
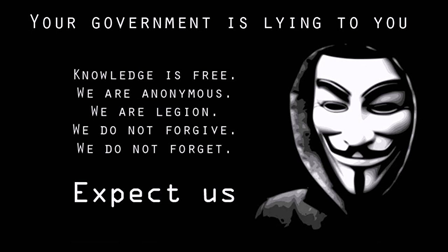
And then there are hacktivists - hackers who hack to do activism for their cause (which can vary greatly in scope between organizations). Hacktivists have a history of using their ransomware attacks to make a point - whether it’s political or personal - and to incite fear in other companies or individuals who support the cause represented by the victim. While you might not think this presents a threat to you personally, or even to your business, the truth is that innovations in cyberattacks threaten us all. If the target were to have a Linux-based system, the hacktivist group targeting that individual would be devoted to finding a way to spread ransomware across Linux-based devices. When ransomware is evolved by perpetrators to this degree, we are likely to see major outages across all the cloud providers listed above, and it could cripple any business or personal account that is hosted therein.
To avoid such a catastrophic and monolithic problem, we should learn to govern our systems from a more ecosystem-centric approach, rather than depend on the classic signature-based antivirus alerts that have become standard. You may recognize Norton Antivirus alerts or even operating-system-based protection like Windows Defender presenting to you pop-ups about updating your signatures.
The truth is that we shouldn’t rely on the technical drivers of these updates, the people who hunt down and publish these known virus signatures, to keep us safe. We should be educating our employees, friends, and families, on the essentials of how to stay digitally secured and prevent breaches in the modern threat landscape. This concept is especially important as a mere tweak in the code of a virus and a quick recompilation of that code can cause the hash (or signature) of the virus to change, causing these famous signature-based antivirus softwares to completely miss the threat on your device.
A phenomenal example of how dangerous this variant-based workaround can be is what happened to the Colorado State Department of Transportation (CDOT) in early 2018.
“As CDOT’s Information Security group scrambled to contain the spread and impact of SamSam’s first wave, their efforts were quickly undermined by another variant of the same ransomware strain that was spreading throughout many of the newly sanitized zones of their network.”[1] (Richard Horne for the SANS Institute)
In an interview with the Denver Post, Brandi Simmons, a spokeswoman for the state's Office of Information Technology said, “The variant of SamSam ransomware just keeps changing. The tools we have in place didn't work. It's ahead of our tools.” The tools in question were signature-tracking antivirus software, like what many of us use on our home computers. In the end, Colorado's Office of Information Technology, the Colorado National Guard, and the FBI all had to collaborate to contain this threat, and by the time they had, over 2,000 computers running Windows and McAfee security software had been taken offline.
In conclusion, it seems inevitable that we will see Linux systems fall prey to the same types of ransomware we currently battle; it’s only a matter of time. Make sure you’re safe and you know how to protect your data: maintain a backup of all your files, be ready to quarantine in the event of a breach, and remember not to panic. We are here to help.
Sources:
https://www.sans.org/reading-room/whitepapers/tools/strings-me-linux-ransomware-39870
https://www.darkreading.com/attacks-breaches/second-ransomware-round-hits-colorado-dot/d/d-id/1331197
Authored by Alison Stuart