Cybersecurity threats from hacktivists, criminals, and hostile nation states are enough to keep government officials, businesses, and consumers up at night. These attacks are growing in sophistication and frequency and pose serious threats to our national and economic security.
Everyone impacted by these vicious and dangerous acts must work together to help prevent, protect against, and effectively respond to them.
What are the biggest cyber threats CISOs are worried about in 2019? In today's age of breaches, staying ahead of cyber threats is becoming more critical than ever. Dive into how organizations are addressing the threat of cyber attacks, how they are measuring risk, and what they are doing about improving security from some of the top experts in the field.
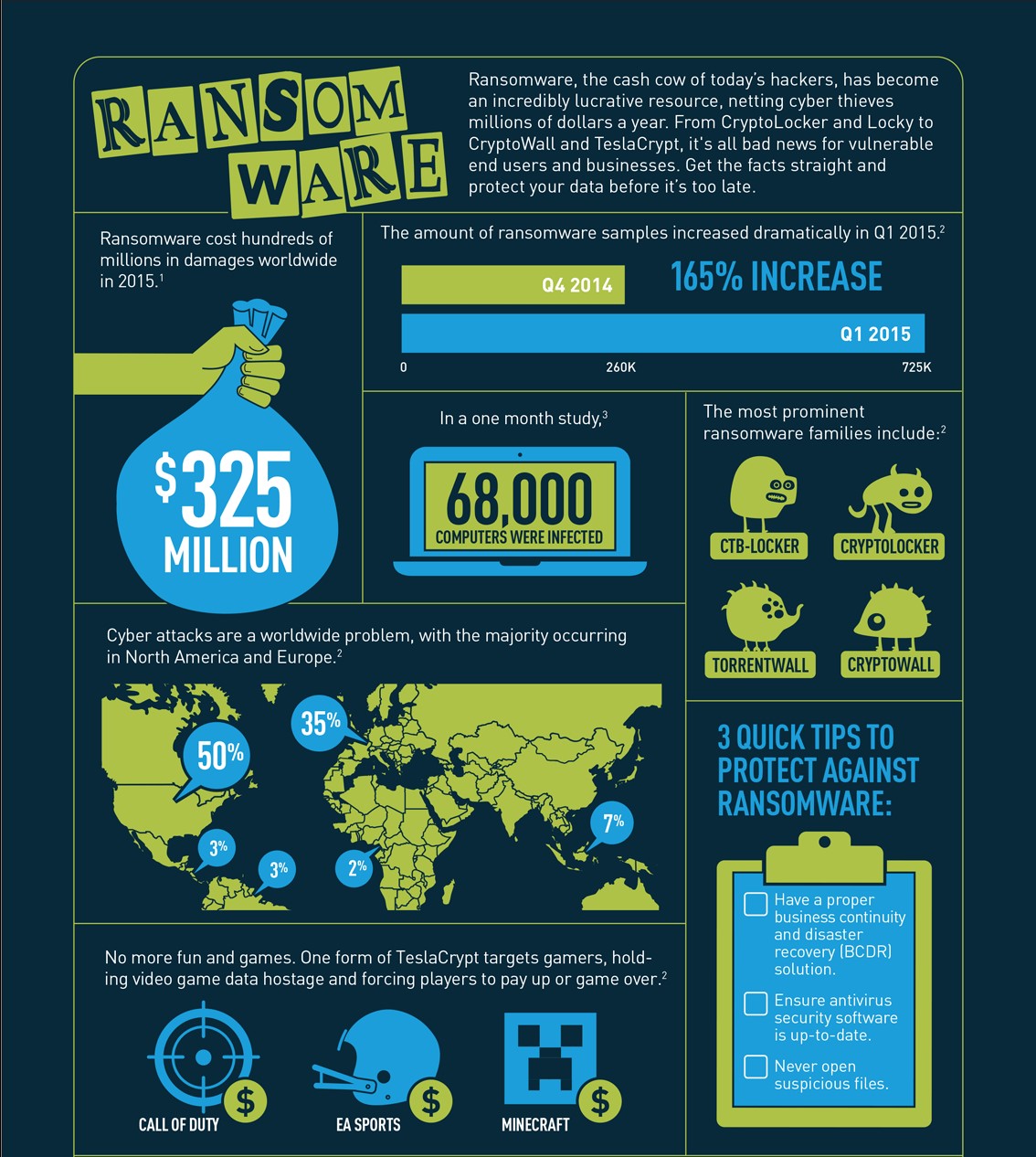
Ransomware is still a large risk, affecting a large number of businesses
Data Loss and Data Breach based on information available on dark web, proves that organization can’t protect customers data.
Small business with no security program are at risk more than large organization.
All industry need to have some type of cyber regulations based on secure standards such as NIST or ISO.
What can business do, to enable a stronger security posture in their enterprise
Businesses adopt standalone cyber insurance policies as boards and executives wake up to cyber liability. As boards and executives experience and witness the impact of cyber attacks, including reduced earnings, operational disruption, and claims brought against directors and officers, businesses will turn to tailored enterprise cyber insurance policies, rather than relying on “silent” components in other policies. Adoption will spread beyond traditional buyers of cyber insurance, such as retail, financial, and healthcare sectors, to others vulnerable to cyber-related business disruption, including manufacturing, transportation, utility, and oil and gas.
As the physical and cyber worlds collide, chief risk officers take center stage to manage cyber as an enterprise risk. As sophisticated cyber attacks generate real-world consequences that impact business operations at increasing scale, C-suites will wake up to the enterprise nature of cyber risk. In 2018, expect CROs to have a seat at the cyber table, working closely with chief information security officers (CISOs) to help organizations understand the holistic impact of cyber risk on the business.
Regulatory spotlight widens and becomes more complex, provoking calls for harmonization. EU holds global companies to account over General Data Protection Regulation (GDPR) violation; big data aggregators come under scrutiny in the U.S. In 2018, regulators at the international, national and local levels will more strictly enforce existing cybersecurity regulations and introduce new regulations. Expect to see EU regulators holding major U.S. and global companies to account for GDPR violations. Across the Atlantic, big data organizations (aggregators and resellers) will come under scrutiny on how they are collecting, using, and securing data. Industry organizations will push back on regulators, calling for alignment of cyber regulations.
Criminals look to attack businesses embracing the Internet of Things, in particular targeting small to mid-sized businesses providing services to global organizations. In 2018, global organizations will need to consider the increased complexities when it comes to how businesses are using the IoT in relation to third-party risk management. The report predicts large companies will be brought down by an attack on a small vendor or contractor that targets the IoT, using it as a way into their network. This will serve as a wake-up call for large organizations to update their third-party risk management, and for small and mid-sized businesses to implement better security measures or risk losing business.
As passwords continue to be hacked, and attackers circumvent physical biometrics, multi-factor authentication becomes more important than ever before. Beyond passwords, companies are implementing new methods of authentication – from facial recognition to fingerprints. However, these technologies are still vulnerable and as such, the report anticipates that a new wave of companies will embrace multi-factor authentication to combat the assault on passwords and attacks targeting biometrics. This will require individuals to present several pieces of evidence to an authentication instrument. With the new need for multi-factor authentication, and consumer demand for unobtrusive layers of security, expect to see the implementation of behavioral biometrics.
Criminals will target transactions that use reward points as currency, spurring mainstream adoption of bug bounty programs: Companies beyond the technology, government, automotive and financial services sectors will introduce bug bounty platforms into their security programs. As criminals target transactions that use points as currency, businesses with loyalty, gift and rewards programs –such as airlines, retailers, and hospitality providers– will be the next wave of companies implementing bug bounty programs. As more organizations adopt the programs, they will require support from external experts to avoid introducing new risks with improperly configured programs.
Ransomware attackers get targeted; crypto currencies help ransomware industry flourish. In 2018, ransomware criminals will evolve their tactics. The reports predicts that attackers utilizing forms of benign malware—such as software designed to cause DDoS attacks or launch display ads on thousands of systems— will launch huge outbreaks of ransomware. While attackers will continue to launch scatter-gun-style attacks to disrupt as many systems as possible, the report predicts an increase in instances of attacks targeting specific companies and demanding ransomware payments proportional to the value of the encrypted assets. Crypto currencies will continue to support the flourishing ransomware industry overall, despite law enforcement becoming more advanced in their ability to trace attacks, for example through bitcoin wallets.
Insider risks plague organizations as they underestimate their severe vulnerability and liability while major attacks fly under the radar. In 2017, businesses under invested in proactive insider risk mitigation strategies, and 2018 will be no different. According to the report, a continued lack of security training and technical controls, coupled with the changing dynamics of the modern workforce, the full extent of cyber attacks and incidents caused by insiders will not become fully public. Many companies will continue to reactively responding to incidents behind closed doors and remain unaware of the true cost and impact of insider risk on the organization.