CYBER SECURITY CONSULTING SERVICE AWARDS AND RECOGNITIONS
CyberSecOp's comprehensive managed security services, cyber security consulting, professional services, and data protection technology are recognized as industry-leading threat detection and response solutions by major analyst firms, key media outlets, and others.
DNS Security: How Hackers Exploit Your Domain Name System and How MSSPs Stop Them
Every time someone visits your website, sends you an email, or connects to a cloud application, a quiet but critical process takes place behind the scenes. The Domain Name System, DNS, translates the human-readable addresses we type into the numerical addresses that computers use to communicate. It is one of the oldest and most fundamental layers of the internet. It is also one of the most frequently abused by attackers.
DNS was designed decades ago with functionality in mind, not security. The result is a protocol that underpins virtually all internet activity but carries significant inherent vulnerabilities, many of which remain exploitable today. For businesses, a successful DNS attack can redirect customers to fraudulent websites, intercept sensitive communications, take down critical services entirely, or serve as the entry point for a much larger breach. Understanding how these attacks work, and how a Managed Security Services Provider (MSSP) closes the gaps, is essential for any organization that depends on the internet to operate.
How the Domain Name System Works, and Why It's a Target
When a user types a web address into their browser, a DNS resolver queries a series of servers to find the corresponding IP address. This process happens in milliseconds and involves multiple points of trust, each of which represents a potential point of attack. DNS queries are typically transmitted in plain text, responses are cached without robust verification, and the system was built on an assumption of good faith that modern attackers have long since abandoned.
The sheer volume of DNS traffic, and the fact that most organizations monitor it poorly or not at all, makes it an attractive channel for attackers. CyberSecOp's Threat and Vulnerability Assessments consistently identify DNS as one of the most overlooked layers of an organization's attack surface.
Common DNS Attack Techniques
DNS Spoofing and Cache Poisoning
In a DNS cache poisoning attack, an attacker injects fraudulent DNS records into a resolver's cache, causing it to return a malicious IP address in response to legitimate queries. Users who type your company's web address are silently redirected to a fake site, one that may look identical to the real thing, where their credentials, payment data, or sensitive information can be harvested. Because the redirect happens at the DNS layer, users see no warning and have no indication that anything is wrong.
Cache poisoning attacks can affect thousands of users simultaneously and persist for hours or days, depending on how long the fraudulent record remains cached before it expires or is detected.
DNS Tunneling
DNS tunneling exploits the fact that DNS traffic is rarely blocked or deeply inspected by firewalls. Attackers embed data, commands, exfiltrated files, or malware payloads, inside DNS queries and responses, using the protocol as a covert communication channel. An attacker who has already established a foothold inside a network can use DNS tunneling to communicate with external command-and-control infrastructure, bypass data loss prevention controls, and exfiltrate sensitive data without triggering conventional security alerts.
DNS tunneling is particularly difficult to detect because the traffic looks, on the surface, like ordinary DNS activity. Detection requires behavioral analysis and pattern recognition that goes well beyond basic firewall rules.
DNS Hijacking
DNS hijacking attacks modify the DNS records of a legitimate domain, either by compromising the domain registrar account, exploiting vulnerabilities in DNS management platforms, or gaining access to the DNS server itself. Once hijacked, the domain can be pointed at attacker-controlled infrastructure, intercepting all traffic intended for the legitimate destination. Email, web traffic, and API communications can all be rerouted in this way.
In some cases, DNS hijacking is used to obtain fraudulent SSL certificates for the hijacked domain, giving the attacker a site that appears fully legitimate, complete with a padlock icon in the browser. CyberSecOp's Attack Surface Management service monitors for unauthorized changes to DNS records and certificate issuance events that can indicate a hijacking attempt.
Distributed Denial of Service via DNS (DNS DDoS)
DNS amplification is a well-established technique for launching large-scale Distributed Denial of Service attacks. By sending small DNS queries with a spoofed source address, set to the victim's IP, attackers cause DNS servers to send disproportionately large responses to the target, overwhelming its network capacity. DNS servers can amplify traffic by a factor of 70 or more, making them a highly efficient weapon for taking services offline.
For businesses that depend on website availability, customer portals, or cloud-based applications, a successful DNS DDoS attack translates directly to lost revenue, damaged reputation, and in some cases, regulatory exposure.
Domain Generation Algorithms (DGA)
Many modern malware strains use Domain Generation Algorithms to generate large numbers of seemingly random domain names that serve as communication points for command-and-control infrastructure. Because the domains change constantly and are generated algorithmically, traditional blocklists cannot keep up. DGA-based malware can maintain persistent communication channels with attacker infrastructure even as individual domains are identified and blocked.
The Business Impact of DNS Attacks
The consequences of a successful DNS attack extend well beyond temporary inconvenience. Customer data harvested through a spoofed login page carries the same regulatory liability as any other data breach. Business email compromise attacks that begin with DNS hijacking can result in fraudulent wire transfers and irreversible financial losses. Extended service outages from DNS DDoS attacks erode customer trust and violate service level agreements with enterprise clients.
For regulated industries, a DNS-related breach is subject to the same notification requirements and penalties as any other security incident. CyberSecOp's Compliance Security Consulting team helps businesses understand how DNS security intersects with their regulatory obligations under frameworks including HIPAA, PCI-DSS, and NIST.
How an MSSP Strengthens DNS Security
Individual IT teams rarely have the tooling, expertise, or bandwidth to monitor DNS traffic at the depth required to detect modern attacks. An MSSP addresses this gap through a combination of technology, continuous monitoring, and threat intelligence that no single internal team can replicate. CyberSecOp's Managed Security Services deliver DNS protection across several interconnected layers.
DNS Filtering and Protective DNS
DNS filtering blocks queries to known malicious domains before a connection is ever established, preventing malware from communicating with command-and-control servers, blocking access to phishing sites, and stopping DNS tunneling channels at the query level. Protective DNS services apply real-time threat intelligence to every DNS query across your environment, blocking threats that signature-based tools cannot detect.
DNSSEC Implementation
DNS Security Extensions (DNSSEC) add cryptographic signatures to DNS records, allowing resolvers to verify that a response has not been tampered with in transit. DNSSEC implementation requires careful configuration and ongoing maintenance, tasks that are frequently deferred or misconfigured without expert oversight. CyberSecOp manages DNSSEC deployment and validation as part of a comprehensive DNS hardening program.
Continuous DNS Traffic Monitoring
Through CyberSecOp's Security Operations Center, DNS traffic is monitored around the clock for behavioral anomalies, unusual query volumes, queries to algorithmically generated domains, tunneling patterns, and unauthorized record modifications. When suspicious activity is detected, the response team investigates and contains the threat before it can escalate.
Domain Registrar Security and Record Monitoring
Securing the DNS layer means securing the administrative accounts that control it. CyberSecOp's Risk Assessment Services evaluate the security of domain registrar accounts, DNS management platforms, and related credentials, identifying weak points before attackers can exploit them. Record monitoring alerts ensure that any unauthorized change to your DNS configuration triggers an immediate investigation.
Incident Response for DNS Attacks
When a DNS attack occurs, whether a cache poisoning event, a hijacking incident, or a DDoS campaign, rapid response is critical. Every minute that fraudulent DNS records remain active is another minute that customers are being redirected to attacker infrastructure. CyberSecOp's Incident Response Services provide immediate containment, forensic investigation, and restoration of legitimate DNS records, minimizing exposure and accelerating recovery.
DNS Security Is Not Optional
DNS is the foundation on which every online interaction your business conducts is built. Leaving it unmonitored and unprotected is the equivalent of leaving the front door open while investing heavily in interior locks. Attackers know this, and they exploit DNS precisely because so many organizations treat it as infrastructure rather than a security priority.
A Cybersecurity Assessment from CyberSecOp will evaluate your current DNS security posture, identify gaps in monitoring and configuration, and provide a prioritized roadmap for hardening this critical layer of your environment. Contact us at cybersecop.com/contact to get started.
The Role of MSSPs in Securing Cryptocurrency and Blockchain Networks
Blockchain technology promised something the financial world had rarely achieved: a transaction record that is transparent, immutable, and resistant to manipulation. For many applications, it has delivered on that promise. But the broader cryptocurrency ecosystem built on top of blockchain infrastructure has proven far more vulnerable than early proponents anticipated, not because the underlying cryptography is weak, but because the platforms, protocols, and human behavior surrounding it are not.
Cryptocurrency-related fraud, theft, and infrastructure attacks have resulted in billions of dollars in losses annually. Exchanges have been drained, smart contracts have been exploited, and private keys have been stolen through phishing attacks that would look familiar to any corporate security team. As businesses increasingly explore blockchain-based payment systems, digital asset custody, and decentralized finance applications, the question of how to secure these environments has moved from niche to urgent. A Managed Security Services Provider (MSSP) with expertise in emerging technology threats plays a critical role in helping organizations navigate this landscape safely.
Understanding the Blockchain Security Paradox
The blockchain itself, the distributed ledger that records transactions across a network of nodes, is exceptionally difficult to attack directly. Altering a confirmed transaction would require controlling more than half of the network's computing power, a feat that is economically prohibitive on major networks. This security property is genuine and meaningful.
The paradox is that almost everything surrounding the blockchain is far less secure than the blockchain itself. The wallets that hold private keys, the exchanges that facilitate trading, the smart contracts that automate transactions, the bridges that connect different blockchain networks, and the human operators who manage all of these components are all subject to conventional security vulnerabilities, and they are being exploited at scale.
How Attackers Target Cryptocurrency and Blockchain Environments
Private Key Theft and Wallet Compromise
Cryptocurrency ownership is, at its core, possession of a private key. Whoever controls the private key controls the assets, and unlike a stolen password, a stolen private key cannot be reset or revoked. Attackers pursue private keys through phishing campaigns, malware that scans for wallet files, fake wallet applications, and social engineering attacks targeting individuals with access to high-value wallets.
For businesses managing cryptocurrency reserves or offering digital asset services to clients, private key security is an existential concern. A single successful key theft can result in irreversible, unrecoverable loss.
Smart Contract Exploitation
Smart contracts are self-executing programs that run on blockchain networks, automating transactions, and enforcing agreement terms without intermediaries. They are also code, and code contains bugs. Unlike traditional software, where a discovered vulnerability can be patched, a deployed smart contract often cannot be modified. An exploited vulnerability remains exploitable until the contract is deprecated, or funds are drained.
The history of decentralized finance is marked by smart contract exploits that have resulted in losses ranging from millions to billions of dollars. These attacks often exploit logical flaws in contract design, reentrancy vulnerabilities, integer overflows, or flawed access controls, that a thorough security assessment would identify before deployment.
Exchange and Custodial Platform Attacks
Centralized cryptocurrency exchanges are high-value targets that combine large asset concentrations with the security challenges of any complex web platform. SQL injection, authentication bypass, API vulnerabilities, and insider threats have all been used to compromise exchanges. When an exchange is breached, customer funds held in hot wallets, those connected to the internet for operational purposes, are typically the first to be drained.
Even exchanges with strong security controls face persistent threats from sophisticated, well-funded threat actors who treat large platform attacks as long-term investment opportunities, conducting reconnaissance over months before executing an attack.
Blockchain Bridge Attacks
Cross-chain bridges, protocols that allow assets to be transferred between different blockchain networks, have emerged as one of the most frequently exploited components of the cryptocurrency ecosystem. Bridges hold large asset reserves and often involve complex smart contract logic that creates multiple potential attack surfaces. Several of the largest cryptocurrency thefts in recent years have targeted bridge protocols, with losses in the hundreds of millions of dollars per incident.
Cryptojacking
Cryptojacking attacks compromise business systems, servers, workstations, cloud infrastructure, and use their computing resources to mine cryptocurrency for the attacker's benefit. Unlike ransomware, cryptojacking is designed to remain undetected as long as possible, silently consuming resources and electricity while degrading system performance. For businesses operating cloud infrastructure, unauthorized crypto mining can result in significant unexpected costs before the intrusion is discovered.
CyberSecOp's Security Operations Center monitors for the behavioral signatures of cryptojacking, anomalous CPU usage, unusual outbound connections, and process behavior inconsistent with normal operations, enabling rapid detection and response.
Crypto-Specific Phishing and Social Engineering
The cryptocurrency space has spawned a distinct class of phishing attacks targeting both individual holders and organizational staff. Fake wallet interfaces, fraudulent airdrop offers, impersonated exchange support personnel, and SIM swapping attacks that defeat SMS-based two-factor authentication are all routinely used to steal credentials and assets. For businesses, business email compromise schemes that redirect cryptocurrency payments to attacker-controlled wallets represent a growing and difficult-to-reverse fraud category.
Regulatory and Compliance Dimensions
The regulatory landscape for cryptocurrency is evolving rapidly, with financial regulators in the United States and globally introducing new requirements for digital asset businesses around anti-money laundering (AML), know-your-customer (KYC), and cybersecurity controls. Businesses operating in this space face compliance obligations that are both novel and stringent. CyberSecOp's Compliance Security Consulting team helps digital asset businesses understand and satisfy these requirements, building compliance frameworks that can adapt as the regulatory environment continues to develop.
How an MSSP Secures Blockchain and Cryptocurrency Environments
Smart Contract Security Auditing
Before a smart contract is deployed to a production blockchain network, it should be subjected to rigorous security review, examining the code for logical flaws, known vulnerability patterns, and edge cases that could be exploited under adversarial conditions. CyberSecOp's application security practice applies formal auditing methodology to smart contract code, providing the kind of independent review that Threat and Vulnerability Assessments deliver for conventional software.
Private Key and Wallet Security Architecture
An MSSP with blockchain security expertise helps organizations design and implement key management architectures that minimize exposure, including hardware security modules (HSMs) for key storage, multi-signature approval workflows that prevent single-point-of-failure key compromise, and cold storage strategies for assets that do not require frequent access. These controls are complemented by strict access management policies that govern who can initiate transactions and under what conditions.
Exchange and Platform Penetration Testing
For businesses operating cryptocurrency platforms, regular penetration testing is essential for identifying vulnerabilities before attackers do. CyberSecOp's penetration testing services simulate the techniques used by real-world attackers against web applications, APIs, and network infrastructure, providing actionable findings that development and security teams can use to harden the platform before it is exploited.
Continuous Monitoring and Threat Detection
Blockchain transactions are publicly visible and permanently recorded, a unique property that creates opportunities for proactive threat detection. By monitoring on-chain activity for patterns consistent with known attack techniques, an MSSP can identify suspicious transaction flows, flag anomalous smart contract interactions, and detect unauthorized fund movements in real time. Combined with conventional network and endpoint monitoring through CyberSecOp's managed detection and response capabilities, this creates a comprehensive threat detection layer across both the blockchain and traditional infrastructure components of a crypto business.
Incident Response for Crypto-Specific Threats
The irreversibility of blockchain transactions makes incident response in this domain uniquely challenging. When cryptocurrency is stolen, it cannot be recalled. The priority of an incident response engagement is therefore to contain the breach, preventing further theft, preserving evidence for forensic investigation, and coordinating with exchanges to flag and potentially freeze stolen assets in transit. CyberSecOp's Incident Response Services are structured to address the specific requirements of cryptocurrency and digital asset incidents, including engagement with blockchain analytics platforms and law enforcement coordination where applicable.
Third-Party and Vendor Risk in the Crypto Ecosystem
Cryptocurrency businesses rely heavily on third-party infrastructure, blockchain node providers, oracle services, DeFi protocol integrations, and custodial partners. Each of these relationships introduces risk that must be assessed and managed. CyberSecOp's Third Party Risk Management service evaluates the security posture of third-party dependencies, ensuring that a weakness in a partner's environment cannot become a pathway into yours.
A Maturing Threat Landscape Demands Professional Security
The cryptocurrency and blockchain space is no longer a fringe technology sector occupied by early adopters. It is a multi-trillion-dollar asset class that institutional investors, payment processors, financial institutions, and enterprises are engaging with directly. The security standards applied to these environments must reflect that reality.
Attackers in this space are sophisticated, well-resourced, and highly motivated. The combination of irreversible transactions, pseudonymous ownership, and the novelty of the technology creates an environment where security shortcuts carry catastrophic consequences.
An MSSP brings the structure, expertise, and continuous oversight that this environment demands. Begin with a Cybersecurity Assessment to evaluate your current posture across both traditional and blockchain-specific risk dimensions. Contact CyberSecOp at cybersecop.com/contact to speak with a member of our team.
AI-Powered Chatbot Attacks: How Hackers Are Weaponizing AI Assistants
For most of the history of cybercrime, the limiting factor was scale. A skilled attacker could craft a convincing phishing email, but sending thousands of personalized, contextually appropriate versions of it required either automation that sacrificed quality or a team that sacrificed efficiency. Generative AI has changed that calculus entirely, and the implications for every organization's security posture are significant.
AI-powered chatbots and large language models are being used by businesses to improve customer service, accelerate content production, and streamline internal workflows. The same capabilities are being used by attackers to industrialize social engineering, automate vulnerability discovery, generate malware, and conduct fraud at a scale and sophistication that was not previously achievable. Understanding how attackers are weaponizing AI, and how a managed security program responds, is now a baseline requirement for security leadership.
The Threat Is Not Hypothetical
AI-generated phishing campaigns, deepfake audio used to impersonate executives in wire transfer fraud, and chatbot-driven credential harvesting attacks are all documented, active threats, not theoretical future risks. CyberSecOp's Security Operations Center tracks these emerging attack patterns as part of continuous threat intelligence operations, and the volume and sophistication of AI-assisted attacks has grown substantially over the past two years.
For businesses, the key challenge is that many existing security controls were designed for a pre-AI threat landscape. Phishing filters trained to detect grammatical errors and awkward phrasing are far less effective against AI-generated text that is fluent, contextually accurate, and indistinguishable from legitimate communication. Employee training programs that teach staff to spot 'obvious' phishing need to be fundamentally updated.
How Attackers Are Using AI and Chatbots
Hyper-Personalized Phishing at Scale
Traditional spear phishing, highly targeted attacks that incorporate personal details about the victim, has always been more effective than generic phishing but far more labor-intensive to execute. Generative AI eliminates that constraint. By feeding publicly available information about a target, LinkedIn profiles, company websites, press releases, social media activity, into a language model, attackers can generate highly personalized phishing emails in seconds, at the volume of bulk campaigns.
These messages reference real projects, use accurate job titles, reflect the recipient's actual professional context, and are written in fluent, professional language. They are significantly harder to identify as fraudulent, and significantly more likely to produce the credential submission, malicious link click, or wire transfer authorization that the attacker is seeking.
Automated Social Engineering via Chatbots
AI chatbots are increasingly being used to conduct real-time social engineering conversations, engaging targets in text or voice interactions that impersonate IT support staff, financial institutions, or trusted vendors. Unlike a static phishing email, an AI-driven chatbot can respond dynamically to the target's questions and objections, maintaining a convincing cover story across an extended conversation.
In some documented cases, attackers have deployed chatbots that initiate contact through legitimate-seeming customer support channels, collect verification information, and then use that information to bypass authentication controls at the actual institution being impersonated.
AI-Generated Malware and Exploit Code
Generative AI lowers the technical barrier for malware development. Code that previously required specialized expertise can now be generated, modified, and obfuscated with the assistance of AI tools, including commercially available models that have been jailbroken to bypass content restrictions. Attackers are using AI to produce malware variants that evade signature-based detection, generate novel exploit code for known vulnerabilities, and accelerate the development of attack tooling.
This has real implications for the speed of the threat landscape. The window between vulnerability disclosure and widespread exploitation is already shrinking. AI-assisted exploit development compresses it further. CyberSecOp's Vulnerability Management Service maintains continuous scanning and prioritized remediation workflows precisely because the time available to patch before exploitation is no longer measured in weeks.
Deepfake Audio and Video in Business Email Compromise
Business Email Compromise (BEC) fraud, in which attackers impersonate executives or financial officers to authorize fraudulent transactions, has been one of the most financially damaging forms of cybercrime for years. AI has introduced a new dimension to these attacks: deepfake audio and video that allows attackers to convincingly impersonate a CEO's voice or appearance in a phone call or video conference.
Reported cases include employees receiving audio calls from what they believed was their CEO, authorizing emergency wire transfers to attacker-controlled accounts. The audio was AI-generated using publicly available recordings of the real executive's voice. These attacks bypass the intuitive human check of 'I recognize this person's voice', historically one of the last lines of defense against telephone fraud.
Prompt Injection and Chatbot Manipulation
Organizations that deploy AI chatbots, for customer service, internal helpdesk, or productivity applications, face a distinct attack category: prompt injection. In a prompt injection attack, a malicious user crafts inputs designed to override the chatbot's instructions, bypassing safety guardrails, extracting confidential information from the model's context, or causing the bot to perform actions outside its intended scope.
For businesses that have integrated AI assistants with internal systems, databases, email platforms, CRM tools, a successful prompt injection can potentially expose sensitive data or trigger unauthorized actions within connected systems. As enterprise AI deployments expand in scope and integration depth, this attack surface grows proportionally.
AI-Powered Credential Stuffing and Account Takeover
Credential stuffing, using lists of stolen username and password combinations to gain unauthorized access to accounts, is not new. AI makes it significantly more effective by enabling adaptive attack strategies that adjust request timing, rotate user agents, and solve CAPTCHA challenges at scale. AI-driven credential stuffing tools can also intelligently prioritize credential lists, targeting the combinations most likely to succeed against specific platforms based on breach data analysis.
The Compounding Effect on the Human Layer
The most significant impact of AI-powered attacks is on the human element of security. Employees who are trained to spot phishing are trained to recognize patterns that AI increasingly masks. The grammatical errors, generic greetings, and implausible requests that characterized earlier phishing attempts are disappearing from AI-generated attacks. CyberSecOp's Security Awareness Training programs have been updated to address this shift, teaching employees to apply process-based verification rather than relying on textual cues that AI can now replicate convincingly.
This means verifying requests through secondary channels regardless of how legitimate they appear, applying strict authorization workflows for financial transactions and data access requests, and understanding that a well-written, contextually appropriate message is no longer evidence of legitimacy.
How MSSPs Respond to AI-Powered Threats
AI-Enhanced Threat Detection
Defending against AI-powered attacks increasingly requires AI-powered defenses. Behavioral analytics platforms that establish baseline patterns of user activity, and flag deviations consistent with account takeover, insider threat, or social engineering success, are far more effective against AI-generated threats than signature-based tools. An MSSP operates these platforms continuously, with analysts investigating and responding to alerts in real time.
Advanced Email Security and Anti-Phishing Controls
Modern email security platforms use machine learning to detect phishing attempts based on behavioral signals, sender reputation, content analysis, and link inspection, not just keyword matching. Deployed and managed as part of CyberSecOp's Managed Security Services, these controls are continuously tuned against the current threat landscape, including AI-generated content patterns that simpler filters miss.
Zero Trust and Strict Authorization Controls
The most effective structural defense against social engineering, AI-powered or otherwise, is reducing how much an attacker can accomplish even after successfully deceiving a human target. Zero Trust architecture limits lateral movement, enforces continuous authentication, and applies least-privilege access controls that contain the damage from a compromised account. When an employee is deceived into disclosing credentials, Zero Trust controls limit what those credentials can unlock.
Dark Web Monitoring for AI-Generated Fraud Signals
Criminal forums and dark web marketplaces are where AI-powered attack tools are developed, sold, and discussed. CyberSecOp's Dark Web Monitoring service tracks these sources for mentions of client organizations, exposed credentials, and emerging attack tooling, providing early warning of threats that have not yet been deployed.
Incident Response for AI-Assisted Attacks
When an AI-powered attack succeeds, a deepfake-assisted BEC fraud, a chatbot-driven credential harvest, or an AI-generated malware infection, the response requires both speed and forensic rigor. CyberSecOp's Incident Response Services are structured to address the specific characteristics of these attacks, including the challenge of distinguishing AI-generated artifacts from legitimate communications during forensic analysis.
vCISO-Level Strategic Oversight
The rapid evolution of AI-powered threats requires security strategy that keeps pace. CyberSecOp's Virtual CISO Program provides the ongoing strategic leadership to ensure that security programs, policies, and controls are updated in response to the changing threat landscape, not just after an incident forces the issue.
The Threat Will Continue to Evolve
Generative AI is improving rapidly, and the attack techniques enabled by it are evolving in parallel. The deepfakes of today are more convincing than those of last year. The phishing emails being generated now are more contextually accurate than those generated six months ago. Organizations that treat AI-powered threats as a future concern rather than a present reality are already behind.
A Cybersecurity Assessment from CyberSecOp will evaluate your organization's readiness for AI-powered threats across technical controls, employee awareness, and incident response capabilities. Contact us at cybersecop.com/contact to schedule a consultation with our team.
Why SMBs Should Use Virtual CISO (vCISO) Services from an MSSP
Small and mid-sized businesses face the same cyber threats as large enterprises — but rarely have the budget, headcount, or expertise to match. A Virtual Chief Information Security Officer (vCISO), delivered through a Managed Security Services Provider (MSSP), offers a practical and cost-effective path to enterprise-grade security leadership.
The Security Leadership Gap in Small Business
Cybersecurity is no longer a concern reserved for Fortune 500 companies. Today's threat landscape is indiscriminate — ransomware, phishing campaigns, supply chain attacks, and data breaches hit businesses of every size. According to industry research, 43% of cyberattacks target small businesses, and 60% of those businesses close within six months of a serious breach.
Yet for most SMBs, the question isn't whether to take security seriously. It's how to do so without the budget for a full-time C-suite security executive. Hiring a Chief Information Security Officer costs $180,000–$280,000 per year in salary alone, before benefits, bonuses, and the months-long hiring process. That's simply out of reach for most growing businesses.
This is where the vCISO model — delivered through an MSSP like CyberSecOp — becomes one of the most impactful decisions an SMB can make.
What Is a vCISO?
A Virtual Chief Information Security Officer is an experienced security executive who provides strategic leadership, program management, and compliance oversight on a fractional or on-demand basis. Unlike a full-time hire, a vCISO is available when you need them — scaling up during audits, incidents, or rapid growth phases, and scaling back during quieter periods.
Through CyberSecOp's Virtual CISO / vCISO Advisory Program, organizations receive a dedicated security leader who takes ownership of their security strategy without the overhead of a permanent executive headcount.
What a vCISO Does for Your Business
The decisions made in the early and mid-growth stages of a business — about data handling, vendor risk, access controls, and incident response — set the security posture for years to come. A vCISO takes responsibility for those decisions. Core responsibilities include:
Security program development: Building and maturing your security policies, procedures, and governance framework from the ground up — creating a program that grows with your business.
Risk assessment and management: Identifying your most critical assets and vulnerabilities through structured risk assessments, then prioritizing remediation based on business impact.
Regulatory compliance guidance: Navigating frameworks including HIPAA, PCI-DSS, SOC 2, CMMC, and NIST — managing documentation, control implementation, and audit readiness.
Incident response planning: Ensuring your business has a tested, documented plan before a breach — not scrambling to create one during an active incident.
Board and executive reporting: Translating technical risk into business language that leadership can act on, supporting informed decision-making at every level.
Vendor and third-party risk: Assessing the security posture of vendors, partners, and suppliers who access your data or systems.
Security awareness program oversight: Coordinating employee training programs that address the human element — the most common entry point for attackers.
In-House CISO vs. vCISO: The Real Comparison
For most SMBs, the idea of a full-time CISO sounds appealing in theory. In practice, the cost and operational overhead make it nearly impossible. Here is what the comparison looks like across the factors that matter most:
Annual cost: In-house: $180,000–$280,000+ in salary, benefits, and bonuses. vCISO: Fraction of the cost, scales with your needs.
Time to onboard: In-house: 3–6 month hiring cycle on average. vCISO: Operational within days to weeks.
Breadth of expertise: In-house: One individual's background and experience. vCISO: Entire MSSP team with cross-industry depth.
24/7 coverage: In-house: Rarely available outside business hours. vCISO: Yes, through integrated SOC monitoring.
Compliance knowledge: In-house: Varies significantly by candidate. vCISO: Multi-framework expertise built into the program.
Scalability: In-house: Limited by a single hire. vCISO: Scales up or down with business needs.
Continuity risk: In-house: High — departure creates an immediate gap. vCISO: Low — institutional knowledge is retained.
Why an MSSP-Backed vCISO Multiplies the Value
A standalone vCISO engagement gives you strategic leadership. A vCISO embedded within a full-service MSSP like CyberSecOp gives you something more powerful: an integrated security ecosystem.
Your vCISO has immediate access to threat intelligence, active monitoring capabilities, forensic investigation resources, and a team of practitioners who can execute the strategy they design. When a threat materializes at 2 a.m., the response isn't dependent on one person picking up a phone. It's backed by CyberSecOp's Incident Response Services and a dedicated Security Operations Center providing continuous monitoring and rapid containment.
When your vCISO is part of a broader MSSP structure, they seamlessly coordinate services like Vulnerability Assessments, Dark Web Monitoring, and Attack Surface Management — ensuring the security strategy is not just documented but actively enforced across your environment.
Compliance Without a Full-Time Hire
Regulatory compliance is one of the most common triggers for SMBs seeking vCISO support. Whether you're preparing for a SOC 2 audit, working toward CMMC certification for government contracts, or maintaining information security compliance standards, the documentation, evidence collection, and control implementation involved is substantial.
A vCISO through CyberSecOp takes ownership of that process — coordinating with your legal, IT, and operations teams to ensure security controls are implemented, tested, and documented in a way that survives an audit. They also advise on cyber liability insurance requirements, helping you qualify for coverage and negotiate better premiums by demonstrating a mature security posture.
Industry-Specific Security Leadership
Cybersecurity requirements for a healthcare organization subject to HIPAA look nothing like those for a law firm navigating client confidentiality or a financial services firm under SEC scrutiny. One of the strongest advantages of CyberSecOp's vCISO model is the depth of industry-specific expertise it brings to every engagement.
CyberSecOp's vCISO advisors bring vertical knowledge across sectors including Healthcare, Financial Services, Legal and Law Firms, Technology Companies, and Government Contractors. Each vertical carries distinct compliance frameworks, breach notification timelines, and threat profiles that a generalist security advisor simply cannot match.
Security Technology Stack Guidance
How a vCISO helps SMBs make smarter decisions about which security tools to buy, avoid, and retire, preventing the common trap of overspending on redundant tools or underinvesting in critical gaps. An in-house CISO may have vendor biases or limited exposure; an MSSP-backed vCISO brings cross-client visibility into what actually works.
Is a vCISO Right for Your Business?
A vCISO engagement deserves serious consideration if your organization recognizes any of the following situations:
You are subject to regulatory compliance requirements but lack dedicated security staff to manage them.
You have experienced a security incident — or near-miss — and need to understand your exposure and build a stronger defensive posture.
You are preparing for rapid growth, a merger, or a new enterprise client relationship that requires demonstrated security controls.
You have an IT team handling security reactively and need someone to build a proactive, strategic program.
You need to present a credible security posture to board members, investors, or insurance underwriters.
You are pursuing government contracts that require CMMC or other federal compliance certifications.
CyberSecOp's Cybersecurity Assessment Services are often the natural starting point — establishing your current security state before a vCISO engagement defines the roadmap forward. A Risk Assessment gives you and your vCISO a clear picture of where you stand, what is at risk, and where to focus first.
The Bottom Line
The cyber threat landscape does not distinguish between large corporations and small businesses. Attackers go where the vulnerabilities are — and SMBs without dedicated security leadership are disproportionately exposed.
A vCISO through CyberSecOp closes that gap. You get the strategic leadership of an experienced CISO, backed by a full MSSP infrastructure — at a fraction of the cost of a full-time hire, available from day one, and scaled precisely to your needs.
To learn more or schedule a consultation, visit cybersecop.com/contact or explore our full cybersecurity consulting services.
The Hidden Dangers of Public Wi-Fi: How MSSPs Protect Traveling Employees
Your employee lands at an airport, opens their laptop, and connects to the free Wi-Fi to check their email before boarding. In that moment — before they've even ordered a coffee — they may have handed an attacker everything needed to compromise your business.
Public Wi-Fi is one of the most consistently underestimated risks in corporate security. It is available everywhere business happens — airports, hotels, conference centers, coffee shops, co-working spaces — and it is used without hesitation by millions of employees every day. What most of those employees don't realize is that the network they just joined may be monitored, manipulated, or outright fake.
For businesses with traveling staff, remote workers, or a distributed workforce, securing connectivity outside the office is not optional. It is a core component of any responsible security program — and it is an area where a Managed Security Services Provider (MSSP) delivers protection that individual employees simply cannot replicate on their own.
What Makes Public Wi-Fi So Dangerous
The fundamental problem with public Wi-Fi is that it is, by design, open. Unlike a corporate network with access controls, authentication requirements, and monitoring, a public network offers no guarantees about who else is connected or what they are doing. Several specific attack techniques make these networks particularly hazardous for business use.
Man-in-the-Middle Attacks
In a man-in-the-middle (MitM) attack, a threat actor positions themselves between the employee's device and the network — invisibly intercepting all traffic that passes between them. Login credentials, session tokens, email content, and file transfers all pass through the attacker's hands before reaching their destination. The employee sees nothing unusual; the attack leaves no immediate trace.
MitM attacks are particularly effective on unencrypted connections, but even HTTPS traffic can be targeted through SSL stripping techniques that downgrade secure connections without the user's awareness.
Evil Twin Networks
An evil twin is a rogue access point that mimics a legitimate network. An attacker sets up a hotspot with a name nearly identical to the hotel or airport Wi-Fi — "Hilton_Guest" instead of "HiltonGuest," for example — and waits for devices to connect automatically. Once connected, all traffic flows through the attacker's equipment.
Many devices are configured to automatically reconnect to previously used networks. An evil twin that matches a saved network name can capture a device's connection without any action from the user at all.
Packet Sniffing
On an unencrypted or poorly secured network, it is trivially easy to capture the raw data packets being transmitted by other users. With freely available tools, an attacker can reconstruct web sessions, read form submissions, and extract authentication tokens — all without interacting directly with the target device. For employees accessing internal systems, client portals, or cloud applications over public Wi-Fi, the exposure is significant.
Session Hijacking
After an employee authenticates to a web application, their session is maintained through a token stored in the browser. If an attacker captures that token over an unsecured network, they can use it to impersonate the authenticated user — accessing the same application, with the same permissions, without ever needing the password. Session hijacking is particularly dangerous for cloud-based business tools, CRM platforms, and financial applications.
Malware Distribution
Public networks can also serve as a vector for malware delivery. Attackers who control a network can inject malicious code into unencrypted web traffic, redirecting software update prompts to deliver malware instead. A traveling employee who accepts what appears to be a routine software update on public Wi-Fi may be installing a backdoor into your corporate environment.
The Business Risk Is Not Theoretical
The risks described above are not edge cases. They are documented attack techniques used daily against business travelers around the world. A single compromised session can expose client data, grant access to internal systems, or plant malware that lies dormant until the employee returns to the office and connects to the corporate network — bringing the attacker in with them.
For industries subject to regulatory compliance — healthcare, financial services, legal, and government contracting — a breach originating from an unsecured public network carries the same consequences as any other data exposure event. Regulators do not distinguish between a sophisticated intrusion and a preventable connectivity lapse. CyberSecOp's Compliance Security Consulting team works with businesses across regulated industries to ensure that mobile and remote access policies meet the requirements of applicable frameworks.
How an MSSP Protects Employees on the Move
Individual employees cannot be expected to assess the safety of every network they encounter or configure enterprise-grade security controls on their own devices. That responsibility belongs to the organization — and the most effective way to fulfill it is through a managed security program that extends protection wherever employees go.
CyberSecOp's Managed Security Services address the full scope of mobile and remote connectivity risk through a layered set of controls.
Enterprise VPN Deployment and Management
A Virtual Private Network (VPN) creates an encrypted tunnel between the employee's device and the corporate network, rendering intercepted traffic unreadable to anyone on the same public network. An MSSP deploys, configures, and maintains enterprise VPN infrastructure — ensuring that all traffic from traveling employees is encrypted end-to-end, that VPN connections are enforced rather than optional, and that the VPN software itself is kept up to date and free of known vulnerabilities.
Critically, an MSSP also monitors VPN usage. Unusual connection patterns — logins from unexpected geographies, connections at atypical hours, or access to systems outside an employee's normal scope — trigger alerts that can indicate a compromised credential or an active intrusion.
Endpoint Detection and Response (EDR)
Perimeter defenses protect the network boundary, but a traveling employee's laptop operates far beyond that boundary. Endpoint Detection and Response tools deployed on employee devices provide continuous behavioral monitoring — identifying suspicious processes, unauthorized file changes, and malware activity regardless of what network the device is connected to.
Through CyberSecOp's Security Operations Center, EDR alerts are monitored around the clock. When a traveling employee's device exhibits behavior consistent with compromise, the response team can isolate the device, contain the threat, and initiate Incident Response procedures — even while the employee is mid-flight.
Mobile Device Management (MDM)
Mobile Device Management gives organizations centralized control over every corporate device — enforcing encryption, requiring screen lock PINs, managing application permissions, and enabling remote wipe if a device is lost or stolen. An MSSP manages the MDM platform, ensuring policies are enforced consistently across the entire device fleet without placing the configuration burden on individual users or an already-stretched IT team.
MDM is also the mechanism that prevents employees from connecting to unsanctioned networks or installing unauthorized applications that could introduce risk. When combined with a clear acceptable use policy — developed as part of CyberSecOp's Program Management services — MDM enforcement gives organizations both the policy and the technical means to uphold it.
Zero Trust Network Access (ZTNA)
Traditional security models assume that anything inside the network perimeter can be trusted. Zero Trust rejects that assumption entirely — requiring every user, device, and application to verify identity and authorization before accessing any resource, regardless of where the connection originates.
For traveling employees, Zero Trust is particularly powerful. Even if an attacker captures credentials over a public network, they cannot use those credentials to move freely through internal systems. Every access request is evaluated in context — device health, user identity, location, and behavior — before access is granted. CyberSecOp's Network Security practice helps organizations implement Zero Trust architectures that scale with their workforce and risk profile.
Dark Web Monitoring for Exposed Credentials
Credentials compromised over public Wi-Fi don't always get used immediately. Attackers frequently sell or trade stolen credentials on dark web forums, where they may sit for weeks or months before being deployed in a targeted attack. CyberSecOp's Dark Web Monitoring service continuously scans these sources for your organization's email addresses, credentials, and sensitive data — providing early warning that allows you to reset compromised accounts before they are exploited.
Training Employees to Recognize the Risks
Technology controls reduce risk significantly, but they work best when employees understand what they are protecting against. A traveling employee who knows how to recognize a suspicious network, who understands why the VPN must always be active before accessing corporate resources, and who knows what to do if their device behaves unusually is a meaningful layer of defense — not just a liability.
CyberSecOp's Security Awareness Training programs include travel-specific security guidance — covering public Wi-Fi risks, hotel network safety, USB charging port dangers (juice jacking), and the steps employees should take before, during, and after business travel. This training is updated regularly to reflect current attack techniques, so employees are always prepared for the threats they will actually encounter.
Industries with the Highest Exposure
While every business with traveling employees carries public Wi-Fi risk, some industries face compounded exposure due to the nature of the data their employees access on the road.
Financial services: Advisors and bankers accessing client portfolios, trade platforms, and financial records from airports and hotel rooms present significant exposure for firms subject to SEC and FINRA oversight.
Healthcare: Clinicians and healthcare executives accessing patient records remotely must maintain HIPAA compliance regardless of where the connection originates — a standard that public Wi-Fi fundamentally cannot support without proper controls.
Legal and law firms: Attorneys traveling to depositions, court appearances, or client meetings carry privileged communications and case materials on devices that are constantly at risk on public networks.
Technology companies: Engineers and product teams accessing source code repositories, development environments, and proprietary systems while traveling represent a high-value target for corporate espionage and competitive intelligence gathering.
Government contractors: Employees working on federal contracts are often bound by strict data handling requirements that explicitly prohibit the use of unsecured networks without VPN or equivalent protection.
The Road Is Part of Your Attack Surface
Your security perimeter no longer ends at the office door. Every employee who connects to a public network from a conference, a client site, or an airport departure lounge is an extension of your organization's attack surface — and they deserve the same level of protection as someone sitting at a desk in your headquarters.
CyberSecOp's managed security services provide that protection. From VPN enforcement and endpoint monitoring to zero trust access controls and real-time threat response, we ensure that mobility doesn't come at the cost of security — for businesses of any size, in any industry.
Begin with a Cybersecurity Assessment to evaluate your current remote and mobile security posture, or explore CyberSecOp's full range of consulting services. Reach out at cybersecop.com/contact to speak with a member of our team.
Cyber Hygiene: The Small Changes That Make a Big Impact on Security
Most businesses that experience a cyberattack weren't brought down by a sophisticated nation-state exploit. They were compromised through a reused password, an unpatched application, or an employee who clicked a convincing phishing link. The uncomfortable truth about cybersecurity is that the majority of successful breaches are preventable — not through expensive technology, but through consistent, disciplined habits.
This is what cyber hygiene means: the day-to-day practices and baseline security behaviors that keep systems clean, access controlled, and threats at bay. For businesses working with a Managed Security Services Provider (MSSP), these habits become part of a structured, monitored program — not a checklist that gets forgotten after onboarding.
Why Cyber Hygiene Is the Foundation of Every Security Program
Advanced security tools — threat detection platforms, endpoint protection, SIEM systems — are only as effective as the foundation they sit on. A business running a $50,000 security stack but still using default admin credentials or skipping software patches is not secure. The tools protect the perimeter; hygiene protects the inside.
CyberSecOp's Cybersecurity Assessment Services consistently identify the same preventable gaps across businesses of every size: weak credentials, unmanaged devices, outdated software, and undertrained employees. These are not technical failures — they are behavioral ones. And behavioral failures are exactly what cyber hygiene programs are designed to address.
1. Strong Password Practices and Multi-Factor Authentication
Credential compromise is the single most common entry point for attackers. Reused passwords, weak passwords, and credentials exposed in past data breaches give attackers a direct path into your systems, often without triggering any alarms.
The baseline requirements for every business are straightforward:
Require unique, complex passwords for every system and account — never shared or reused across platforms.
Deploy a password manager so employees aren't tempted to simplify or recycle credentials.
Enable multi-factor authentication (MFA) on every application that supports it, beginning with email, VPN, and any cloud-based platform.
Immediately revoke access for former employees — departing staff with active credentials are one of the most overlooked risks in small business security.
An MSSP helps enforce these controls at scale — auditing account access, flagging dormant credentials, and integrating MFA across your environment as part of ongoing security risk management.
2. Patching and Software Updates
Unpatched software is the low-hanging fruit of the threat landscape. When a vulnerability is disclosed and a patch is released, attackers immediately begin scanning the internet for systems that haven't applied the fix yet. The window between disclosure and exploitation is often measured in hours, not weeks.
Effective patch management means keeping operating systems, applications, firmware, and third-party plugins consistently up to date — not just when something breaks. This extends to every connected device on your network, including routers, printers, and any IoT equipment.
CyberSecOp's Vulnerability Management Service takes the guesswork out of this process — continuously scanning your environment for known vulnerabilities, prioritizing remediation by risk level, and tracking patch status across every asset.
3. Controlling Who Has Access to What
One of the most effective — and most overlooked — security controls is the principle of least privilege: every user, system, and application should have access only to what they need to do their job, and nothing more.
In practice, this means regularly auditing who has access to sensitive systems and data, removing permissions that are no longer needed, and ensuring that administrator accounts are not used for everyday tasks. It also means segmenting your network so that a compromise in one area doesn't grant free movement across your entire environment.
Access control is also a core component of most regulatory compliance frameworks. Whether you're subject to HIPAA, PCI-DSS, or SOC 2, demonstrating that access to sensitive data is restricted, logged, and reviewed is a fundamental audit requirement. CyberSecOp's Compliance Security Consulting team helps businesses build access control frameworks that satisfy both operational and regulatory needs.
4. Backing Up Data — and Testing Those Backups
Ransomware has made data backup one of the most critical cyber hygiene practices a business can maintain. When attackers encrypt your systems and demand payment to restore access, a clean, recent, and tested backup is often the difference between a hours-long recovery and a business-ending event.
The operative word is tested. Many businesses have backups that have never been verified — and discover during an actual incident that the restore process fails, the backup is incomplete, or the data is months out of date. Effective backup hygiene requires:
Automated, frequent backups of all critical data and systems.
Offsite or cloud-based storage that is logically separated from your primary environment — ransomware that reaches your network should not be able to reach your backups.
Regular restore tests to confirm backups are complete, current, and functional.
A documented recovery time objective (RTO) so your team knows exactly what to do and how long recovery should take.
This practice feeds directly into a broader Incident Response strategy. Without reliable backups, even the best incident response plan has limited options.
5. Employee Training and Phishing Awareness
Social engineering — manipulating people rather than exploiting technology — remains the most reliable tool in an attacker's arsenal. Phishing emails, pretexting calls, and fraudulent login pages trick employees into handing over credentials or authorizing fraudulent transactions. No firewall blocks a well-crafted email that an employee chooses to trust.
Building a security-aware workforce is not a one-time training event. It requires regular, relevant education that reflects current attack techniques — because the phishing emails employees see today look very different from those of three years ago. Modern attacks use AI-generated text, impersonate internal executives, and mimic legitimate business processes with alarming accuracy.
CyberSecOp's Security Awareness Training programs go beyond checkbox compliance. They use simulated phishing campaigns, real-world scenario training, and role-specific education to build genuine awareness — and to identify which employees need additional coaching before attackers find them first.
6. Monitoring Your Attack Surface and Dark Web Exposure
Cyber hygiene isn't only about protecting what you can see. Every business has an attack surface that extends beyond its own network — including employee credentials leaked in third-party data breaches, domain spoofing, exposed cloud storage buckets, and forgotten subdomains running outdated software.
CyberSecOp's Attack Surface Management service continuously maps your external-facing assets, identifying exposure before attackers can exploit it. Paired with Dark Web Monitoring, which scans criminal forums and leaked credential databases for your business's data, this gives organizations visibility into threats that traditional security tools simply cannot detect.
7. Managing Third-Party and Vendor Risk
Your security posture is only as strong as the weakest link in your supply chain. Third-party vendors, SaaS platforms, IT providers, and contractors who have access to your systems or data introduce risk that many SMBs fail to account for. Some of the most damaging breaches in recent years originated not from a direct attack on the target, but through a compromised vendor.
Good cyber hygiene at the organizational level means asking the right questions before granting any third party access: What security controls do they have in place? How do they handle a breach involving your data? Have they been independently audited? CyberSecOp's Third Party Risk Management service formalizes this process — giving businesses a structured way to evaluate, monitor, and manage vendor risk on an ongoing basis.
How an MSSP Turns Hygiene Into a Managed Program
Knowing what good cyber hygiene looks like is the easy part. Sustaining it — across a growing team, an expanding technology stack, and an evolving threat landscape — is where most businesses struggle without professional support.
An MSSP doesn't just advise on best practices. It operationalizes them. Through CyberSecOp's Managed Security Services, businesses get continuous monitoring, automated vulnerability scanning, patch tracking, access review workflows, and security awareness program management — all coordinated through a single provider with deep expertise across every layer of your environment.
For businesses that want strategic oversight layered on top of operational execution, CyberSecOp's Virtual CISO (vCISO) Program ensures that hygiene practices are part of a coherent, documented security program — with clear ownership, regular review, and measurable improvement over time.
Small Changes, Serious Results
Cyber hygiene is not glamorous. It doesn't involve cutting-edge AI or zero-day exploits. But it is the single most reliable way to reduce your organization's risk profile — and it is the first thing any experienced security professional will evaluate when they assess your environment.
Businesses that practice consistent cyber hygiene are harder to attack, faster to recover, and far better positioned to pass compliance audits, qualify for cyber insurance, and earn the trust of the enterprise clients and partners they want to serve.
Start with a Cybersecurity Assessment to understand where your hygiene gaps are today. From there, CyberSecOp's team can build a practical, prioritized roadmap that turns good intentions into lasting security habits. Contact us at cybersecop.com/contact to get started.
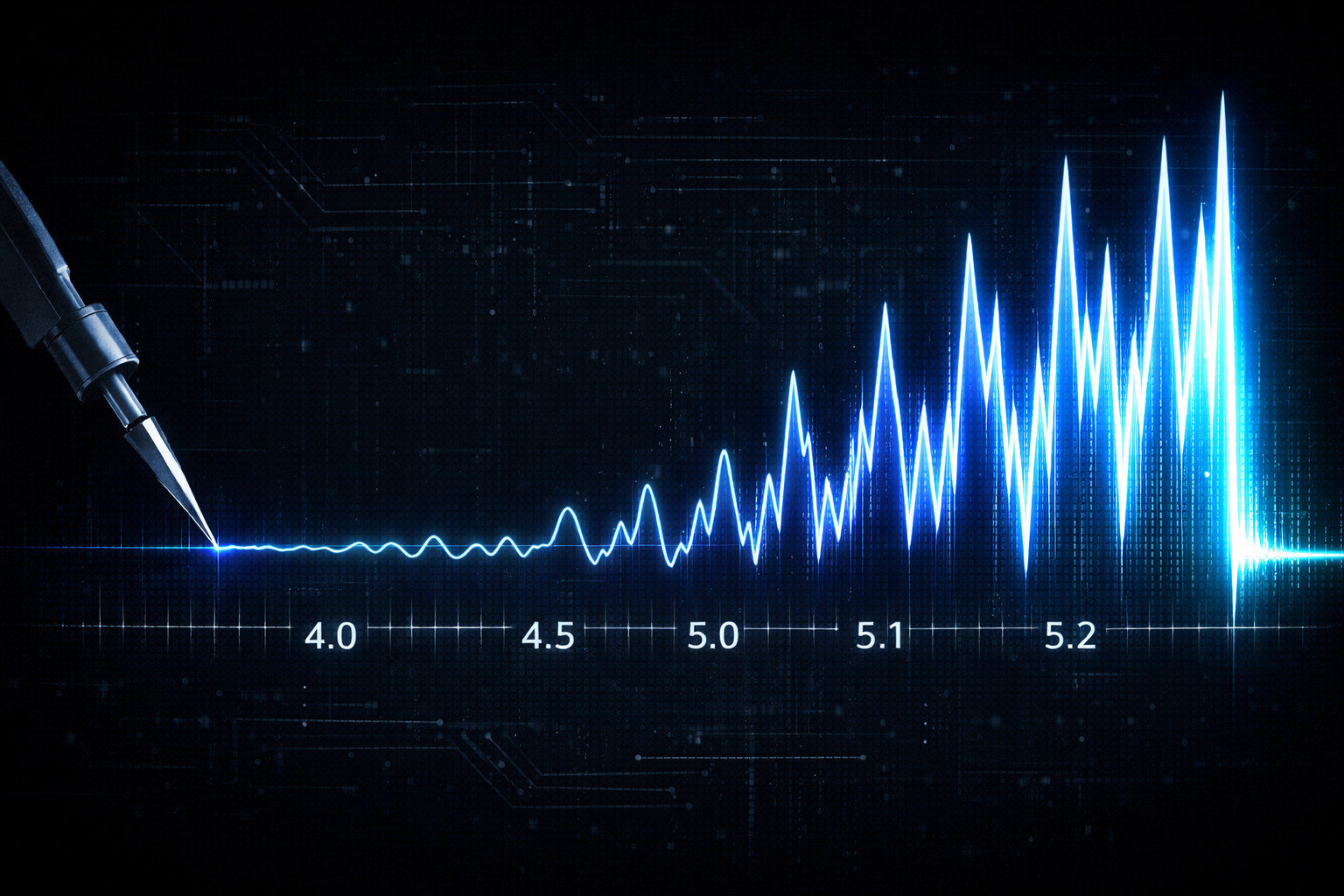
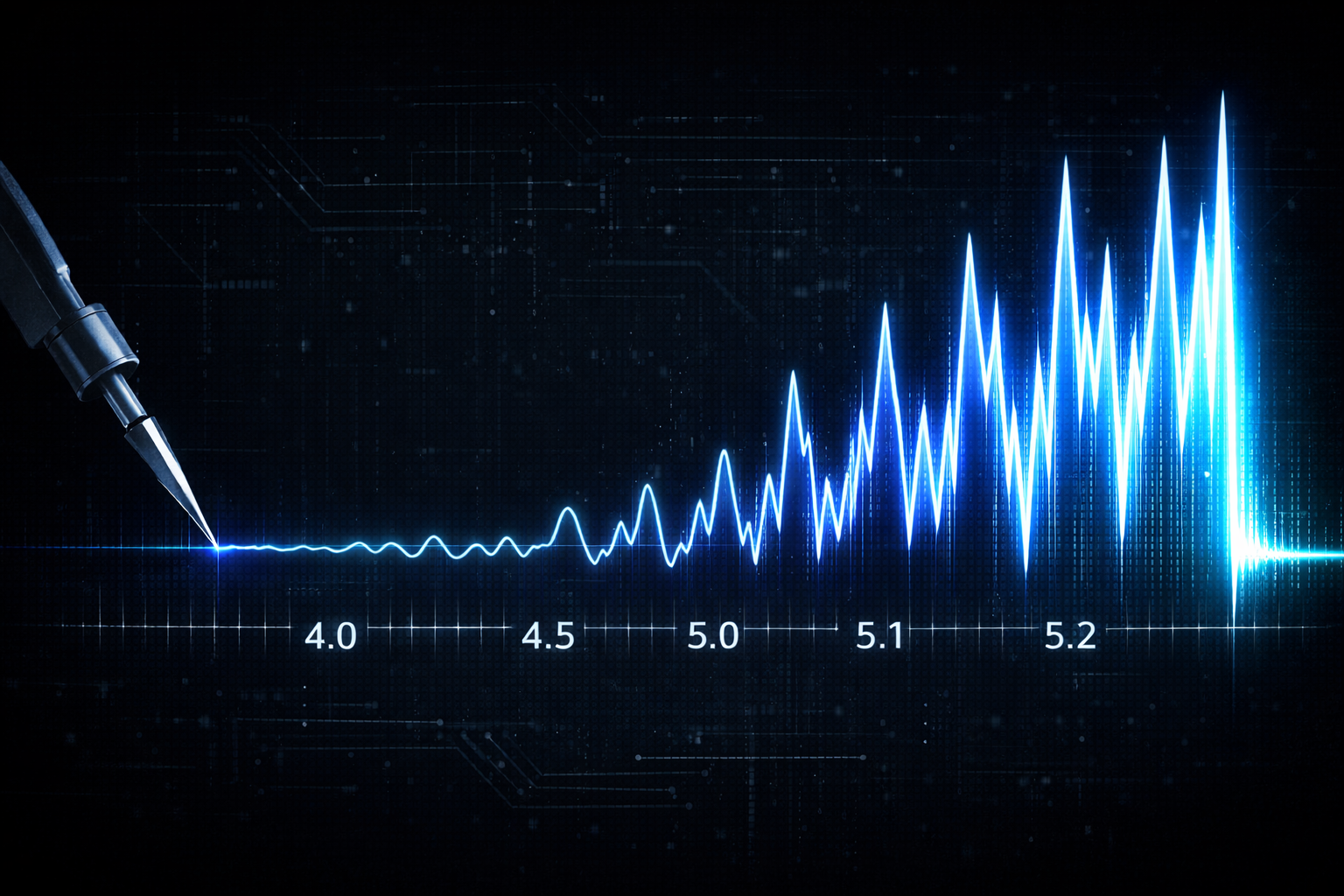
The Richter Scale of AI
When a 5.0 earthquake hits, it rattles windows. A 5.1 doesn't just rattle a little more. It releases significantly more energy. That's how logarithmic scales work. Small numbers, massive differences.
AI is following the same pattern.
Anthropic recently moved from Claude Opus 4.5 to Opus 4.6. A decimal point. On paper, it looks incremental. In practice, the leap in reasoning, contextual awareness, and agentic capability was anything but minor. And they're not alone. OpenAI's jump from GPT-4 to GPT-4o to o1 brought similar step-changes in capability. Google's Gemini models have followed the same trajectory. Meta's open-source LLaMA family keeps closing the gap with each release. Across the board, what looks like a version bump is often a generational shift in what these systems can actually do.
Here's why this matters for security and technology leaders:
The AI risk assessment you completed six months ago? It may already be outdated. The vendor questionnaire you sent last quarter about AI usage in your supply chain? The answers have likely changed. The policies you wrote to govern acceptable use of AI tools? They were written for a less capable technology.
We're not on a linear curve. We're on a logarithmic one. And just like seismologists learned to respect the difference between a 6.0 and a 7.0, technology leaders need to respect the difference between "that's a neat tool" and "that just replaced a workflow."
The organizations that treat AI governance as a one-time project will be the ones caught off guard. The ones that build adaptive frameworks, with regular reassessment cycles and flexible policies, will be the ones still standing when the next decimal point drops.
A small number on the scale. A seismic shift underneath.
#Cybersecurity #AI #ArtificialIntelligence #CISO #GRC #RiskManagement #vCISO
Credential Stuffing Attacks: Why Passwords Alone Are No Longer Safe
Credential stuffing attacks represent industrialized account takeover warfare, with attackers launching 193+ billion attempts annually using stolen credentials from mega-breaches. In 2026, passwords alone cannot protect modern enterprises. Managed Security Service Providers (MSSPs) deploy sophisticated behavioral analytics, bot mitigation, and automated response systems to combat these automated threats effectively.
What Are Credential Stuffing Attacks?
Credential stuffing uses automated bots to test username/password combinations harvested from data breaches against thousands of websites simultaneously. Attackers exploit password reuse—where users recycle credentials across platforms—achieving 0.2-2% success rates that scale massively across billions of combinations.
The Attack Lifecycle
Breach Harvesting: Mega-breaches expose 149M+ credentials (Jan 2026)
Automated Testing: Bots test millions of combinations per minute
Account Takeover: Successful logins grant attacker access
Fraud & Lateral Movement: PII theft, ransomware deployment, privilege escalation
Why Traditional Passwords Fail
Scale Overwhelms Manual Defenses
Attackers use global proxy networks and residential IPs to distribute attacks, evading basic IP blocking. Single compromised credentials unlock multiple systems due to reuse across platforms.
Stealth Through Legitimate Appearance
Credential stuffing generates valid login traffic indistinguishable from normal user activity. Traditional WAFs and rate limiting struggle against sophisticated botnets mimicking human behavior.
MFA Bypass Techniques
Even multi-factor authentication fails against:
Session hijacking after initial login
MFA fatigue attacks (bombardment)
Social engineering for one-time codes
SIM swapping for SMS-based MFA
MSSP Defenses Against Credential Stuffing
Behavioral Biometrics & UEBA
MSSPs analyze 100+ behavioral signals to distinguish humans from bots:
Human patterns: Natural mouse movement, typing cadence, 9-5 login times
Bot signatures: Perfect mouse paths, uniform keystroke timing, 24/7 activity
Device fingerprinting creates unique signatures combining browser characteristics, screen resolution, time zone, and installed fonts—invisible to attackers.
Advanced Bot Management
Next-generation WAFs with machine learning bot scoring:
| Detection Method | Effectiveness |
|---|---|
| CAPTCHA bypass timing analysis | 98% |
| Mouse entropy analysis | 99% |
| Dynamic behavioral rate limiting | 99.5% |
| ML-updated bot signatures | 99.9% |
Dark Web Credential Monitoring
MSSPs continuously scan dark web markets, paste sites, and Telegram channels for your organization's credentials:
1. Credential discovered → 2. Automated password reset
→ 3. MFA enforcement → 4. Device quarantine
Average response time: 12 minutes vs. weeks for internal teams.
Adaptive Authentication Framework
Risk-based access controls challenge only suspicious logins:
| Risk Level | Example | Authentication Required |
|---|---|---|
| Low | Known device + corporate IP | Password only |
| Medium | New browser | Email OTP |
| High | Datacenter IP + 3AM login | Hardware token + biometrics |
| Critical | Dark web credential match | Account suspension |
Passwordless Authentication Migration
MSSPs implement FIDO2 passkeys, certificate-based authentication, and biometrics, eliminating passwords entirely for high-value systems.
SIEM + SOAR Automated Response
Security Orchestration platforms execute response playbooks instantly:
ALERT: 75 failed logins in 90 seconds from 3 IPs
→ EXECUTE: Block IPs → Quarantine devices → Notify SecOps → Forensic analysis
Mean Time to Respond: 47 seconds vs. days manually.
Credential Stuffing Success Metrics
| Defense Layer | MSSP Capability | Attack Reduction |
|---|---|---|
| Behavioral UEBA | 100+ signal analysis | 97% |
| Bot Management | ML-powered WAF | 99.9% |
| Dark Web Monitoring | Real-time hunting | 100% proactive |
| Passwordless Auth | FIDO2 implementation | Eliminates passwords |
| SOAR Automation | Playbook execution | MTTR: 47 seconds |
Real-World MSSP Results
Financial Services Client:
Before MSSP: 2,847 successful ATOs/month
After MSSP: 0 successful ATOs in 24 months
Result: $4.2M annual fraud prevention
Healthcare Provider:
85% reduction in helpdesk password resets
Zero ransomware entry via credential stuffing
30% cyber insurance premium reduction
The Passwordless Future
MSSPs accelerate migration to modern authentication:
Phase 1: Risk-based MFA everywhere
Phase 2: Passwordless for critical systems
Phase 3: Enterprise-wide FIDO2 passkeys
Phase 4: Certificate-based machine auth
Result: 100% elimination of credential stuffing risk
Conclusion
Credential stuffing represents cybercrime industrialization—billions of automated attempts exploiting inevitable password reuse. Traditional passwords fail catastrophically against this scale and sophistication.
MSSPs deliver intelligence-led defense combining behavioral analytics, bot mitigation, dark web monitoring, and automated response to shrink attack surfaces to near-zero.
CyberSecOp stops credential stuffing before damage occurs.
Protect Your Organization Today
Eliminate credential stuffing risks with CyberSecOp's comprehensive MSSP platform:
✅ Dark web credential hunting
✅ AI behavioral defense
✅ Passwordless migration expertise
✅ 24/7 automated response
Schedule your credential risk assessment:
Customer Service: 1 866-973-2677 Sales: Sales@CyberSecOp.com
Data Exfiltration: How Hackers Steal Your Data Without You Noticing
Data exfiltration represents the final stage of most successful cyberattacks, where attackers quietly extract sensitive information over weeks or months without triggering alarms. In 2026, sophisticated threat actors use stealth techniques to bypass traditional security controls, making exfiltration detection one of cybersecurity's greatest challenges. Managed Security Service Providers (MSSPs) deploy advanced monitoring, behavioral analytics, and automated response capabilities to prevent and detect unauthorized data transfers before damage becomes irreversible.
What is Data Exfiltration?
Data exfiltration occurs when malicious actors covertly transfer sensitive data from your environment to external destinations under attacker control. Unlike ransomware's dramatic encryption, exfiltration operates silently, often going undetected until intellectual property theft, customer data compromise, or regulatory violations surface.
Common Exfiltration Techniques
DNS Tunneling
Attackers encode stolen data within DNS queries, disguising malicious traffic as legitimate domain resolution requests. This technique evades firewalls monitoring only HTTP/HTTPS traffic.
Encrypted Channel Abuse
Malware establishes HTTPS/SMB connections to legitimate cloud services like Dropbox, OneDrive, or GitHub, blending exfiltration with normal business traffic.
Office 365 & SaaS Exploitation
Compromised credentials enable attackers to upload data to personal OneDrive accounts, share via Teams, or exfiltrate through legitimate enterprise SaaS applications.
Cloud Storage Misuse
Stolen API keys grant access to misconfigured S3 buckets, Azure Blob storage, or Google Cloud repositories where attackers stage data for later extraction.
Stealth Exfiltration Methods Attackers Use
Low-and-Slow Transfers
Attackers send small data packets at regular intervals over extended periods, blending with normal user behavior while extracting massive volumes undetected.
Legitimate Protocol Abuse
Attackers route data through HTTPS to CDN domains, SMTP email attachments, FTP/SFTP to business partners, or database replication to attacker-controlled servers.
Data Compression & Obfuscation
Sensitive data gets compressed, Base64 encoded, and split across multiple files and domains, evading volume-based Data Loss Prevention (DLP) systems.
Why Traditional Security Fails
Data Loss Prevention (DLP) Limitations
Traditional DLP struggles against encrypted traffic (95% of web traffic), unknown data classifications, legitimate cloud service usage, insider threat patterns, and compressed/obfuscated payloads.
Network Monitoring Blind Spots
Firewall logs miss DNS tunneling (UDP port 53), internal east-west movement, SaaS application uploads, and encrypted archive transfers.
How MSSPs Prevent and Detect Data Exfiltration
Network Traffic Analytics (NTA)
MSSPs deploy AI-powered network sensors analyzing all protocols:
| Protocol | Exfiltration Risk | MSSP Detection |
|---|---|---|
| DNS (UDP 53) | High | Query entropy analysis |
| HTTPS (TCP 443) | High | Certificate pinning detection |
| SMB (TCP 445) | Medium | Unusual share access patterns |
| SMTP (TCP 25) | Medium | Volume + destination analysis |
User and Entity Behavior Analytics (UEBA)
Continuous baseline monitoring flags anomalous data movement patterns for specific users and roles.
Cloud Access Security Broker (CASB)
MSSPs monitor all SaaS interactions, distinguishing legitimate business usage from malicious uploads to personal cloud storage.
Endpoint Detection and Response (EDR)
Behavioral monitoring catches local exfiltration attempts like PowerShell compressing databases to USB drives.
Data Flow Mapping and Classification
MSSPs create dynamic data maps identifying crown jewel assets, unusual destinations, and excessive volumes for specific user roles.
MSSP Exfiltration Prevention Framework
Layer 1: Discovery and Classification
Automated data discovery across endpoints, servers, and cloud environments identifies and classifies crown jewel assets with risk-based tagging.
Layer 2: Continuous Monitoring
Comprehensive monitoring covers network protocols, cloud SaaS traffic, endpoint file operations, and identity access patterns simultaneously.
Layer 3: Automated Response
Security Orchestration platforms execute response playbooks instantly, blocking connections and quarantining systems within seconds.
Real-World MSSP Success Stories
Manufacturing Giant
UEBA and CASB detected anomalous GitHub uploads by compromised engineering credentials, blocking 18GB of IP theft and terminating three insiders. Result: $42M R&D preservation.
Financial Services
Network Traffic Analytics identified DNS tunneling patterns exfiltrating customer data, blocking 7TB of attempted theft with no customer impact, and avoiding $15M GDPR fines.
Exfiltration Detection Metrics
| Detection Method | False Positive Rate | Detection Speed | Coverage |
|---|---|---|---|
| Network Analytics | 0.3% | Real-time | 100% protocols |
| UEBA | 1.2% | Real-time | User + machine |
| CASB | 0.8% | Real-time | All SaaS traffic |
| EDR | 2.1% | <60 seconds | Endpoint activity |
The MSSP Advantage
MSSPs provide full protocol coverage, AI-driven anomaly detection, automated response orchestration, and 24/7 expert analysts—capabilities beyond most internal security teams.
Conclusion
Data exfiltration succeeds through stealth, patience, and legitimate protocol abuse. Attackers spend months extracting terabytes while security teams chase false positives. MSSPs eliminate these blind spots through comprehensive monitoring, behavioral analytics, and automated response.
CyberSecOp stops data exfiltration before it starts.
Stop Data Theft with CyberSecOp
Secure your data with CyberSecOp's comprehensive exfiltration prevention:
Full protocol visibility
AI-powered behavioral analytics
Cloud-native CASB protection
Automated response orchestration
Schedule your data protection assessment:
Customer Service: 1 866-973-2677 Sales:Sales@CyberSecOp.com
CyberSecOp's Cyber & AI Leadership Summit 2026: Key Takeaways and What You Missed
The Cyber & AI Leadership Summit 2026, held on March 11 in New Rochelle, NY, brought together cybersecurity executives, CISOs, legal experts, and risk leaders for a transformative day of strategic insights. Hosted in collaboration with the Global CISO Leadership Foundation and featuring prominent CyberSecOp speakers, the summit addressed the accelerating challenges of AI-driven threats, expanding attack surfaces, regulatory pressures, and board-level expectations shaping cyber leadership in 2026.
If you attended, revisit the highlights. If you missed it, discover why this event sets the standard for executive cybersecurity dialogue—and how CyberSecOp can help you implement these strategies.
Summit Recap: Conversations That Defined Cyber Leadership
Opening Keynote: "Reasonable Security in the Era of Agentic AI"
Curtis Dukes, Executive VP & GM at the Center for Internet Security, and Chirag Arora, Chair of the Global CISO Leadership Foundation, set the tone by examining what "reasonable security" means as enterprises deploy autonomous AI systems.
Key Insights:
Agentic AI requires new governance models beyond traditional controls
"Due care" definitions are evolving with AI decision-making capabilities
Practical frameworks for immediate implementation were shared
Security vs. Compliance Think Tank
Tom Guadagno, CISO at CyberSecOp, facilitated a candid discussion challenging the "checkbox compliance" mindset that leaves organizations vulnerable despite passing audits.
Attendees Explored:
Real-world compliance failures leading to breaches
Metrics that demonstrate measurable risk reduction to boards
Aligning security operations with regulatory requirements
External Attack Surface Management
Chirag Arora delivered a board-level roadmap for closing external security gaps across cloud, SaaS, AI integrations, and third-party ecosystems—the fastest-growing source of cyber risk.
CyberSecOp's Leadership Presence
CyberSecOp executives dominated the agenda, showcasing our position as a #1 ranked security consulting provider (Gartner Peer Insights 2025):
Tom Guadagno, CISO
Led the Security vs. Compliance think tank
Panelist on the CISO Executive Panel
Oscar Jones & Mike Schimenti, CISOs
Featured in the closing "AI Exposure: The Next-Gen Challenge for Cyber Leaders" executive panel alongside Chirag Arora
Proven Expertise in Action
Attendees experienced why CyberSecOp consistently earns top industry recognition—delivering practical, board-ready strategies that translate into measurable business outcomes.
Additional Summit Highlights Attendees Raved About
🛡️ Cyber Insurance Strategy – Imani Barnes from Risk Strategies on sizing coverage for business interruption and third-party failures.
🔒 Zero Trust at the Browser Layer – Sean Fischer from Island.io demonstrated agentless security for the new enterprise control plane.
⚖️ Legal Deep Dive – Professor Antony Haynes from Albany Law School analyzed AI agent liability using landmark cases like Perplexity v. Amazon.
💾 Ransomware-Resilient Architectures – Nutanix showcased backup strategies that assume compromise and preserve data integrity.
📊 Unified Audits – Brad Lyons from 360Advanced explained "Audit Once, Report Many" methodologies that reduce fatigue while improving maturity.
Why This Summit Mattered
Unlike typical vendor-driven events, the Cyber & AI Leadership Summit delivered:
High-Impact Peer Dialogue among CISOs and executives
Board-Ready Insights on AI governance, external exposure, and compliance evolution
Practical Frameworks attendees could implement immediately
Unparalleled Networking with cyber leadership peers
Implement Summit Strategies with CyberSecOp
Missed the event? CyberSecOp brings these proven strategies to your organization through our world-class MSSP services:
✅ Agentic AI governance frameworks
✅ External attack surface management
✅ Zero Trust browser security
✅ Operationalized GRC platforms
✅ Ransomware-resilient architectures
✅ Unified audit and compliance programs
Client Testimonials from Summit Attendees
"CyberSecOp's CISO panel cut through the AI hype and delivered practical strategies we implemented the next week." – Director of Cybersecurity, Fortune 1000
"Tom Guadagno's think tank reframed our entire compliance approach. We're already seeing risk reduction metrics." – VP Information Security, Financial Services
Next Steps: Partner with CyberSecOp
Transform summit insights into actionable security outcomes with CyberSecOp's award-winning managed security services.
Schedule your personalized cybersecurity strategy session:
📞 Customer Service: 1 866-973-2677
✉️ Sales: Sales@CyberSecOp.com
🎯 Subject: "Cyber AI Summit Follow-Up Strategy Session"
Stay Connected with CyberSecOp Events
Follow CyberSecOp for upcoming executive briefings, webinars, and leadership summits featuring our CISO team:
Monthly CISO Roundtables
Quarterly Threat Landscape Briefings
AI Security Strategy Workshops
How MSSPs Secure the Financial Sector Against Cyber Heists and Fraud
The financial sector faces relentless cyber threats in 2025, from sophisticated heists stealing millions to widespread fraud exploiting digital banking. Banks and financial institutions handle sensitive data and high-value transactions, making them prime targets for cybercriminals. Managed Security Service Providers (MSSPs) deliver tailored cybersecurity solutions to meet stringent regulatory demands and protect against evolving attacks.
Unique Cybersecurity Challenges in the Financial Sector
Regulatory Compliance Pressures
Financial institutions must adhere to rigorous standards like PCI DSS, GLBA, SOX, and FFIEC guidelines. Non-compliance risks massive fines—up to 4% of global revenue under GDPR—and reputational damage.
High-Value Transaction Vulnerabilities
Real-time payment systems, SWIFT networks, and mobile banking create opportunities for fraud, with cyber heists averaging $4.5 million per incident.
Advanced Persistent Threats (APTs)
Nation-state actors and organized crime groups launch targeted attacks using zero-days, supply chain compromises, and insider threats to infiltrate core banking systems.
Fraud at Scale
Account takeover (ATO), synthetic identity fraud, and payment redirection scams surged 35% in 2025, exploiting AI-driven automation.
How MSSPs Provide Tailored Solutions for Financial Institutions
24/7 Security Operations Centers (SOCs) with Financial Expertise
MSSPs deploy specialized SOC teams trained in financial crime patterns, monitoring transactions, logs, and endpoints continuously to detect anomalies like unusual wire transfers or login spikes.
Real-Time Transaction Monitoring
Advanced behavioral analytics flag suspicious activities, such as high-velocity small transactions or geographic mismatches, preventing fraud before settlement.
Zero Trust Architecture Implementation
MSSPs enforce strict identity verification, micro-segmentation, and least-privilege access across hybrid cloud and on-premises banking environments, limiting lateral movement during breaches.
Multi-Factor Authentication (MFA) and Biometrics
Adaptive MFA combines device trust, behavioral biometrics, and risk-based authentication to secure remote access for tellers, traders, and executives.
AI-Powered Fraud Detection and Prevention
Machine learning models analyze petabytes of transaction data in real-time, identifying synthetic identities, ATO attempts, and deepfake-driven scams with 99% accuracy.
Threat Hunting for APTs
Proactive hunts using MITRE ATT&CK frameworks uncover dormant threats in core banking systems, SWIFT gateways, and third-party vendor networks.
Comprehensive Compliance and Audit Support
MSSPs automate evidence collection for PCI DSS, SOC 2, and FFIEC audits, generating executive reports that demonstrate control effectiveness and risk posture.
Incident Response Tailored to Financial Regulations
Pre-defined playbooks ensure rapid containment while preserving chain-of-custody for regulatory notifications within mandatory timelines (e.g., 72 hours under GDPR).
Endpoint and Network Protection for Branch Operations
MSSPs secure ATMs, POS terminals, and branch networks with EDR, next-gen firewalls, and Deception Technology that lures attackers into honeypots.
Vendor and Third-Party Risk Management
Continuous monitoring of fintech partners, payment processors, and cloud providers prevents supply chain attacks that compromise 40% of financial breaches.
Proven Benefits of MSSP Partnerships for Banks
Reduced Fraud Losses: Clients report 60-80% drops in unauthorized transactions.
Faster Breach Containment: Mean time to respond (MTTR) under 30 minutes vs. industry average of 277 days.
Premium Reductions: Cyber insurance discounts of 20-30% through demonstrated security maturity.
Scalability: Handles peak volumes during trading hours or tax seasons without staffing spikes.
Conclusion
Financial institutions cannot afford downtime or data compromise in a sector where trust equals revenue. MSSPs like CyberSecOp provide the specialized expertise, technology stack, and regulatory alignment needed to secure against cyber heists, fraud rings, and APTs while enabling digital innovation.
Partner with CyberSecOp for Financial Sector Cybersecurity
Fortify your bank's defenses with CyberSecOp's MSSP solutions designed specifically for the financial industry. From transaction monitoring to compliance automation, we deliver enterprise-grade protection tailored to your risk profile.
Contact us today to schedule a financial security assessment:
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com
Deepfake Fraud: How Cybercriminals Are Using AI to Impersonate Executives
Deepfake fraud has surged in 2025, with cybercriminals using AI-generated videos, audio, and voice clones to impersonate executives in scams targeting businesses. These attacks trick employees into transferring funds, revealing sensitive data, or granting unauthorized access, resulting in multimillion-dollar losses like the $25 million Arup incident in 2024.
The Rise of Deepfake Executive Impersonation
AI tools enable attackers to create hyper-realistic deepfakes from mere seconds of public audio or video, such as podcasts or webinars. Common tactics include:
Vishing (Voice Phishing): Cloned executive voices in urgent calls demanding wire transfers or confidential info, with vishing attacks up 170% in Q2 2025.
Video Deepfakes: Real-time face-swaps during video calls, fooling even security experts; 40% of IT pros reported executive deepfake targets in 2025, up from 33% in 2023.
Whaling Attacks: Highly targeted scams mimicking CEOs or CFOs via multi-channel escalation (email, calls, video), often bypassing biometrics.
BEC (Business Email Compromise): Deepfakes combined with phishing to divert vendor payments.
Deepfake files exploded from 500K in 2023 to 8M in 2025, with fraud attempts spiking 3,000%.
Business Impacts and Real-World Examples
These scams exploit trust in leadership, causing financial devastation, data breaches, and reputational harm. Attackers target finance/HR teams under end-of-quarter pressure, leading to unauthorized transactions or espionage. Executives face personal risks too, as breaches extend to home networks. Startups like imper.ai raised $28M in December 2025 to combat this boom.
How MSSPs Mitigate Deepfake Threats
Managed Security Service Providers (MSSPs) deploy layered defenses to detect and neutralize deepfakes:
AI-Powered Detection Tools: Analyze media for inconsistencies in audio-visual data, voice patterns, and liveness challenges to verify authenticity in real-time.
Behavioral Analytics and UEBA: Monitor anomalies like unusual access requests or multi-channel escalations tied to impersonation attempts.
Phishing Simulations and Training: Run realistic deepfake/vishing drills with executive clones, code-phrase systems, and verification protocols (e.g., callback policies).
Incident Response Playbooks: 90-day frameworks for risk assessment, technical controls (e.g., payment gates), and board reporting to contain scams swiftly.
Threat Intelligence Integration: Track emerging deepfake tools like Deep-Live-Cam and global IoCs for proactive blocking.
These measures reduce human error—the key deepfake vulnerability—while automating responses.
Conclusion
Deepfake executive impersonation exploits AI realism and human trust, driving massive fraud in 2025. MSSPs counter with advanced detection, training, and rapid response, turning potential crises into manageable risks.
Protect Against Deepfake Fraud with CyberSecOp
Secure your executives and teams from AI scams through CyberSecOp’s MSSP services featuring deepfake detection and proactive defenses.
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com
Cyber Insurance: What It Covers (and Why an MSSP is Still Necessary)
Cyber insurance provides financial protection against the aftermath of cyberattacks, covering costs like data breaches and ransomware that average $3.86 million per incident in 2025. With the global market reaching $20.56 billion this year and 62% of firms now insured (up from 49% in 2024), policies help mitigate recovery expenses—but they do not prevent attacks or reduce premiums without strong defenses.
What Cyber Insurance Typically Covers
Policies vary but generally include first-party (direct business losses) and third-party (liability to others) coverage:
Data Breaches and Incident Response: Forensic investigations, notification costs, and credit monitoring for affected individuals.
Ransomware and Extortion: Payments (where allowed), decryption tools, and recovery efforts; ransomware drives 60% of large claims.
Business Interruption: Lost revenue from downtime during recovery.
Legal and Regulatory Fines: Defense costs, settlements, and penalties for non-compliance (e.g., GDPR, HIPAA).
Reputation Management and Third-Party Claims: PR support and lawsuits from customers or partners.
Exclusions are tightening, often denying claims for outdated software, unpatched systems, or poor cybersecurity hygiene, pushing premiums up 15-20% annually.
Why Businesses Still Need MSSPs for Proactive Security
Cyber insurance is reactive—it pays after damage occurs and increasingly requires proof of robust security (e.g., MDR, EDR) for coverage or lower rates, with proactive measures cutting premiums by up to 20%. MSSPs provide essential prevention that insurance cannot:
Continuous Threat Monitoring and Detection: 24/7 SOCs identify threats early, reducing breach likelihood and claim frequency (down 50% in 2025).
Incident Response and Remediation: Rapid containment minimizes downtime and costs, preserving insurability.
Compliance and Risk Management: Automated audits and frameworks ensure policies remain valid amid stricter underwriting.
Advanced Defenses: AI-driven tools combat ransomware (33% of claims from manufacturing) before escalation.
Without MSSPs, businesses face higher premiums, claim denials, and uninsurable risks in a market projected to hit $30 billion by 2030.
Conclusion
Cyber insurance safeguards finances post-breach but demands proactive security for viability. MSSPs deliver the prevention, monitoring, and response that keep attacks at bay, ensuring coverage remains affordable and effective.
Strengthen Your Defenses with CyberSecOp
Combine cyber insurance with CyberSecOp’s MSSP services for comprehensive protection and premium savings.
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com
Cyber & AI Leadership Summit In-person EventIn Collaboration with Global CISO Leadership Foundation
Modern cyber risk is accelerating faster than most organizations can adapt—and 2026 will be defined by AI driven threats, expanding attack surfaces, legal uncertainty, and rising board expectations.
From agentic AI and external exposure to cyber insurance, Zero Trust, legal risk, GRC modernization, ransomware resilient architectures, and an executive CISO panel, this event delivers the insights and peer dialogue required to stay ahead of what’s coming next.
Wednesday, March 11, 2026
9:00 AM 5:00 PM
Hotel NoMa ,1 Radisson PlazaNew Rochelle, NY, 10801United States (map)
9-9:30AM EST (30min)
Welcome, Networking Breakfast & Partner Tables - Sponsored by 360Advanced
9:30 -9:45AM EST (15min)
Kickoff and Agenda
Featured Speakers: Gina Fideli, P3 Transformation Founder - HOST
Set the tone, expectations & session logistics and Introductions
9:45-10:30AM EST (45min)
Opening Keynote: “Reasonable Security in the Era of Agentic AI”
Featured Speakers: Curtis Dukes, Executive Vice President & General Manager, Center for Internet Security (CIS) & Chirag Arora, Global Ambassador, Center for Internet Security; Chair, Global CISO Leadership Foundation.
This keynote will examine what “reasonable security” means as enterprises adopt agentic AI systems capable of autonomous decision-making. The session will explore governance expectations, evolving definitions of due care, and practical frameworks organizations can adopt today.
10:30-11:15AM EST (45min)
Roadmap to Closing Your Organization’s External Security Gaps: Managing External Exposure, Brand Risk, and Dark Web Threats in a Rapidly Expanding Attack Surface
Presenter: Chirag Arora, Global Security Leader
Session Overview
As organizations rapidly expand their digital footprint across cloud, SaaS, AI integrations, and third-party ecosystems, external exposure has become the fastest-growing source of cyber risk. Traditional internal security controls alone are no longer sufficient to detect, prioritize, or prevent real-world breaches.
This session provides a practical, board-level roadmap for identifying and closing security gaps across external attack surface, brand abuse, and dark web intelligence, using real-world threat patterns and exposure data.
11:15-12:00PM EST (45min)
Security vs. Compliance: Why “Checking the Box” Keeps Failing CISOs: A Think Tank on Bridging Real Risk Reduction and Regulatory Expectations
Format: Think Tank Discussion
Facilitator: Oscar Jones, CISO, CyberSecOp
Session Framing
Security and compliance are often treated as interchangeable—but in practice, they frequently work against each other. Organizations pass audits yet still get breached. CISOs invest heavily in frameworks, assessments, and controls, while attackers continue to exploit gaps that compliance programs never surface.
This think tank brings security leaders together to challenge conventional thinking, examine real-world failures, and explore how CISOs can move beyond checkbox compliance toward measurable risk reduction—without breaking regulatory alignment.
12-12:15PM (15min)
Properly Sizing Cyber Insurance
Speaker: Imani Barnes, Associate Director, RiskStrategies
Session Overview
Cybersecurity can lower your risk, but it can’t protect you from every weak link in your digital ecosystem. With cyber incidents and business interruption ranked as the top global risks, organizations must prepare for the ripple effects of third‑party failures. That’s why cyber insurance, especially contingent business interruption coverage, has become an essential safety net for the threats you can’t control.
12:15-12:45PM Sponsored by RiskStrategies
Lunch, Networking Break
12:45-1:30PM (45min)
Operationalizing Zero Trust at the Browser Layer: Real-World Use Cases Enabled
Speaker: MacKenzie Miller, CAM of Island.io
Session Overview
As work increasingly happens inside the browser—across SaaS, cloud consoles, AI tools, and legacy web apps—the browser has become the new control plane for enterprise security, data protection, and compliance.
This session shows how Island’s Enterprise Browser Console modules enable organizations to secure access, prevent data loss, and reduce attack surface without agents, VPNs, or virtual desktops—while preserving user experience.
1:30-2:15PM EST (45min)
Legal Deep Dive: “AI Agents, Liability & the Courts: Lessons from Perplexity v. Amazon”
Speaker: Antony Haynes, Professor of Law, Albany Law School; Group Head, Cybersecurity, Data Privacy & AI Practice, Dorf Nelson & Zauderer LLP
A forward-looking analysis of the emerging legal landscape for both developers of agentic systems and organizations deploying agents as users. Using Perplexity v. Amazon as the anchor case, this session will cover IP liability, contractual risk allocation, tort exposure, and what corporate counsel must anticipate as AI autonomy increases.
2:15-2:45 EST (30min)
Operationalizing Cyber Resilience: Turning GRC from Compliance Burden into Business Capability: How Modern GRC Enables Measurable Resilience Across Security, Risk, and Operations
Speakers: Shareth Ben, VP of Sales & Strategy, Apptega & Tom Guadagno, CISO of CyberSecOp
Session Overview
Most organizations invest heavily in Governance, Risk, and Compliance (GRC), yet struggle to translate frameworks, assessments, and policies into day-to-day operational resilience. GRC is often perceived as documentation-heavy and reactive—disconnected from how security teams actually manage risk.
This session explores how modern GRC programs can be operationalized to drive real resilience by aligning security operations, risk management, and compliance into a single, actionable system of record.
2:45-3:15PM EST (30min)
How Unified Audits Reduce Cost, Fatigue and Improve Security Program Maturity
Speakers: Jim Brennan, Sr. Compliance Executive
Session Overview
An Audit Once, Report Many methodology is designed to streamline the entire experience by consolidating the overlapping requirements across frameworks and conducting a single, comprehensive audit that supports all the needed reports. We gather evidence once, validate controls once, and then map the results into each relevant framework for delivery. The result? A more efficient, predictable, and less disruptive audit experience.
3:15-3:50 EST (35min)
Ransomware-Proof by Design: Building Resilient, Recoverable, and Trustworthy Data Backups: How Modern Enterprises Ensure Recovery When Prevention Fails
Presenter: Nutanix (Speaker TBD – Field CTO / Distinguished Technologist / Security Architect)
Session Overview
Ransomware is no longer just an encryption event—it is a data integrity and recovery crisis. Attackers increasingly target backups first, corrupt recovery points, and exploit operational complexity to delay restoration.
This session explores how organizations can design robust, ransomware-resilient backup and recovery architectures that assume compromise, preserve trust in data, and enable rapid, confident recovery—without adding operational overhead.
3:50-4:30PM EST (40min)
CISO Executive Panel: “AI Exposure: The Next-Generation Challenge for Cyber Leaders”
Panelists: Oscar Jones, Mike Schimenti & Tom Guadagno, Cybersecurity CISOs, Chirag Arora, Chair, Global CISO Leadership Foundation & Additional New York–based CISO (TBD)
A practical and strategic discussion on how AI-driven exposures—LLM integration, agentic automation, API misuse, data governance gaps, and digital supply chain risks—are reshaping the CISO agenda for 2025–2026. This panel will highlight real-world scenarios, defense strategies, and what cyber leaders need to prioritize now.
4:30-5PM EST
Raffle + Closing Remarks
Featured Speakers: Gina Fidely/HOST & Vinny LaRocca/CEO
5 -6PM EST Sponsored by Island.io
Happy Hour + Open Networking
MSSP vs. MDR: Understanding the Differences and Which One Your Business Needs
In 2025, cybersecurity solutions have become more specialized, and businesses often face the choice between engaging a Managed Security Service Provider (MSSP) or a Managed Detection and Response (MDR) service.
In 2025, cybersecurity solutions have become more specialized, and businesses often face the choice between engaging a Managed Security Service Provider (MSSP) or a Managed Detection and Response (MDR) service. Both play vital roles in enhancing cybersecurity, but they serve distinct purposes and offer different capabilities. Understanding these differences will help you decide which solution fits your organization's security needs.
What is an MSSP?
A Managed Security Service Provider (MSSP) offers a broad range of outsourced security management services. Their core focus is on prevention, management, and monitoring of security infrastructure, including firewalls, antivirus solutions, vulnerability assessments, patch management, compliance management, and alert monitoring. MSSPs primarily act as an extension of an organization's internal security team, providing 24/7 monitoring and alerting based on predefined thresholds.
Key Characteristics of MSSPs:
Scope: Broad security service coverage including device management, compliance, and basic incident alerting.
Approach: Emphasis on prevention through controls, configurations, and monitoring.
Response: Typically alert-based — MSSPs notify the organization about security events; internal teams often handle in-depth investigations and responses.
Expertise Level: General cybersecurity skills across various domains.
Cost: Generally more cost-effective than MDR, especially for organizations requiring broad security coverage.
Integration: May require complex setups integrating with existing client infrastructure.
What is MDR?
Managed Detection and Response (MDR) is a specialized service focusing specifically on continuous threat detection, proactive hunting, and rapid incident response. MDR providers assume that breaches can occur, so their priority lies in swiftly identifying and neutralizing active threats to minimize damage.
Key Characteristics of MDR:
Scope: Focused on detecting sophisticated threats, incident investigation, and remediation.
Approach: Proactive and real-time threat detection combined with immediate response.
Response: Hands-on involvement, including investigation, containment, and mitigation by the MDR team.
Expertise Level: Highly specialized analysts skilled in deep detection, threat hunting, and forensics.
Cost: Typically higher than MSSPs, reflecting the depth of response and expertise.
Integration: Requires tight integration with endpoint, network, and security tools for optimal detection and response.
Comparing MSSP and MDR Side by Side
| Aspect | MSSP | MDR |
|---|---|---|
| Primary Focus | Security infrastructure management, monitoring, and alerting | Real-time threat detection, hunting, and incident response |
| Security Approach | Preventive and reactive | Proactive and reactive |
| Alert & Response | Alert-based, with response often by client | Direct response and containment by provider |
| Expertise Level | Broad cybersecurity knowledge | Specialized threat detection and incident handling |
| Service Scope | Broad security services including compliance | Focused on sophisticated attacks and rapid response |
| Cost | More affordable for broad coverage | Higher cost due to depth and immediacy of services |
| Ideal For | Organizations needing comprehensive security coverage and compliance assistance | Organizations facing advanced persistent threats needing rapid, expert response |
Which One Does Your Business Need?
Choose an MSSP if you need a broad, ongoing security management partner to handle your infrastructure, compliance, and general alert monitoring.
Choose MDR if you require specialized, proactive threat detection and a rapid incident response team that actively investigates and neutralizes ongoing attacks.
Many organizations benefit from a hybrid approach, where MSSPs provide general security support and MDR services augment detection and response capabilities.
Conclusion
While MSSPs focus on managing and monitoring your overall security posture, MDR services dive deeper to detect and respond to sophisticated, active threats. Both are integral to a comprehensive cybersecurity strategy, and selecting the appropriate service depends on your organization's risk profile, budget, and security maturity.
CyberSecOp offers both MSSP and MDR services, delivering tailored cybersecurity solutions to meet your unique business needs.
Secure Your Business with CyberSecOp
Find out which managed security solution is right for you with CyberSecOp’s expert guidance.
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com
How MSSPs Use Threat Hunting to Stop Cybercriminals Before They Strike
In 2025, cyber threats continue to grow in complexity, with adversaries constantly evolving tactics to evade detection.
In 2025, cyber threats continue to grow in complexity, with adversaries constantly evolving tactics to evade detection. Managed Security Service Providers (MSSPs) adopt threat hunting as a proactive security measure to identify and eliminate hidden threats before they cause damage. Unlike reactive approaches that wait for alerts, threat hunting involves actively searching for signs of compromise in network and endpoint data to uncover stealthy attackers.
Proactive Security Measures in MSSP Threat Hunting
1. Data Aggregation and Preparation
MSSPs collect and normalize diverse security data including logs, network traffic, endpoint telemetry, and threat intelligence from various sources. This consolidated dataset forms the foundation for effective threat hunting.
2. Structured and Hypothesis-Driven Hunting
Analysts use structured methodologies such as the MITRE ATT&CK framework to explore specific attacker tactics, techniques, and procedures (TTPs) relevant to client environments. Hypotheses based on recent threat intelligence or behavioral anomalies guide targeted searches to uncover hidden malicious activities.
3. AI and Machine Learning Analytics
Advanced MSSPs employ AI/ML to sift through vast datasets, identify anomalies, and correlate seemingly unrelated events that human analysts might miss. AI enhances pattern recognition for detecting novel attack vectors, reducing false positives and focusing on genuine threats.
4. Threat Intelligence Integration
Real-time threat intelligence feeds inform hunters about emerging Indicators of Compromise (IoCs) and new adversary profiles. This intel enriches hunts, enabling early detection of known and unknown threats.
5. Flexible Hunting Approaches
Combining automated exploratory scans with focused, event-driven hunts allows MSSPs to benchmark normal behavior, identify deviations, and adapt dynamically to evolving attack methods.
6. Rapid Investigation and Incident Response
Once suspicious activity is discovered, MSSPs leverage automated workflows and Security Orchestration, Automation, and Response (SOAR) tools to quickly contain threats, minimize dwell times, and reduce impact.
The Business Benefits of MSSP Threat Hunting
Early Detection: Catch attackers before they escalate attacks or exfiltrate data.
Reduced Damage: Minimize operational disruption, data loss, and financial impact.
Improved Security Posture: Identify gaps and improve defenses proactively.
Regulatory Compliance: Demonstrate proactive risk management for auditors and regulators.
Operational Efficiency: Leverage AI and automation to maximize security team productivity.
Conclusion
Threat hunting is a game-changer in cybersecurity, shifting the paradigm from waiting to respond toward actively seeking threats before damage occurs. MSSPs, equipped with advanced analytics, threat intelligence, and skilled analysts, provide organizations with this crucial proactive defense layer, significantly reducing risk and enhancing cyber resilience.
Protect Your Business with CyberSecOp’s Threat Hunting Expertise
Stay ahead of cybercriminals with CyberSecOp’s managed threat hunting services that find and stop threats before they strike.
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com
AI-Generated Cyber Threats: How Hackers Use AI and How MSSPs Counter It
In 2025, cybercriminals are increasingly harnessing the power of artificial intelligence (AI) to elevate their attack capabilities, creating a new breed of AI-generated cyber threats.
In 2025, cybercriminals are increasingly harnessing the power of artificial intelligence (AI) to elevate their attack capabilities, creating a new breed of AI-generated cyber threats. These AI-enhanced attacks are more sophisticated, automated, and harder to detect, posing significant risks to organizations worldwide. Managed Security Service Providers (MSSPs) leverage advanced AI-driven defenses to counter these evolving threats actively. This blog explores how hackers use AI for cyberattacks and how MSSPs employ AI to protect businesses.
How Hackers Use AI in Cyberattacks
AI-Powered Phishing and Social Engineering
Cybercriminals use AI-generated content to craft highly personalized and convincing phishing emails at scale. These messages often mimic writing styles and reference personal data, making them more difficult for users to identify as fraudulent. AI chatbots like FraudGPT are used to automate scams, increasing both reach and effectiveness.
AI-Driven Malware and Ransomware
AI enables malware to adapt in real-time, learning from the target environment to evade traditional endpoint detection and response (EDR) systems. For instance, ransomware strains like BlackMatter use AI to identify and encrypt the most valuable data while avoiding artifacts that trigger detection tools.
Deepfake Technology for Impersonation Attacks
Attackers deploy AI-generated audio and video deepfakes to impersonate executives, customers, or trusted parties, tricking employees into unauthorized transactions or divulging confidential information. The realism of these forgeries significantly complicates verification processes.
Automation of Attack Tools
Malicious AI models available on dark web forums provide “cybercrime as a service” by automating the generation of malicious code, phishing websites, and social engineering campaigns. This lowers the technical barrier for committing sophisticated cybercrime.
AI-Powered Reconnaissance
AI algorithms analyze vast data sets — including social media and network behavior — to identify vulnerabilities, map user behaviors, and pinpoint key targets for attacks, increasing the precision and success rate of campaigns.
How MSSPs Use AI to Combat AI-Generated Threats
1. AI-Enhanced Threat Detection
MSSPs deploy AI-powered Security Information and Event Management (SIEM) and User and Entity Behavior Analytics (UEBA) tools to identify anomalies and suspicious patterns indicative of AI-driven attacks, often before damage occurs.
2. Automated Incident Response and Hunting
Using AI-powered Security Orchestration, Automation, and Response (SOAR) platforms, MSSPs automate routine investigation and remediation tasks, accelerating response times and minimizing human error.
3. AI-Driven Phishing Detection
MSSPs utilize AI tools to scan inbound emails for AI-crafted phishing content, analyzing context, language nuances, and user history to block malicious messages effectively.
4. Deepfake Detection and Verification
Advanced AI models help MSSPs detect deepfake media by analyzing inconsistencies in audio-visual data, ensuring communications authenticity and preventing impersonation fraud.
5. Continuous Learning and Adaptation
MSSP AI tools continuously learn from new threat data, improving detection models in near real-time to keep pace with rapidly evolving AI-generated attack techniques.
Conclusion
The rise of AI-generated cyber threats presents unprecedented challenges for cybersecurity defense. Cybercriminals’ use of AI to automate, personalize, and evade detection requires equally sophisticated countermeasures. MSSPs, equipped with cutting-edge AI-enhanced tools and expert analysts, provide the proactive and adaptive defenses necessary to protect businesses from these next-generation threats.
Secure Your Business Against AI-Driven Cyberattacks with CyberSecOp
Partner with CyberSecOp to leverage AI-powered security technologies and expert managed services designed to detect and neutralize advanced AI-generated cyber threats.
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com
What the AWS Outage Exposed About Continuity, Dependency, and Real Resilience
The AWS outage in the US-East-1 region last week didn’t just disrupt services, it revealed how dependent most organizations have become on cloud providers without having continuity plans outside of them.
The recent AWS outage in the US-East-1 region wasn’t just another cloud hiccup. It was a leadership test for IT organizations across every industry, private sector, government, healthcare, finance. Some businesses stayed online. Most waited to recover. And everyone was reminded of an uncomfortable reality:
We’ve built mission-critical operations on cloud infrastructure, but we haven’t built a way to operate when it fails.
This wasn’t an attack. It wasn’t ransomware or a foreign adversary. It was an internal DNS automation failure at AWS. But the business impact was the same. Systems down, transactions halted, customers locked out, revenue on hold.
What Actually Happened
On October 20, 2025, around 3 a.m. ET, AWS experienced a failure inside its DNS automation and monitoring systems. A change removed critical DNS records for DynamoDB service endpoints, and automated recovery didn’t fix it. Applications could no longer resolve service addresses, which caused cascading failures.
By 6:01 p.m. ET, AWS declared services recovered. But the damage was already done.
Who Was Affected and How Bad Was It?
This wasn’t a small or regional outage.
According to the Guardian and Reuters, thousands of companies were affected globally. Some sources estimate well over 2,000 directly impacted providers and platforms.
Millions of end users reported failures, with more than 4 million outage reports recorded at peak.
Major platforms were affected, including Venmo, Ring, airlines, healthcare portals, banks, authentication platforms, retail sites, smart home platforms, and gaming services like Fortnite and Roblox.
Even government agencies and enterprises with segmentation, zoning, or isolated VPCs experienced interruptions, because the failure was at the provider layer, not inside customer environments.
How Much Did It Cost Businesses?
No one has a final number, but we do know this:
CyberCube estimates insured financial losses between $38 million and $581 million from this one event.
Broader economic impact, including lost revenue, productivity, and supply chain disruption, is expected to land in the hundreds of millions to billions.
Industry benchmarking tells us many enterprises lose between $300,000 and $5 million per hour of downtime. Some exceed $16,000 per minute.
A mid-size ecommerce business processing $100,000 a day in sales could have lost around $60,000 during the outage window, not including customer churn or recovery cost.
Multiply that across thousands of businesses over a 12 to 15-hour disruption, and the numbers add up quickly.
Why Some Organizations Stayed Online and Most Didn’t
This outage revealed a clear split.
| Organization Type | Outcome |
|---|---|
| Businesses with tested failover to Google Cloud, Azure, on-prem systems, or active-active infrastructure | Continued operating or saw minimal disruption |
| Organizations fully dependent on AWS US-East-1, often because of SaaS platforms, APIs, or identity providers | Operations paused until AWS recovered |
| Enterprises and government agencies with zoning, segmentation, or VPC separation | Still affected, because control plane and DNS failures sit above those protections |
| Organizations relying on Azure as a fallback | Were reminded Azure suffered a similar outage earlier in the year |
Azure Had the Same Problem with a Different Cause
Earlier in 2023, Azure experienced a major global disruption. A surge in network traffic and DDoS attempts caused Azure Portal and core services to become unavailable. Management functions, authentication, and critical services stalled.
Azure did not publish how many businesses were affected. AWS provided more detail in this recent event. Different clouds, different trigger points, same result. Operations stopped, IT teams scrambled, and executives wanted answers.
This isn’t about which cloud is safer. It’s about whether your business can keep operating when any cloud fails.
The Real Issue: Over-Dependency Without a Backup Plan
Three big problems were exposed.
Most organizations don’t have a way to function without their primary cloud provider. They have redundancy inside AWS or Azure, but nothing outside.
We’ve mistaken segmentation for resilience. Zoning, VPCs, and multi-AZ architectures are valuable, but they don’t protect against failures in DNS, identity, or control plane systems at the provider.
Business continuity hasn’t evolved at the same pace as cloud adoption. We moved applications, identity, and data to the cloud, but we never built an exit ramp for when the cloud is the problem.
What CIOs, CISOs, and IT Directors Should Be Doing Now
1. Map All Dependencies
Not just your servers. Look at identity, authentication, DNS, APIs, SaaS platforms, payments, analytics, HR systems, payroll tools. If it stops working when AWS or Azure is down, it’s a dependency you need to know about.
2. Build Continuity Outside the Cloud Provider
That could mean a secondary provider like Google Cloud or Azure, on-prem hardware, or private infrastructure for core workloads. It could include secondary DNS, offline authentication modes, or replicated data stores that aren’t tied to a single vendor.
3. Test What Happens During Failure
Run real-tabletop exercises. If AWS goes down at 10 a.m., what do you do in the first hour? Can you authenticate employees? Take payments? Access critical data? Communicate with customers and leadership?
4. Explain This Clearly to Executives
Don’t sell panic. Sell transparency and readiness.
Cloud is still the right strategy, but it isn’t immune to failure. Our goal isn’t to move away from AWS or Azure. It’s to make sure we can keep working when they don’t.
This isn’t only an IT problem. It’s business continuity.
Final Thought
Cloud is still the best place to build, scale, and secure modern systems. But uptime isn’t guaranteed. The AWS outage wasn’t a random glitch. It proved that cloud dependency without continuity is a business risk.
Some organizations stayed online. Others waited in the dark. The difference wasn’t budget or size. It was planning.
The new measure of IT leadership isn’t how well things run on a good day. It’s how well they run when the cloud isn’t there.
Zero-Day Attacks and Why Every Business Needs MSSP Protection
In 2025, zero-day attacks remain one of the most formidable cyberthreats organizations face. A zero-day attack exploits a software, hardware, or firmware vulnerability unknown to the vendor and for which no patch or fix is available.
In 2025, zero-day attacks remain one of the most formidable cyberthreats organizations face. A zero-day attack exploits a software, hardware, or firmware vulnerability unknown to the vendor and for which no patch or fix is available. Attackers leverage these undisclosed vulnerabilities before security teams have any opportunity to prepare or defend against them, making zero-day exploits highly effective and dangerous.
What are Zero-Day Attacks?
Zero-day vulnerability: A flaw or weakness in software or hardware that is unknown to vendors and without a current fix.
Zero-day exploit: The attack method malicious actors use to take advantage of the vulnerability.
Zero-day attack: When attackers successfully exploit the zero-day vulnerability to gain unauthorized access, steal data, or cause damage.
These attacks are particularly severe because they provide no warning or defense window, often giving attackers the ability to move freely inside a network and cause serious harm, from data theft to disruption of critical systems.
Why Zero-Day Attacks Are So Dangerous
Unknown and Unpatched Vulnerabilities: No immediate fix or signature exists to detect or prevent the attack.
Targeted and Sophisticated: Attackers can design exploits that evade traditional security tools.
Potential for Widespread Damage: The window between vulnerability discovery and patch release is exploited aggressively.
High Impact: Can lead to data breaches, ransomware infections, intellectual property theft, and long-term damage to business reputation.
How MSSPs Proactively Defend Against Zero-Day Attacks
1. Behavioral Analytics and Anomaly Detection
MSSPs use advanced User and Entity Behavior Analytics (UEBA) and machine learning to detect abnormal patterns in user activities and endpoint behaviors indicative of zero-day exploitation attempts.
2. Endpoint Detection and Response (EDR)
Modern EDR tools provide real-time monitoring, threat hunting, and automated containment capabilities that can identify and isolate suspicious processes or lateral movement behaviors arising from zero-day attacks.
3. Threat Intelligence Integration
MSSPs leverage global, real-time threat intelligence feeds to identify emerging zero-day activity, Indicators of Compromise (IoCs), and updated threat actor tactics to quickly respond and adapt defenses.
4. Security Orchestration, Automation, and Response (SOAR)
Automated workflows allow MSSPs to respond rapidly to detected threats, containing zero-day intrusions and minimizing damage while analysts investigate.
5. Network Segmentation and Zero Trust Architecture
MSSPs implement robust network segmentation and zero trust models to limit attackers' lateral movement, reducing the impact of zero-day breaches.
6. Continuous Patch and Vulnerability Management
Although zero-days are unknown vulnerabilities, MSSPs ensure that all known patches and security configurations are up to date, closing other attack avenues that zero-day exploits may try to use.
Conclusion
Zero-day attacks exploit unknown vulnerabilities, offering attackers a significant advantage. Traditional security solutions reliant on known threat signatures are insufficient against such stealthy and sophisticated attacks. MSSPs bring the technology, expertise, and proactive strategies necessary to detect, contain, and mitigate zero-day threats effectively.
Partnering with an MSSP like CyberSecOp ensures a resilient defense posture, employing cutting-edge behavioral analytics, threat intelligence, automated response, and comprehensive endpoint protection to safeguard your business from emerging threats—even before patches exist.
Protect Your Business from Zero-Day Attacks with CyberSecOp
Stay ahead of zero-day threats with CyberSecOp’s expert managed security services designed to detect and respond to advanced cyberattacks in real time.
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com
The Evolution of Insider Threats: How MSSPs Detect and Prevent Employee-Based Attacks
Insider threats have emerged as one of the most costly and complex cybersecurity risks in 2025. According to recent industry research, insider incidents cost businesses an average of $17.4 million annually, with credential theft accounting for the highest per-incident expense—nearly $780,000.
Insider threats have emerged as one of the most costly and complex cybersecurity risks in 2025. According to recent industry research, insider incidents cost businesses an average of $17.4 million annually, with credential theft accounting for the highest per-incident expense—nearly $780,000. As organizations grapple with hybrid work models, sprawling cloud environments, and an influx of SaaS tools, the risk from insiders—whether malicious or negligent—is becoming increasingly significant.
Why Insider Threats Are Growing
Expanded IT Complexity: The dissolution of traditional network perimeters, combined with hybrid work, makes monitoring insider activities more challenging.
Human Element: Insider threats often arise from misconduct, negligence, or stolen credentials. Studies show insiders contribute to over 45% of data breaches.
AI-Driven Sophistication: Adversaries are also weaponizing AI to scale and refine insider attacks.
Negligent and Malicious Insiders: Both types cause significant damage, from accidental data leaks to deliberate sabotage or theft.
How MSSPs Use Behavioral Analytics to Detect Suspicious Activities
1. Continuous User and Entity Behavior Monitoring
MSSPs deploy advanced User and Entity Behavior Analytics (UEBA) tools to monitor normal user activity baselines and detect anomalies such as unusual login times, data access patterns, or privilege escalations.
2. Real-Time Anomaly Detection and Alerting
By applying machine learning algorithms, MSSPs identify deviations from typical behavior in real time, triggering immediate alerts for potential insider incidents.
3. Risk Scoring and Prioritization
Risk scores based on behavioral factors, combined with access context (location, device, role), allow MSSPs to prioritize incidents, reducing alert fatigue and focusing attention on high-risk activities.
4. Integration with Human Resources and Security Systems
MSSPs correlate behavioral analytics with HR data (such as recent terminations or role changes) to enhance detection accuracy and response strategies.
5. Automated and Guided Incident Response
Once suspicious behavior is detected, MSSPs automate containment actions—such as session termination, account suspension, or access revocation—while providing security teams with detailed forensic evidence to investigate.
6. Continuous Improvement Through AI
Artificial intelligence models refine detection capabilities by learning from new data, adjusting thresholds, and reducing false positives, balancing security with operational continuity.
The Business Value of MSSP-Driven Insider Threat Programs
Reduced Incident Costs: Rapid detection and response reduce breach duration and financial impact.
Improved Regulatory Compliance: Demonstrates proactive insider risk management for audits and legal requirements.
Stronger Security Posture: Safeguards intellectual property, customer data, and operational continuity.
Employee Trust and Culture: Detection paired with training reinforces positive security behaviors.
Conclusion
Insider threats present an evolving and significant challenge, fueled by technology complexity, human factors, and AI-enhanced adversaries. MSSPs leverage behavioral analytics and AI-driven detection to provide comprehensive insider threat management, enabling organizations to detect, respond to, and prevent malicious or negligent insider activities effectively.
Protect Your Organization from Insider Threats with CyberSecOp
Gain peace of mind with CyberSecOp’s expert insider threat detection and prevention services powered by behavioral analytics and AI.
Customer Service: 1 866-973-2677
Sales: Sales@CyberSecOp.com